#include <umtypes.h>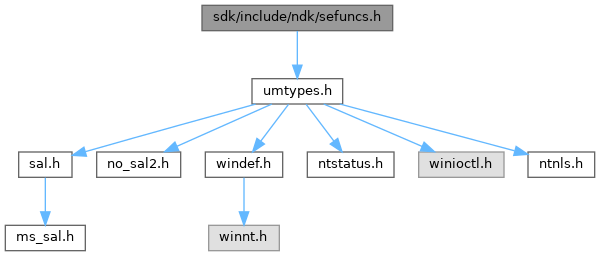

Go to the source code of this file.
Function Documentation
◆ _IRQL_requires_max_()
| _IRQL_requires_max_ | ( | PASSIVE_LEVEL | ) |
Queries information details about a security descriptor.
Computes the quota size of a security descriptor.
Assigns a security descriptor for a new object.
An extended function that assigns a security descriptor for a new object.
Frees a security descriptor.
An extended function that sets new information data to a security descriptor.
Modifies some information data about a security descriptor.
- Parameters
-
[in] SecurityInformation Security information details to be queried from a security descriptor. [out] SecurityDescriptor The returned security descriptor with security information data. [in,out] Length The returned length of a security descriptor. [in,out] ObjectsSecurityDescriptor The returned object security descriptor.
- Returns
- Returns STATUS_SUCCESS if the operations have been completed successfully and that the specific information about the security descriptor has been queried. STATUS_BUFFER_TOO_SMALL is returned if the buffer size is too small to contain the queried info about the security descriptor.
- Parameters
-
[in] Object If specified, the function will use this arbitrary object that points to an object security descriptor. [in] SecurityInformation Security information details to be set. [in] SecurityDescriptor A security descriptor where its info is to be changed. [in,out] ObjectsSecurityDescriptor The returned pointer to security descriptor objects. [in] PoolType Pool type for the new security descriptor to allocate. [in] GenericMapping The generic mapping of access rights masks.
- Returns
- See SeSetSecurityDescriptorInfoEx.
- Parameters
-
[in] Object If specified, the function will use this arbitrary object that points to an object security descriptor. [in] SecurityInformation Security information details to be set. [in] SecurityDescriptor A security descriptor where its info is to be changed. [in,out] ObjectsSecurityDescriptor The returned pointer to security descriptor objects. [in] AutoInheritFlags Flags bitmask inheritation, influencing how the security descriptor can be inherited and if it can be in the first place. [in] PoolType Pool type for the new security descriptor to allocate. [in] GenericMapping The generic mapping of access rights masks.
- Returns
- Returns STATUS_SUCCESS if the operations have been completed without problems and that new info has been set to the security descriptor. STATUS_NO_SECURITY_ON_OBJECT is returned if the object does not have a security descriptor. STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation for the new security descriptor with new info set has failed.
- Parameters
-
[in] SecurityDescriptor A security descriptor to be freed from memory.
- Returns
- Returns STATUS_SUCCESS.
- Parameters
-
[in] _ParentDescriptor A security descriptor of the parent object that is being created. [in] _ExplicitDescriptor An explicit security descriptor that is applied to a new object. [out] NewDescriptor The new allocated security descriptor. [in] ObjectType The type of the new object. [in] IsDirectoryObject Set this to TRUE if the newly created object is a directory object, otherwise set this to FALSE. [in] AutoInheritFlags Automatic inheritance flags that influence how access control entries within ACLs from security descriptors are inherited. [in] SubjectContext Security subject context of the new object. [in] GenericMapping Generic mapping of access mask rights. [in] PoolType This parameter is unused.
- Returns
- Returns STATUS_SUCCESS if the operations have been completed successfully and that the security descriptor has been assigned to the new object. STATUS_NO_TOKEN is returned if the caller hasn't supplied a valid argument to a security subject context. STATUS_INVALID_OWNER is returned if the caller hasn't supplied a parent descriptor that belongs to the main user (owner). STATUS_INVALID_PRIMARY_GROUP is returned by the same reason as with the previous NTSTATUS code. The two NTSTATUS codes are returned if the calling thread stated that the owner and/or group is defaulted to the parent descriptor (SEF_DEFAULT_OWNER_FROM_PARENT and/or SEF_DEFAULT_GROUP_FROM_PARENT respectively). STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation for the descriptor buffer has failed. A failure NTSTATUS is returned otherwise.
