#include "ob_x.h"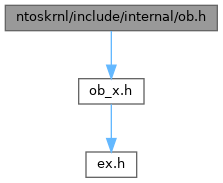
Go to the source code of this file.
Classes | |
| struct | _OBP_SET_HANDLE_ATTRIBUTES_CONTEXT |
| struct | _OBP_CLOSE_HANDLE_CONTEXT |
| struct | _OBP_FIND_HANDLE_DATA |
| struct | _SECURITY_DESCRIPTOR_HEADER |
| struct | _OB_SD_CACHE_LIST |
| union | ALIGNEDNAME |
| struct | _OB_TEMP_BUFFER |
Macro Definition Documentation
◆ _OB_DEBUG_
◆ GENERIC_ACCESS
| #define GENERIC_ACCESS |
◆ KERNEL_HANDLE_FLAG
◆ OB_CALLBACK_DEBUG
◆ OB_HANDLE_DEBUG
◆ OB_NAMESPACE_DEBUG
◆ OB_REFERENCE_DEBUG
◆ OB_SECURITY_DEBUG
◆ OBJ_AUDIT_OBJECT_CLOSE
◆ OBJ_HANDLE_ATTRIBUTES
| #define OBJ_HANDLE_ATTRIBUTES |
◆ OBJ_PROTECT_CLOSE
◆ ObKernelHandleToHandle
◆ ObMarkHandleAsKernelHandle
◆ OBP_SYSTEM_PROCESS_QUOTA
| #define OBP_SYSTEM_PROCESS_QUOTA ((PEPROCESS_QUOTA_BLOCK)(ULONG_PTR)1) |
◆ ObpAccessProtectCloseBit
◆ ObpGetHandleObject
| #define ObpGetHandleObject | ( | x | ) | ((POBJECT_HEADER)((ULONG_PTR)x->Object & ~OBJ_HANDLE_ATTRIBUTES)) |
◆ ObpGetHeaderForEntry
| #define ObpGetHeaderForEntry | ( | x | ) | CONTAINING_RECORD((x), SECURITY_DESCRIPTOR_HEADER, Link) |
◆ ObpGetHeaderForSd
| #define ObpGetHeaderForSd | ( | x | ) | CONTAINING_RECORD((x), SECURITY_DESCRIPTOR_HEADER, SecurityDescriptor) |
◆ ObpIsKernelHandle
◆ OBTRACE
◆ TAG_OB_TEMP_STORAGE
Typedef Documentation
◆ OB_SD_CACHE_LIST
| typedef struct _OB_SD_CACHE_LIST OB_SD_CACHE_LIST |
◆ OB_TEMP_BUFFER
| typedef struct _OB_TEMP_BUFFER OB_TEMP_BUFFER |
◆ OBP_CLOSE_HANDLE_CONTEXT
◆ OBP_FIND_HANDLE_DATA
◆ OBP_SET_HANDLE_ATTRIBUTES_CONTEXT
◆ POB_SD_CACHE_LIST
| typedef struct _OB_SD_CACHE_LIST * POB_SD_CACHE_LIST |
◆ POB_TEMP_BUFFER
| typedef struct _OB_TEMP_BUFFER * POB_TEMP_BUFFER |
◆ POBP_CLOSE_HANDLE_CONTEXT
◆ POBP_FIND_HANDLE_DATA
| typedef struct _OBP_FIND_HANDLE_DATA * POBP_FIND_HANDLE_DATA |
◆ POBP_SET_HANDLE_ATTRIBUTES_CONTEXT
◆ PSECURITY_DESCRIPTOR_HEADER
◆ SECURITY_DESCRIPTOR_HEADER
Function Documentation
◆ ObAssignObjectSecurityDescriptor()
| NTSTATUS NTAPI ObAssignObjectSecurityDescriptor | ( | IN PVOID | Object, |
| IN PSECURITY_DESCRIPTOR SecurityDescriptor | OPTIONAL, | ||
| IN POOL_TYPE | PoolType | ||
| ) |
Definition at line 20 of file obsecure.c.
Referenced by SeDefaultObjectMethod(), and WmipSecurityMethod().
◆ ObCheckCreateObjectAccess()
| BOOLEAN NTAPI ObCheckCreateObjectAccess | ( | IN PVOID | Object, |
| IN ACCESS_MASK | CreateAccess, | ||
| IN PACCESS_STATE | AccessState, | ||
| IN PUNICODE_STRING | ComponentName, | ||
| IN BOOLEAN | LockHeld, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| OUT PNTSTATUS | AccessStatus | ||
| ) |
Definition at line 203 of file obsecure.c.
