#include <ntoskrnl.h>#include <debug.h>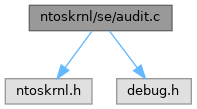
Go to the source code of this file.
Macros | |
| #define | NDEBUG |
| #define | SEP_PRIVILEGE_SET_MAX_COUNT 60 |
Variables | |
| UNICODE_STRING | SeSubsystemName = RTL_CONSTANT_STRING(L"Security") |
Macro Definition Documentation
◆ NDEBUG
◆ SEP_PRIVILEGE_SET_MAX_COUNT
Function Documentation
◆ NtAccessCheckAndAuditAlarm()
| _Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtAccessCheckAndAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when a caller attempts to access an object and determine if the access can be made.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ObjectTypeName The name of the object type. [in] ObjectName The object name. [in] SecurityDescriptor A security descriptor. [in] DesiredAccess The desired access rights masks requested by the caller. [in] GenericMapping The generic mapping of access mask rights. [in] ObjectCreation Set this to TRUE if the object has just been created. [out] GrantedAccess Returns the granted access rights. [out] AccessStatus Returns a NTSTATUS status code indicating whether access check can be granted or not. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise.
- Returns
- See SepAccessCheckAndAuditAlarm.
Definition at line 2125 of file audit.c.
Referenced by AccessCheckAndAuditAlarmA(), and AccessCheckAndAuditAlarmW().
◆ NtAccessCheckByTypeAndAuditAlarm()
| _Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtAccessCheckByTypeAndAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ AUDIT_EVENT_TYPE | AuditType, | ||
| _In_ ULONG | Flags, | ||
| _In_reads_opt_(ObjectTypeLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when a caller attempts to access an object and determine if the access can be made by type.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ObjectTypeName The name of the object type. [in] ObjectName The object name. [in] SecurityDescriptor A security descriptor. [in] PrincipalSelfSid A principal self user SID. [in] DesiredAccess The desired access rights masks requested by the caller. [in] AuditType Type of audit to start, influencing how the audit should be done. [in] Flags Flag bitmask, used to check if auditing can be done without privileges. [in] ObjectTypeList A list of object types. [in] ObjectTypeLength The length size of the list. [in] GenericMapping The generic mapping of access mask rights. [in] ObjectCreation Set this to TRUE if the object has just been created. [out] GrantedAccess Returns the granted access rights. [out] AccessStatus Returns a NTSTATUS status code indicating whether access check can be granted or not. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise.
- Returns
- See SepAccessCheckAndAuditAlarm.
Definition at line 2222 of file audit.c.
◆ NtAccessCheckByTypeResultListAndAuditAlarm()
| _Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtAccessCheckByTypeResultListAndAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ AUDIT_EVENT_TYPE | AuditType, | ||
| _In_ ULONG | Flags, | ||
| _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _Out_writes_(ObjectTypeListLength) PACCESS_MASK | GrantedAccessList, | ||
| _Out_writes_(ObjectTypeListLength) PNTSTATUS | AccessStatusList, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when a caller attempts to access an object and determine if the access can be made by given type result.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ObjectTypeName The name of the object type. [in] ObjectName The object name. [in] SecurityDescriptor A security descriptor. [in] PrincipalSelfSid A principal self user SID. [in] DesiredAccess The desired access rights masks requested by the caller. [in] AuditType Type of audit to start, influencing how the audit should be done. [in] Flags Flag bitmask, used to check if auditing can be done without privileges. [in] ObjectTypeList A list of object types. [in] ObjectTypeLength The length size of the list. [in] GenericMapping The generic mapping of access mask rights. [in] ObjectCreation Set this to TRUE if the object has just been created. [out] GrantedAccessList Returns the granted access rights. [out] AccessStatusList Returns a NTSTATUS status code indicating whether access check can be granted or not. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise.
- Returns
- See SepAccessCheckAndAuditAlarm.
Definition at line 2324 of file audit.c.