- Parameters
-
[in] ParentDescriptor A security descriptor of the parent object that is being created. [in] ExplicitDescriptor An explicit security descriptor that is applied to a new object. [out] NewDescriptor The new allocated security descriptor. [in] IsDirectoryObject Set this to TRUE if the newly created object is a directory object, otherwise set this to FALSE. [in] SubjectContext Security subject context of the new object. [in] GenericMapping Generic mapping of access mask rights. [in] PoolType This parameter is unused.
- Returns
- See SeAssignSecurityEx.
- Parameters
-
[in] SecurityDescriptor A security descriptor. [out] QuotaInfoSize The returned quota size of the given security descriptor to the caller. The function may return 0 to this parameter if the descriptor doesn't have a group or a discretionary access control list (DACL) even.
- Returns
- Returns STATUS_SUCCESS if the quota size of a security descriptor has been computed successfully. STATUS_UNKNOWN_REVISION is returned if the security descriptor has an invalid revision.
Definition at line 923 of file Messaging.c.
◆ _Out_writes_bytes_to_opt_() [1/2]
| _In_ TOKEN_INFORMATION_CLASS _Out_writes_bytes_to_opt_ | ( | Length | , |
| * | ResultLength | ||
| ) |
◆ _Out_writes_bytes_to_opt_() [2/2]
| _In_ TOKEN_INFORMATION_CLASS _Out_writes_bytes_to_opt_ | ( | TokenInformationLength | , |
| * | ReturnLength | ||
| ) |
◆ _When_()
| _When_ | ( | TokenInformationClass | = = TokenAccessInformation, |
| _At_(TokenInformationLength, _In_range_(>=, sizeof(TOKEN_ACCESS_INFORMATION))) | |||
| ) |
◆ NtAccessCheck()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtAccessCheck | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on an object.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2214 of file accesschk.c.
Referenced by AccessCheck(), AccessCheckEmptyMappingTest(), and CheckTokenMembership().
◆ NtAccessCheckAndAuditAlarm()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtAccessCheckAndAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when a caller attempts to access an object and determine if the access can be made.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ObjectTypeName The name of the object type. [in] ObjectName The object name. [in] SecurityDescriptor A security descriptor. [in] DesiredAccess The desired access rights masks requested by the caller. [in] GenericMapping The generic mapping of access mask rights. [in] ObjectCreation Set this to TRUE if the object has just been created. [out] GrantedAccess Returns the granted access rights. [out] AccessStatus Returns a NTSTATUS status code indicating whether access check can be granted or not. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise.
- Returns
- See SepAccessCheckAndAuditAlarm.
Definition at line 2125 of file audit.c.
◆ NtAccessCheckByType()
| _Must_inspect_result_ NTSYSCALLAPI NTSTATUS NTAPI NtAccessCheckByType | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on the object type list. The access is either granted or denied for the whole object hierarchy in the list.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2254 of file accesschk.c.
Referenced by AccessCheckByType(), AccessGrantedMultipleObjectsTests(), AccessGrantedNoDaclTests(), AccessGrantedTests(), DenyAccessTests(), and ParamsValidationTests().
◆ NtAccessCheckByTypeResultList()
| _Must_inspect_result_ NTSYSCALLAPI NTSTATUS NTAPI NtAccessCheckByTypeResultList | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_reads_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_writes_(ObjectTypeListLength) PACCESS_MASK | GrantedAccess, | ||
| _Out_writes_(ObjectTypeListLength) PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on the object type list. Unlike the NtAccessCheckByType variant, this function will grant or deny access to each individual object and sub-object in the list.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2297 of file accesschk.c.
Referenced by AccessCheckByTypeResultList(), DenyAccessTests(), GrantedAccessTests(), and ParamValidationNoObjsList().