Referenced by ObpLookupObjectName().
◆ ObCheckObjectAccess()
| BOOLEAN NTAPI ObCheckObjectAccess | ( | IN PVOID | Object, |
| IN OUT PACCESS_STATE | AccessState, | ||
| IN BOOLEAN | LockHeld, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| OUT PNTSTATUS | ReturnedStatus | ||
| ) |
Definition at line 441 of file obsecure.c.
Referenced by CmpDoOpen(), and ObpIncrementHandleCount().
◆ ObClearProcessHandleTable()
Definition at line 2027 of file obhandle.c.
Referenced by NtTerminateProcess(), and PspTerminateProcess().
◆ ObDeassignSecurity()
| NTSTATUS NTAPI ObDeassignSecurity | ( | IN OUT PSECURITY_DESCRIPTOR * | SecurityDescriptor | ) |
Definition at line 60 of file obsecure.c.
Referenced by SeDefaultObjectMethod(), and WmipSecurityMethod().
◆ ObDereferenceDeviceMap()
Definition at line 456 of file devicemap.c.
Referenced by PspDeleteProcess(), and PspSetPrimaryToken().
◆ ObDereferenceObjectEx()
Definition at line 88 of file obref.c.
Referenced by ExpTimerApcKernelRoutine(), ExTimerRundown(), NtCancelTimer(), NtSetTimer(), ObFastReferenceObject(), ObFastReplaceObject(), and PspCreateThread().
◆ ObDereferenceProcessHandleTable()
Definition at line 48 of file obhandle.c.
Referenced by ObClearProcessHandleTable(), ObDuplicateObject(), ObFindHandleForObject(), ObGetProcessHandleCount(), and ObInitProcess().
◆ ObDuplicateObject()
| NTSTATUS NTAPI ObDuplicateObject | ( | IN PEPROCESS | SourceProcess, |
| IN HANDLE | SourceHandle, | ||
| IN PEPROCESS TargetProcess | OPTIONAL, | ||
| IN PHANDLE TargetHandle | OPTIONAL, | ||
| IN ACCESS_MASK | DesiredAccess, | ||
| IN ULONG | HandleAttributes, | ||
| IN ULONG | Options, | ||
| IN KPROCESSOR_MODE | PreviousMode | ||
| ) |
Definition at line 2204 of file obhandle.c.
Referenced by DbgkpOpenHandles(), and NtDuplicateObject().
◆ ObFastDereferenceObject()
Definition at line 167 of file obref.c.
Referenced by PsImpersonateClient(), PspCreateProcess(), PspCreateThread(), PspExitThread(), PspInitializeProcessSecurity(), PspSetPrimaryToken(), SeIsTokenChild(), SeIsTokenSibling(), SepImpersonateAnonymousToken(), SepOpenThreadToken(), and SeReleaseSubjectContext().
◆ ObFastReferenceObject()
| PVOID FASTCALL ObFastReferenceObject | ( | IN PEX_FAST_REF | FastRef | ) |
Definition at line 132 of file obref.c.
Referenced by PsReferenceEffectiveToken(), and PsReferencePrimaryToken().
◆ ObFastReferenceObjectLocked()
| PVOID FASTCALL ObFastReferenceObjectLocked | ( | IN PEX_FAST_REF | FastRef | ) |
Definition at line 119 of file obref.c.
Referenced by PsReferenceEffectiveToken(), and PsReferencePrimaryToken().
◆ ObFastReplaceObject()
Referenced by SeDeassignPrimaryToken(), and SeExchangePrimaryToken().
◆ ObfDereferenceDeviceMap()
| VOID FASTCALL ObfDereferenceDeviceMap | ( | IN PDEVICE_MAP | DeviceMap | ) |
Definition at line 477 of file devicemap.c.
Referenced by ObDereferenceDeviceMap(), ObpLookupObjectName(), ObpSetCurrentProcessDeviceMap(), ObQueryDeviceMapInformation(), ObSetDeviceMap(), SeGetLogonIdDeviceMap(), SepRmDeleteLogonSession(), and SepRmDereferenceLogonSession().
◆ ObFreeObjectCreateInfoBuffer()
| VOID NTAPI ObFreeObjectCreateInfoBuffer | ( | IN POBJECT_CREATE_INFORMATION | ObjectCreateInfo | ) |
Definition at line 603 of file oblife.c.