◆ NtAccessCheckByTypeResultListAndAuditAlarmByHandle()
| _Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtAccessCheckByTypeResultListAndAuditAlarmByHandle | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ AUDIT_EVENT_TYPE | AuditType, | ||
| _In_ ULONG | Flags, | ||
| _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _Out_writes_(ObjectTypeListLength) PACCESS_MASK | GrantedAccessList, | ||
| _Out_writes_(ObjectTypeListLength) PNTSTATUS | AccessStatusList, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when a caller attempts to access an object and determine if the access can be made by given type result and a token handle.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ClientToken A handle to a client access token. [in] ObjectTypeName The name of the object type. [in] ObjectName The object name. [in] SecurityDescriptor A security descriptor. [in] PrincipalSelfSid A principal self user SID. [in] DesiredAccess The desired access rights masks requested by the caller. [in] AuditType Type of audit to start, influencing how the audit should be done. [in] Flags Flag bitmask, used to check if auditing can be done without privileges. [in] ObjectTypeList A list of object types. [in] ObjectTypeLength The length size of the list. [in] GenericMapping The generic mapping of access mask rights. [in] ObjectCreation Set this to TRUE if the object has just been created. [out] GrantedAccessList Returns the granted access rights. [out] AccessStatusList Returns a NTSTATUS status code indicating whether access check can be granted or not. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise.
- Returns
- See SepAccessCheckAndAuditAlarm.
Definition at line 2430 of file audit.c.
◆ NtCloseObjectAuditAlarm()
| NTSTATUS NTAPI NtCloseObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ BOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when an object is about to be closed.
- Parameters
-
[in] SubsystemName A Unicode string that points to the name of the subsystem. [in] HandleId A handle of an ID used for identification instance for auditing. [in] GenerateOnClose A boolean value previously created by the "open" equivalent of this function. If the caller explicitly sets this to FALSE, the function assumes that the object is not opened.
- Returns
- Returns STATUS_SUCCESS if all the operations have completed successfully. STATUS_PRIVILEGE_NOT_HELD is returned if the security subject context does not have the audit privilege to actually begin auditing procedures in the first place.
Definition at line 1358 of file audit.c.
Referenced by ObjectCloseAuditAlarmA(), and ObjectCloseAuditAlarmW().
◆ NtDeleteObjectAuditAlarm()
| NTSTATUS NTAPI NtDeleteObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ BOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when an object is about to be deleted.
@unimplemented
- Parameters
-
[in] SubsystemName A Unicode string that points to the name of the subsystem. [in] HandleId A handle of an ID used for identification instance for auditing. [in] GenerateOnClose A boolean value previously created by the "open" equivalent of this function. If the caller explicitly sets this to FALSE, the function assumes that the object is not opened.
- Returns
- To be added...
Definition at line 1475 of file audit.c.
Referenced by ObjectDeleteAuditAlarmA(), and ObjectDeleteAuditAlarmW().
◆ NtOpenObjectAuditAlarm()
| __kernel_entry NTSTATUS NTAPI NtOpenObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_opt_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ HANDLE | ClientTokenHandle, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ ACCESS_MASK | GrantedAccess, | ||
| _In_opt_ PPRIVILEGE_SET | PrivilegeSet, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when an object is about to be opened.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID used for identification instance for auditing. [in] ObjectTypeName A Unicode string that points to an object type name. [in] ObjectName The name of the object. [in] SecurityDescriptor A security descriptor. [in] ClientTokenHandle A handle to a client access token. [in] DesiredAccess The desired access rights masks requested by the caller. [in] GrantedAccess The granted access mask rights. [in] PrivilegeSet If specified, the function will use this set of privileges to audit. [in] ObjectCreation Set this to TRUE if the object has just been created. [in] AccessGranted Set this to TRUE if the access attempt was deemed as granted. [out] GenerateOnClose A boolean flag returned to the caller once audit generation procedure finishes.
- Returns
- Returns STATUS_SUCCESS if all the operations have been completed successfully. STATUS_PRIVILEGE_NOT_HELD is returned if the given subject context does not hold the required audit privilege to actually begin auditing in the first place. STATUS_BAD_IMPERSONATION_LEVEL is returned if the security impersonation level of the client token is not on par with the impersonation level that alllows impersonation. STATUS_INVALID_PARAMETER is returned if the caller has submitted a bogus set of privileges as such array set exceeds the maximum count of privileges that the kernel can accept. A failure NTSTATUS code is returned otherwise.