◆ NtAdjustGroupsToken()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtAdjustGroupsToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ BOOLEAN | ResetToDefault, | ||
| _In_opt_ PTOKEN_GROUPS | NewState, | ||
| _In_opt_ ULONG | BufferLength, | ||
| _Out_writes_bytes_to_opt_(BufferLength, *ReturnLength) PTOKEN_GROUPS | PreviousState, | ||
| _When_(PreviousState !=NULL, _Out_) PULONG | ReturnLength | ||
| ) |
◆ NtAdjustPrivilegesToken()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtAdjustPrivilegesToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ BOOLEAN | DisableAllPrivileges, | ||
| _In_opt_ PTOKEN_PRIVILEGES | NewState, | ||
| _In_ ULONG | BufferLength, | ||
| _Out_writes_bytes_to_opt_(BufferLength, *ReturnLength) PTOKEN_PRIVILEGES | PreviousState, | ||
| _When_(PreviousState !=NULL, _Out_) PULONG | ReturnLength | ||
| ) |
◆ NtAllocateLocallyUniqueId()
| NTSYSCALLAPI NTSTATUS NTAPI NtAllocateLocallyUniqueId | ( | _Out_ LUID * | LocallyUniqueId | ) |
◆ NtAllocateUuids()
| NTSYSCALLAPI NTSTATUS NTAPI NtAllocateUuids | ( | _Out_ PULARGE_INTEGER | Time, |
| _Out_ PULONG | Range, | ||
| _Out_ PULONG | Sequence, | ||
| _Out_ PUCHAR | Seed | ||
| ) |
◆ NtCompareTokens()
| NTSYSCALLAPI NTSTATUS NTAPI NtCompareTokens | ( | _In_ HANDLE | FirstTokenHandle, |
| _In_ HANDLE | SecondTokenHandle, | ||
| _Out_ PBOOLEAN | Equal | ||
| ) |
Compares tokens if they're equal or not.
- Parameters
-
[in] FirstToken The first token. [in] SecondToken The second token. [out] Equal The retrieved value which determines if the tokens are equal or not.
- Returns
- Returns STATUS_SUCCESS, otherwise it returns a failure NTSTATUS code.
Definition at line 2504 of file token.c.
Referenced by START_TEST().
◆ NtCreateToken()
| __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtCreateToken | ( | _Out_ PHANDLE | TokenHandle, |
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_opt_ POBJECT_ATTRIBUTES | ObjectAttributes, | ||
| _In_ TOKEN_TYPE | TokenType, | ||
| _In_ PLUID | AuthenticationId, | ||
| _In_ PLARGE_INTEGER | ExpirationTime, | ||
| _In_ PTOKEN_USER | TokenUser, | ||
| _In_ PTOKEN_GROUPS | TokenGroups, | ||
| _In_ PTOKEN_PRIVILEGES | TokenPrivileges, | ||
| _In_opt_ PTOKEN_OWNER | TokenOwner, | ||
| _In_ PTOKEN_PRIMARY_GROUP | TokenPrimaryGroup, | ||
| _In_opt_ PTOKEN_DEFAULT_DACL | TokenDefaultDacl, | ||
| _In_ PTOKEN_SOURCE | TokenSource | ||
| ) |
Creates an access token.
- Parameters
-
[out] TokenHandle The returned created token handle to the caller. [in] DesiredAccess The desired access rights for the token that we're creating. [in] ObjectAttributes The object attributes for the token object that we're creating. [in] TokenType The type of token to assign for the newly created token. [in] AuthenticationId Authentication ID that represents the token's identity. [in] ExpirationTime Expiration time for the token. If set to -1, the token never expires. [in] TokenUser The main user entity for the token to assign. [in] TokenGroups Group list of SIDs for the token to assign. [in] TokenPrivileges Privileges for the token. [in] TokenOwner The main user that owns the newly created token. [in] TokenPrimaryGroup The primary group that represents as the main group of the token. [in] TokenDefaultDacl Discretionary access control list for the token. This limits on how the token can be used, accessed and used by whom. [in] TokenSource The source origin of the token who creates it.
- Returns
- Returns STATUS_SUCCESS if the function has successfully created the token. A failure NTSTATUS code is returned otherwise.