Referenced by IoCreateStreamFileObjectLite().
◆ ObGetProcessHandleCount()
Definition at line 56 of file obhandle.c.
Referenced by NtQueryInformationProcess(), and QSI_DEF().
◆ ObInheritDeviceMap()
Definition at line 511 of file devicemap.c.
Referenced by PspCreateProcess().
◆ ObInitializeFastReference()
Definition at line 107 of file obref.c.
Referenced by PspInitializeProcessSecurity(), SeAssignPrimaryToken(), and SepInitializationPhase0().
◆ ObInitProcess()
Definition at line 2090 of file obhandle.c.
Referenced by PspCreateProcess().
◆ ObInitSystem()
Definition at line 203 of file obinit.c.
Referenced by ExpInitializeExecutive(), and Phase1InitializationDiscard().
◆ ObIsLUIDDeviceMapsEnabled()
Definition at line 662 of file devicemap.c.
Referenced by NtQueryInformationProcess(), and PspSetPrimaryToken().
◆ ObKillProcess()
Definition at line 2160 of file obhandle.c.
Referenced by PspDeleteProcess(), and PspExitThread().
◆ ObpCaptureObjectCreateInformation()
| NTSTATUS NTAPI ObpCaptureObjectCreateInformation | ( | IN POBJECT_ATTRIBUTES | ObjectAttributes, |
| IN KPROCESSOR_MODE | AccessMode, | ||
| IN KPROCESSOR_MODE | CreatorMode, | ||
| IN BOOLEAN | AllocateFromLookaside, | ||
| IN POBJECT_CREATE_INFORMATION | ObjectCreateInfo, | ||
| OUT PUNICODE_STRING | ObjectName | ||
| ) |
Definition at line 455 of file oblife.c.
Referenced by ObCreateObject(), and ObOpenObjectByName().
◆ ObpCaptureObjectName()
| NTSTATUS NTAPI ObpCaptureObjectName | ( | IN PUNICODE_STRING | CapturedName, |
| IN PUNICODE_STRING | ObjectName, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| IN BOOLEAN | AllocateFromLookaside | ||
| ) |
Referenced by ObReferenceObjectByName().
◆ ObpCheckObjectReference()
| BOOLEAN NTAPI ObpCheckObjectReference | ( | IN PVOID | Object, |
| IN OUT PACCESS_STATE | AccessState, | ||
| IN BOOLEAN | LockHeld, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| OUT PNTSTATUS | AccessStatus | ||
| ) |
Definition at line 340 of file obsecure.c.
Referenced by ObReferenceObjectByName().
◆ ObpCheckTraverseAccess()
| BOOLEAN NTAPI ObpCheckTraverseAccess | ( | IN PVOID | Object, |
| IN ACCESS_MASK | TraverseAccess, | ||
| IN PACCESS_STATE AccessState | OPTIONAL, | ||
| IN BOOLEAN | LockHeld, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| OUT PNTSTATUS | AccessStatus | ||
| ) |
Definition at line 267 of file obsecure.c.
Referenced by ObpLookupObjectName().
◆ ObpCreateDosDevicesDirectory()
Definition at line 177 of file obname.c.
Referenced by ObInitSystem().
◆ ObpCreateSymbolicLinkName()
| VOID NTAPI ObpCreateSymbolicLinkName | ( | IN POBJECT_SYMBOLIC_LINK | SymbolicLink | ) |
Definition at line 334 of file oblink.c.
Referenced by ObInsertObject().
◆ ObpDeleteEntryDirectory()
| BOOLEAN NTAPI ObpDeleteEntryDirectory | ( | IN POBP_LOOKUP_CONTEXT | Context | ) |
Referenced by ObpDeleteNameCheck().
◆ ObpDeleteNameCheck()
Definition at line 301 of file obname.c.
Referenced by ObInsertObject(), ObpDecrementHandleCount(), and ObpSetPermanentObject().
◆ ObpDeleteObject()
Definition at line 147 of file oblife.c.
Referenced by ObfDereferenceObject(), and ObpReapObject().
◆ ObpDeleteObjectType()
Definition at line 1417 of file oblife.c.
Referenced by ObInitSystem().
◆ ObpDeleteSymbolicLink()
Referenced by ObInitSystem().