Definition at line 1560 of file tokenlif.c.
Referenced by LsapLogonUser().
◆ NtDuplicateToken()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtDuplicateToken | ( | _In_ HANDLE | ExistingTokenHandle, |
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_opt_ POBJECT_ATTRIBUTES | ObjectAttributes, | ||
| _In_ BOOLEAN | EffectiveOnly, | ||
| _In_ TOKEN_TYPE | TokenType, | ||
| _Out_ PHANDLE | NewTokenHandle | ||
| ) |
Duplicates a token.
- Parameters
-
[in] ExistingTokenHandle An existing token to duplicate. [in] DesiredAccess The desired access rights for the new duplicated token. [in] ObjectAttributes Object attributes for the new duplicated token. [in] EffectiveOnly If set to TRUE, the function removes all the disabled privileges and groups of the token to duplicate. [in] TokenType Type of token to assign to the duplicated token. [out] NewTokenHandle The returned duplicated token handle.
- Returns
- STATUS_SUCCESS is returned if token duplication has completed successfully. STATUS_BAD_IMPERSONATION_LEVEL is returned if the caller erroneously wants to raise the impersonation level even though the conditions do not permit it. A failure NTSTATUS code is returned otherwise.
- Remarks
- Some sources claim 4th param is ImpersonationLevel, but on W2K this is certainly NOT true, although I can't say for sure that EffectiveOnly is correct either. -Gunnar This is true. EffectiveOnly overrides SQOS.EffectiveOnly. - IAI NOTE for readers: https://hex.pp.ua/nt/NtDuplicateToken.php is therefore wrong in that regard, while MSDN documentation is correct.
Definition at line 1871 of file tokenlif.c.
◆ NtFilterToken()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtFilterToken | ( | _In_ HANDLE | ExistingTokenHandle, |
| _In_ ULONG | Flags, | ||
| _In_opt_ PTOKEN_GROUPS | SidsToDisable, | ||
| _In_opt_ PTOKEN_PRIVILEGES | PrivilegesToDelete, | ||
| _In_opt_ PTOKEN_GROUPS | RestrictedSids, | ||
| _Out_ PHANDLE | NewTokenHandle | ||
| ) |
Creates an access token in a restricted form from the original existing token, that is, such action is called filtering.
- Parameters
-
[in] ExistingTokenHandle A handle to an access token which is to be filtered. [in] Flags Privilege flag options. This parameter argument influences how the token's privileges are filtered. For further details see remarks. [in] SidsToDisable Array of SIDs to disable. The action of doing so assigns the SE_GROUP_USE_FOR_DENY_ONLY attribute to the respective group SID and takes away SE_GROUP_ENABLED and SE_GROUP_ENABLED_BY_DEFAULT. This parameter can be NULL. This can be a UM pointer. [in] PrivilegesToDelete Array of privileges to delete. The function will walk within this array to determine if the specified privileges do exist in the access token. Any missing privileges gets ignored. This parameter can be NULL. This can be a UM pointer. [in] RestrictedSids An array list of restricted groups SID to be added in the access token. A token that is already restricted the newly added restricted SIDs are redundant information in addition to the existing restricted SIDs in the token. This parameter can be NULL. This can be a UM pointer. [out] NewTokenHandle A new handle to the restricted (filtered) access token. This can be a UM pointer.
- Returns
- Returns STATUS_SUCCESS if the routine has successfully filtered the access token. STATUS_INVALID_PARAMETER is returned if one or more parameters are not valid (see SepPerformTokenFiltering routine call for more information). A failure NTSTATUS code is returned otherwise.
- Remarks
- The Flags parameter determines the final outcome of how the privileges in an access token are filtered. This parameter can take these supported values (these can be combined):
0 – Filter the token's privileges in the usual way. The function expects that the caller MUST PROVIDE a valid array list of privileges to be deleted (that is, PrivilegesToDelete MUSTN'T BE NULL).
DISABLE_MAX_PRIVILEGE – Disables (deletes) all the privileges except SeChangeNotifyPrivilege in the new access token. Bear in mind if this flag is specified the routine ignores PrivilegesToDelete.
SANDBOX_INERT – Stores the TOKEN_SANDBOX_INERT token flag within the access token.
LUA_TOKEN – The newly filtered access token is a LUA token. This flag is not supported in Windows Server 2003.
WRITE_RESTRICTED – The newly filtered token has the restricted SIDs that are considered only when evaluating write access onto the token. This value is not supported in Windows Server 2003.
Definition at line 2077 of file tokenlif.c.
◆ NtImpersonateAnonymousToken()
| NTSYSCALLAPI NTSTATUS NTAPI NtImpersonateAnonymousToken | ( | _In_ HANDLE | ThreadHandle | ) |
Allows the calling thread to impersonate the system's anonymous logon token.
- Parameters
-
[in] ThreadHandle A handle to the thread to start the procedure of logon token impersonation. The thread must have the THREAD_IMPERSONATE access right.
- Returns
- Returns STATUS_SUCCESS if the thread has successfully impersonated the anonymous logon token, otherwise a failure NTSTATUS code is returned.
- Remarks
- By default the system gives the opportunity to the caller to impersonate the anonymous logon token without including the Everyone Group SID. In cases where the caller wants to impersonate the token including such group, the EveryoneIncludesAnonymous registry value setting has to be set to 1, from HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa registry path. The calling thread must invoke PsRevertToSelf when impersonation is no longer needed or RevertToSelf if the calling execution is done in user mode.
Definition at line 2613 of file token.c.
◆ NtOpenObjectAuditAlarm()
| __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtOpenObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_opt_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ HANDLE | ClientTokenHandle, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ ACCESS_MASK | GrantedAccess, | ||
| _In_opt_ PPRIVILEGE_SET | PrivilegeSet, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when an object is about to be opened.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID used for identification instance for auditing. [in] ObjectTypeName A Unicode string that points to an object type name. [in] ObjectName The name of the object. [in] SecurityDescriptor A security descriptor. [in] ClientTokenHandle A handle to a client access token. [in] DesiredAccess The desired access rights masks requested by the caller. [in] GrantedAccess The granted access mask rights. [in] PrivilegeSet If specified, the function will use this set of privileges to audit. [in] ObjectCreation Set this to TRUE if the object has just been created. [in] AccessGranted Set this to TRUE if the access attempt was deemed as granted. [out] GenerateOnClose A boolean flag returned to the caller once audit generation procedure finishes.
- Returns
- Returns STATUS_SUCCESS if all the operations have been completed successfully. STATUS_PRIVILEGE_NOT_HELD is returned if the given subject context does not hold the required audit privilege to actually begin auditing in the first place. STATUS_BAD_IMPERSONATION_LEVEL is returned if the security impersonation level of the client token is not on par with the impersonation level that alllows impersonation. STATUS_INVALID_PARAMETER is returned if the caller has submitted a bogus set of privileges as such array set exceeds the maximum count of privileges that the kernel can accept. A failure NTSTATUS code is returned otherwise.
Definition at line 1622 of file audit.c.
◆ NtOpenProcessTokenEx()
| NTSYSCALLAPI NTSTATUS NTAPI NtOpenProcessTokenEx | ( | _In_ HANDLE | ProcessHandle, |
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ ULONG | HandleAttributes, | ||
| _Out_ PHANDLE | TokenHandle | ||
| ) |
◆ NtPrivilegeCheck()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtPrivilegeCheck | ( | _In_ HANDLE | ClientToken, |
| _Inout_ PPRIVILEGE_SET | RequiredPrivileges, | ||
| _Out_ PBOOLEAN | Result | ||
| ) |
◆ NtPrivilegedServiceAuditAlarm()
| NTSYSCALLAPI NTSTATUS NTAPI NtPrivilegedServiceAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PUNICODE_STRING | ServiceName, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
◆ NtPrivilegeObjectAuditAlarm()
| __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtPrivilegeObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
◆ NtSetInformationToken()
| _Must_inspect_result_ __kernel_entry NTSYSCALLAPI NTSTATUS NTAPI NtSetInformationToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ TOKEN_INFORMATION_CLASS | TokenInformationClass, | ||
| _In_reads_bytes_(TokenInformationLength) PVOID | TokenInformation, | ||
| _In_ ULONG | TokenInformationLength | ||
| ) |
Sets (modifies) some specific information in regard of an access token. The calling thread must have specific access rights in order to modify token's information data.