◆ ObpDeleteSymbolicLinkName()
| VOID NTAPI ObpDeleteSymbolicLinkName | ( | IN POBJECT_SYMBOLIC_LINK | SymbolicLink | ) |
Definition at line 326 of file oblink.c.
Referenced by ObpDeleteNameCheck().
◆ ObpFreeObjectNameBuffer()
| VOID NTAPI ObpFreeObjectNameBuffer | ( | IN PUNICODE_STRING | Name | ) |
Definition at line 346 of file oblife.c.
Referenced by ObCreateObject(), ObOpenObjectByName(), ObpCaptureObjectName(), and ObReferenceObjectByName().
◆ ObpInitSdCache()
Definition at line 61 of file obsdcach.c.
Referenced by ObInitSystem().
◆ ObpInsertEntryDirectory()
| BOOLEAN NTAPI ObpInsertEntryDirectory | ( | IN POBJECT_DIRECTORY | Parent, |
| IN POBP_LOOKUP_CONTEXT | Context, | ||
| IN POBJECT_HEADER | ObjectHeader | ||
| ) |
Definition at line 45 of file obdir.c.
Referenced by ObCreateObjectType(), ObInitSystem(), and ObpLookupObjectName().
◆ ObpLookupEntryDirectory()
| PVOID NTAPI ObpLookupEntryDirectory | ( | IN POBJECT_DIRECTORY | Directory, |
| IN PUNICODE_STRING | Name, | ||
| IN ULONG | Attributes, | ||
| IN BOOLEAN | SearchShadow, | ||
| IN POBP_LOOKUP_CONTEXT | Context | ||
| ) |
Definition at line 158 of file obdir.c.
Referenced by ObCreateObjectType(), ObInitSystem(), ObpDeleteNameCheck(), ObpLookupObjectName(), and ObpProcessDosDeviceSymbolicLink().
◆ ObpLookupObjectName()
| NTSTATUS NTAPI ObpLookupObjectName | ( | IN HANDLE RootHandle | OPTIONAL, |
| IN OUT PUNICODE_STRING | ObjectName, | ||
| IN ULONG | Attributes, | ||
| IN POBJECT_TYPE | ObjectType, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| IN OUT PVOID | ParseContext, | ||
| IN PSECURITY_QUALITY_OF_SERVICE SecurityQos | OPTIONAL, | ||
| IN PVOID InsertObject | OPTIONAL, | ||
| IN OUT PACCESS_STATE | AccessState, | ||
| OUT POBP_LOOKUP_CONTEXT | LookupContext, | ||
| OUT PVOID * | FoundObject | ||
| ) |
Definition at line 446 of file obname.c.
Referenced by ObInsertObject(), ObOpenObjectByName(), and ObReferenceObjectByName().
◆ ObpParseSymbolicLink()
| NTSTATUS NTAPI ObpParseSymbolicLink | ( | IN PVOID | ParsedObject, |
| IN PVOID | ObjectType, | ||
| IN OUT PACCESS_STATE | AccessState, | ||
| IN KPROCESSOR_MODE | AccessMode, | ||
| IN ULONG | Attributes, | ||
| IN OUT PUNICODE_STRING | FullPath, | ||
| IN OUT PUNICODE_STRING | RemainingName, | ||
| IN OUT PVOID Context | OPTIONAL, | ||
| IN PSECURITY_QUALITY_OF_SERVICE SecurityQos | OPTIONAL, | ||
| OUT PVOID * | NextObject | ||
| ) |
Definition at line 431 of file oblink.c.
Referenced by ObInitSystem(), and ObpLookupObjectName().
◆ ObpReapObject()
Definition at line 220 of file oblife.c.
Referenced by ObInitSystem().
◆ ObpReferenceDeviceMap()
| PDEVICE_MAP NTAPI ObpReferenceDeviceMap | ( | VOID | ) |
Definition at line 325 of file devicemap.c.
Referenced by ObpLookupObjectName(), and ObQueryDeviceMapInformation().
◆ ObpReferenceSecurityDescriptor()
| PSECURITY_DESCRIPTOR NTAPI ObpReferenceSecurityDescriptor | ( | IN POBJECT_HEADER | ObjectHeader | ) |
Definition at line 181 of file obsdcach.c.
Referenced by ObGetObjectSecurity(), ObQuerySecurityDescriptorInfo(), and ObSetSecurityDescriptorInfo().