@unimplemented
- Parameters
-
[in] TokenHandle A handle of a token where information is to be modified. [in] TokenInformationClass Token information class. [in] TokenInformation An arbitrary pointer to a buffer with token information to set. Such arbitrary buffer depends on the information class chosen that the caller wants to modify such information data of a token. [in] TokenInformationLength Length of the token information buffer, in bytes.
- Returns
- Returns STATUS_SUCCESS if information setting has completed successfully. STATUS_INFO_LENGTH_MISMATCH is returned if the information length of the buffer is less than the required length. STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation has failed. STATUS_PRIVILEGE_NOT_HELD is returned if the calling thread hasn't the required privileges to perform the operation in question. A failure NTSTATUS code is returned otherwise.
- Remarks
- The function is partly implemented, mainly TokenOrigin.
Definition at line 1125 of file tokencls.c.
◆ SeCaptureSecurityDescriptor()
| NTKERNELAPI NTSTATUS NTAPI SeCaptureSecurityDescriptor | ( | _In_ PSECURITY_DESCRIPTOR | _OriginalSecurityDescriptor, |
| _In_ KPROCESSOR_MODE | CurrentMode, | ||
| _In_ POOL_TYPE | PoolType, | ||
| _In_ BOOLEAN | CaptureIfKernel, | ||
| _Out_ PSECURITY_DESCRIPTOR * | CapturedSecurityDescriptor | ||
| ) |
Captures a security descriptor.
- Parameters
-
[in] _OriginalSecurityDescriptor An already existing and valid security descriptor to be captured. [in] CurrentMode Processor level access mode. [in] PoolType Pool type to be used when allocating the captured buffer. [in] CaptureIfKernel Set this to TRUE if capturing is done within the kernel. [out] CapturedSecurityDescriptor The captured security descriptor.
- Returns
- Returns STATUS_SUCCESS if the operations have been completed successfully and that the security descriptor has been captured. STATUS_UNKNOWN_REVISION is returned if the security descriptor has an unknown revision. STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation for the captured buffer has failed. A failure NTSTATUS code is returned otherwise.
Definition at line 386 of file sd.c.
Referenced by NtOpenObjectAuditAlarm(), NtSetSecurityObject(), ObpCaptureObjectCreateInformation(), ProbeAndCaptureObjectAttributes(), SepAccessCheck(), and SepAccessCheckAndAuditAlarm().
◆ SeCreateAccessState()
| NTKERNELAPI NTSTATUS NTAPI SeCreateAccessState | ( | _In_ PACCESS_STATE | AccessState, |
| _In_ PAUX_ACCESS_DATA | AuxData, | ||
| _In_ ACCESS_MASK | Access, | ||
| _In_ PGENERIC_MAPPING | GenericMapping | ||
| ) |
◆ SeDeleteAccessState()
| NTKERNELAPI VOID NTAPI SeDeleteAccessState | ( | _In_ PACCESS_STATE | AccessState | ) |
Deletes an allocated access state from the memory.
- Parameters
-
[in] AccessState A valid access state.
- Returns
- Nothing.
Definition at line 150 of file access.c.
Referenced by NtOpenProcess(), NtOpenThread(), ObDuplicateObject(), ObInsertObject(), ObOpenObjectByName(), ObOpenObjectByPointer(), ObReferenceObjectByName(), PspCreateProcess(), PspCreateThread(), and START_TEST().
◆ SeReleaseSecurityDescriptor()
| NTKERNELAPI NTSTATUS NTAPI SeReleaseSecurityDescriptor | ( | _In_ PSECURITY_DESCRIPTOR | CapturedSecurityDescriptor, |
| _In_ KPROCESSOR_MODE | CurrentMode, | ||
| _In_ BOOLEAN | CaptureIfKernelMode | ||
| ) |
Releases a captured security descriptor buffer.
- Parameters
-
[in] CapturedSecurityDescriptor The captured security descriptor to be freed. [in] CurrentMode Processor level access mode. [in] CaptureIfKernelMode Set this to TRUE if the releasing is to be done within the kernel.
- Returns
- Returns STATUS_SUCCESS.
Definition at line 760 of file sd.c.
Referenced by NtOpenObjectAuditAlarm(), NtSetSecurityObject(), ObInsertObject(), ObpReleaseObjectCreateInformation(), ReleaseCapturedObjectAttributes(), SepAccessCheck(), and SepAccessCheckAndAuditAlarm().
◆ SeTokenImpersonationLevel()
| NTKERNELAPI SECURITY_IMPERSONATION_LEVEL NTAPI SeTokenImpersonationLevel | ( | _In_ PACCESS_TOKEN | Token | ) |
Gathers the security impersonation level of an access token.
- Returns
- Returns the security impersonation level from a valid token.
Definition at line 2060 of file token.c.
Referenced by PsAssignImpersonationToken().
◆ ZwAccessCheck()
| NTSYSAPI NTSTATUS NTAPI ZwAccessCheck | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Out_ PULONG | PrivilegeSetLength, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
◆ ZwAdjustGroupsToken()
| NTSYSAPI NTSTATUS NTAPI ZwAdjustGroupsToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ BOOLEAN | ResetToDefault, | ||
| _In_ PTOKEN_GROUPS | NewState, | ||
| _In_ ULONG | BufferLength, | ||
| _Out_opt_ PTOKEN_GROUPS | PreviousState, | ||
| _Out_ PULONG | ReturnLength | ||
| ) |
◆ ZwAdjustPrivilegesToken()
| _Must_inspect_result_ NTSYSAPI NTSTATUS NTAPI ZwAdjustPrivilegesToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ BOOLEAN | DisableAllPrivileges, | ||
| _In_opt_ PTOKEN_PRIVILEGES | NewState, | ||
| _In_ ULONG | BufferLength, | ||
| _Out_writes_bytes_to_opt_(BufferLength, *ReturnLength) PTOKEN_PRIVILEGES | PreviousState, | ||
| _When_(PreviousState !=NULL, _Out_) PULONG | ReturnLength | ||
| ) |
Referenced by RtlAcquirePrivilege(), RtlAdjustPrivilege(), RtlpSysVolTakeOwnership(), RtlReleasePrivilege(), and RtlRemovePrivileges().
◆ ZwAllocateLocallyUniqueId()
Referenced by CreateInitialSystemToken().
◆ ZwAllocateUuids()
| NTSYSAPI NTSTATUS NTAPI ZwAllocateUuids | ( | _Out_ PULARGE_INTEGER | Time, |
| _Out_ PULONG | Range, | ||
| _Out_ PULONG | Sequence, | ||
| _Out_ PUCHAR | Seed | ||
| ) |
◆ ZwCreateToken()
| NTSYSAPI NTSTATUS NTAPI ZwCreateToken | ( | _Out_ PHANDLE | TokenHandle, |
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ POBJECT_ATTRIBUTES | ObjectAttributes, | ||
| _In_ TOKEN_TYPE | TokenType, | ||
| _In_ PLUID | AuthenticationId, | ||
| _In_ PLARGE_INTEGER | ExpirationTime, | ||
| _In_ PTOKEN_USER | TokenUser, | ||
| _In_ PTOKEN_GROUPS | TokenGroups, | ||
| _In_ PTOKEN_PRIVILEGES | TokenPrivileges, | ||
| _In_ PTOKEN_OWNER | TokenOwner, | ||
| _In_ PTOKEN_PRIMARY_GROUP | TokenPrimaryGroup, | ||
| _In_ PTOKEN_DEFAULT_DACL | TokenDefaultDacl, | ||
| _In_ PTOKEN_SOURCE | TokenSource | ||
| ) |
Referenced by CreateInitialSystemToken().