◆ ObpSetHandleAttributes()
| BOOLEAN NTAPI ObpSetHandleAttributes | ( | IN OUT PHANDLE_TABLE_ENTRY | HandleTableEntry, |
| IN ULONG_PTR | Context | ||
| ) |
Definition at line 1859 of file obhandle.c.
Referenced by NtSetInformationObject(), and ObSetHandleAttributes().
◆ ObpSetPermanentObject()
Definition at line 266 of file oblife.c.
Referenced by NtMakePermanentObject(), NtMakeTemporaryObject(), and ObMakeTemporaryObject().
◆ ObQueryDeviceMapInformation()
| NTSTATUS NTAPI ObQueryDeviceMapInformation | ( | _In_opt_ PEPROCESS | Process, |
| _Out_ PPROCESS_DEVICEMAP_INFORMATION | DeviceMapInfo, | ||
| _In_ ULONG | Flags | ||
| ) |
Definition at line 539 of file devicemap.c.
Referenced by NtQueryInformationProcess().
◆ ObQuerySecurityDescriptorInfo()
| NTSTATUS NTAPI ObQuerySecurityDescriptorInfo | ( | IN PVOID | Object, |
| IN PSECURITY_INFORMATION | SecurityInformation, | ||
| OUT PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| IN OUT PULONG | Length, | ||
| IN PSECURITY_DESCRIPTOR * | OutputSecurityDescriptor | ||
| ) |
Definition at line 85 of file obsecure.c.
Referenced by SeDefaultObjectMethod(), and WmipSecurityMethod().
◆ ObReferenceFileObjectForWrite()
| NTSTATUS NTAPI ObReferenceFileObjectForWrite | ( | IN HANDLE | Handle, |
| IN KPROCESSOR_MODE | AccessMode, | ||
| OUT PFILE_OBJECT * | FileObject, | ||
| OUT POBJECT_HANDLE_INFORMATION | HandleInformation | ||
| ) |
Definition at line 200 of file obref.c.
Referenced by NtWriteFile().
◆ ObReferenceObjectEx()
Definition at line 77 of file obref.c.
Referenced by ObFastReferenceObject(), ObFastReplaceObject(), ObInitializeFastReference(), and PspCreateThread().
◆ ObReferenceObjectSafe()
Definition at line 22 of file obref.c.
Referenced by _Function_class_(), CmpFlushNotifiesOnKeyBodyList(), NtImpersonateClientOfPort(), NtRequestPort(), PsGetNextProcess(), PsGetNextProcessThread(), PsLookupProcessByProcessId(), PsLookupProcessThreadByCid(), PsLookupThreadByThreadId(), PspExitThread(), and SepCleanupLUIDDeviceMapDirectory().
◆ ObReferenceProcessHandleTable()
| PHANDLE_TABLE NTAPI ObReferenceProcessHandleTable | ( | IN PEPROCESS | Process | ) |
Definition at line 26 of file obhandle.c.
Referenced by ObClearProcessHandleTable(), ObDuplicateObject(), ObFindHandleForObject(), ObGetProcessHandleCount(), and ObInitProcess().
◆ ObSetDeviceMap()
Definition at line 24 of file devicemap.c.
Referenced by NtSetInformationProcess(), and ObpCreateDosDevicesDirectory().
◆ ObSetDirectoryDeviceMap()
Definition at line 149 of file devicemap.c.
Referenced by SeGetLogonIdDeviceMap().
◆ ObSetSecurityDescriptorInfo()
| NTSTATUS NTAPI ObSetSecurityDescriptorInfo | ( | IN PVOID | Object, |
| IN PSECURITY_INFORMATION | SecurityInformation, | ||
| IN OUT PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| IN OUT PSECURITY_DESCRIPTOR * | OutputSecurityDescriptor, | ||
| IN POOL_TYPE | PoolType, | ||
| IN PGENERIC_MAPPING | GenericMapping | ||
| ) |
Definition at line 117 of file obsecure.c.
Referenced by SeDefaultObjectMethod(), and WmipSecurityMethod().
◆ ObShutdownSystem()
Variable Documentation
◆ IoCountOperations
|
extern |
Definition at line 38 of file iomgr.c.
Referenced by IopUpdateOperationCount(), and IopUpdateTransferCount().
◆ ObpCaseInsensitive
|
extern |
Definition at line 18 of file obname.c.
Referenced by ObpLookupObjectName().
◆ ObpCreateInfoLookasideList
| GENERAL_LOOKASIDE ObpCreateInfoLookasideList |
Definition at line 644 of file ob.h.