◆ ZwImpersonateAnonymousToken()
◆ ZwOpenObjectAuditAlarm()
| NTSYSAPI NTSTATUS NTAPI ZwOpenObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ULONG | DesiredAccess, | ||
| _In_ ULONG | GrantedAccess, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
◆ ZwPrivilegeCheck()
| NTSYSAPI NTSTATUS NTAPI ZwPrivilegeCheck | ( | _In_ HANDLE | ClientToken, |
| _In_ PPRIVILEGE_SET | RequiredPrivileges, | ||
| _In_ PBOOLEAN | Result | ||
| ) |
◆ ZwPrivilegedServiceAuditAlarm()
| NTSYSAPI NTSTATUS NTAPI ZwPrivilegedServiceAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PUNICODE_STRING | ServiceName, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
◆ ZwPrivilegeObjectAuditAlarm()
| NTSYSAPI NTSTATUS NTAPI ZwPrivilegeObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ULONG | DesiredAccess, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
◆ ZwSetInformationToken()
| NTSYSAPI NTSTATUS NTAPI ZwSetInformationToken | ( | _In_ HANDLE | TokenHandle, |
| _In_ TOKEN_INFORMATION_CLASS | TokenInformationClass, | ||
| _Out_ PVOID | TokenInformation, | ||
| _In_ ULONG | TokenInformationLength | ||
| ) |
Variable Documentation
◆ DesiredAccess
◆ EffectiveOnly
| _Must_inspect_result_ _In_opt_ PACCESS_TOKEN _In_ BOOLEAN _In_ BOOLEAN EffectiveOnly |
Definition at line 410 of file sefuncs.h.
Referenced by GetProcessLuid(), NtCloseObjectAuditAlarm(), NtDuplicateToken(), NtOpenThreadTokenEx(), ObpReferenceDeviceMap(), PsImpersonateClient(), PsReferenceEffectiveToken(), PsReferenceImpersonationToken(), SeCaptureSubjectContextEx(), SeImpersonateClientEx(), SepDuplicateToken(), SepOpenThreadToken(), and test_object_permanence().
◆ HandleAttributes
◆ Length
◆ NewTokenHandle
| _In_ ACCESS_MASK _In_opt_ POBJECT_ATTRIBUTES _In_ BOOLEAN _In_ TOKEN_TYPE _Out_ PHANDLE NewTokenHandle |
Definition at line 412 of file sefuncs.h.
Referenced by CreateRestrictedToken(), NtDuplicateToken(), and NtFilterToken().
◆ ObjectAttributes
| _In_ ACCESS_MASK _In_opt_ POBJECT_ATTRIBUTES ObjectAttributes |
◆ ResultLength
◆ ReturnLength
◆ TokenHandle
◆ TokenInformationClass
| _In_ TOKEN_INFORMATION_CLASS TokenInformationClass |
Definition at line 317 of file sefuncs.h.
Referenced by GetTokenInformation(), NtQueryInformationToken(), NtSetInformationToken(), SeQueryInformationToken(), and SetTokenInformation().
◆ TokenInformationLength
| _In_ TOKEN_INFORMATION_CLASS _In_ ULONG TokenInformationLength |
Definition at line 319 of file sefuncs.h.
Referenced by GetTokenInformation(), NtQueryInformationToken(), NtSetInformationToken(), and SetTokenInformation().
◆ TokenType
| _In_ ACCESS_MASK _In_opt_ POBJECT_ATTRIBUTES _In_ BOOLEAN _In_ TOKEN_TYPE TokenType |
Definition at line 411 of file sefuncs.h.
Referenced by CheckTokenMembership(), CreateProcessAsUserCommon(), DuplicateTokenEx(), GetTokenInformation(), ImpersonateLoggedOnUser(), ImpersonatePrinterClient(), NpFreeClientSecurityContext(), NtCreateToken(), NtDuplicateToken(), NtQueryInformationToken(), PsReferenceEffectiveToken(), QueryTokenTypeTests(), SeCreateClientSecurity(), SepCreateClientSecurity(), SepCreateToken(), SepDuplicateToken(), SeQueryInformationToken(), SetTokenInformation(), test_CreateRestrictedToken(), test_elevation(), TestsSeQueryInformationToken(), validate_impersonation_token(), and WhoamiGetTokenInfo().