Referenced by ObInit2(), and ObInitSystem().
◆ ObpDefaultObject
|
extern |
Definition at line 23 of file oblife.c.
Referenced by ObCreateObjectType().
◆ ObpDeviceMapLock
|
extern |
Definition at line 24 of file oblife.c.
Referenced by ObDereferenceDeviceMap(), ObfDereferenceDeviceMap(), ObInheritDeviceMap(), ObInitSystem(), ObpGetShadowDirectory(), ObpProcessDosDeviceSymbolicLink(), ObpReferenceDeviceMap(), ObpSetCurrentProcessDeviceMap(), ObQueryDeviceMapInformation(), ObSetDeviceMap(), and ObSetDirectoryDeviceMap().
◆ ObpDirectoryObjectType
|
extern |
Definition at line 20 of file obdir.c.
Referenced by NtCreateDirectoryObject(), NtOpenDirectoryObject(), and NtQueryDirectoryObject().
◆ ObpDosDevicesShortName
|
extern |
Definition at line 25 of file obname.c.
Referenced by ObpLookupObjectName(), and ObpProcessDosDeviceSymbolicLink().
◆ ObpDosDevicesShortNamePrefix
|
extern |
Definition at line 23 of file obname.c.
Referenced by ObpLookupObjectName(), and ObpProcessDosDeviceSymbolicLink().
◆ ObpDosDevicesShortNameRoot
|
extern |
Definition at line 24 of file obname.c.
Referenced by ObpCreateDosDevicesDirectory(), and ObpLookupObjectName().
◆ ObpKernelHandleTable
|
extern |
Definition at line 20 of file obhandle.c.
Referenced by NtSetInformationObject(), NtWaitForMultipleObjects(), ObInitSystem(), ObpCloseHandle(), ObpCreateHandle(), ObpCreateUnnamedHandle(), ObpReferenceProcessObjectByHandle(), ObQueryObjectAuditingByHandle(), ObReferenceFileObjectForWrite(), ObReferenceObjectByHandle(), and ObSetHandleAttributes().
◆ ObpLUIDDeviceMapsDisabled
|
extern |
Definition at line 17 of file devicemap.c.
Referenced by ObpCreateDosDevicesDirectory().
◆ ObpLUIDDeviceMapsEnabled
|
extern |
Definition at line 18 of file devicemap.c.
Referenced by ObIsLUIDDeviceMapsEnabled(), ObpCreateDosDevicesDirectory(), ObpLookupEntryDirectory(), ObpProcessDosDeviceSymbolicLink(), ObpReferenceDeviceMap(), and ObQueryDeviceMapInformation().
◆ ObpNameBufferLookasideList
|
extern |
Definition at line 26 of file oblife.c.
Referenced by ObInit2(), and ObInitSystem().
◆ ObpObjectSecurityMode
◆ ObpProtectionMode
|
extern |
Definition at line 57 of file obinit.c.
Referenced by ObpCreateDosDevicesDirectory(), and ObpGetDosDevicesProtection().
◆ ObpReaperList
Definition at line 29 of file oblife.c.
Referenced by ObpDeferObjectDeletion(), and ObpReapObject().
◆ ObpReaperWorkItem
|
extern |
Definition at line 28 of file oblife.c.
Referenced by ObInitSystem(), and ObpDeferObjectDeletion().
◆ ObpRootDirectoryObject
|
extern |
Definition at line 19 of file obname.c.
Referenced by ObInitSystem(), ObpLookupObjectName(), ObpProcessDosDeviceSymbolicLink(), and ObQueryNameString().
◆ ObpSymbolicLinkObjectType
|
extern |
Definition at line 19 of file oblink.c.
Referenced by NtCreateSymbolicLinkObject(), NtOpenSymbolicLinkObject(), NtQuerySymbolicLinkObject(), and ObpProcessDosDeviceSymbolicLink().
◆ ObpTraceLevel
◆ ObpTypeDirectoryObject
|
extern |
Definition at line 20 of file obname.c.
Referenced by ObCreateObjectType(), and ObInitSystem().
◆ ObpTypeObjectType
|
extern |
Definition at line 22 of file oblife.c.
Referenced by ObCreateObjectType().
◆ ObpUnsecureGlobalNamesBuffer
|
extern |
Definition at line 32 of file obname.c.
Referenced by ObpIsUnsecureName().