Definition at line 1622 of file audit.c.
Referenced by ObjectOpenAuditAlarmA(), and ObjectOpenAuditAlarmW().
◆ NtPrivilegedServiceAuditAlarm()
| __kernel_entry NTSTATUS NTAPI NtPrivilegedServiceAuditAlarm | ( | _In_opt_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PUNICODE_STRING | ServiceName, | ||
| _In_ HANDLE | ClientTokenHandle, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
Raises an alarm audit message when a caller attempts to request a privileged service call.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] ServiceName A Unicode string that points to a name of the privileged service. [in] ClientTokenHandle A handle to a client access token. [in] Privileges An array set of privileges. [in] AccessGranted Set this to TRUE if the access attempt was deemed as granted.
- Returns
- Returns STATUS_SUCCESS if all the operations have been completed successfully. STATUS_PRIVILEGE_NOT_HELD is returned if the given subject context does not hold the required audit privilege to actually begin auditing in the first place. STATUS_BAD_IMPERSONATION_LEVEL is returned if the security impersonation level of the client token is not on par with the impersonation level that alllows impersonation. STATUS_INVALID_PARAMETER is returned if the caller has submitted a bogus set of privileges as such array set exceeds the maximum count of privileges that the kernel can accept. A failure NTSTATUS code is returned otherwise.
Definition at line 1883 of file audit.c.
Referenced by PrivilegedServiceAuditAlarmA(), and PrivilegedServiceAuditAlarmW().
◆ NtPrivilegeObjectAuditAlarm()
| NTSTATUS NTAPI NtPrivilegeObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ULONG | DesiredAccess, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
Raises an alarm audit message when a caller attempts to access a privileged object.
- Parameters
-
[in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID that is used as identification instance for auditing. [in] ClientToken A handle to a client access token. [in] DesiredAccess A handle to a client access token. [in] Privileges An array set of privileges. [in] AccessGranted Set this to TRUE if the access attempt was deemed as granted.
- Returns
- To be added...
Definition at line 2066 of file audit.c.
Referenced by ObjectPrivilegeAuditAlarmA(), and ObjectPrivilegeAuditAlarmW().
◆ SeAuditHardLinkCreation()
| VOID NTAPI SeAuditHardLinkCreation | ( | _In_ PUNICODE_STRING | FileName, |
| _In_ PUNICODE_STRING | LinkName, | ||
| _In_ BOOLEAN | bSuccess | ||
| ) |
Performs an audit against a hard link creation.
@unimplemented
- Parameters
-
[in] FileName A Unicode string that points to the name of the file. [in] LinkName A Unicode string that points to a link. [out] bSuccess If TRUE, the function has successfully audited the hard link and security access can be granted, FALSE otherwise.
- Returns
- Nothing.
◆ SeAuditingFileEvents()
| BOOLEAN NTAPI SeAuditingFileEvents | ( | _In_ BOOLEAN | AccessGranted, |
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor | ||
| ) |
Determines whether auditing against file events is being done or not.
@unimplemented
- Parameters
-
[in] AccessGranted If set to TRUE, the access attempt is deemed as successful otherwise set it to FALSE. [in] SecurityDescriptor A security descriptor.
- Returns
- Returns TRUE if auditing is being currently done, FALSE otherwise.
◆ SeAuditingFileEventsWithContext()
| BOOLEAN NTAPI SeAuditingFileEventsWithContext | ( | _In_ BOOLEAN | AccessGranted, |
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSECURITY_SUBJECT_CONTEXT | SubjectSecurityContext | ||
| ) |
Determines whether auditing against file events with subject context is being done or not.
@unimplemented
- Parameters
-
[in] AccessGranted If set to TRUE, the access attempt is deemed as successful otherwise set it to FALSE. [in] SecurityDescriptor A security descriptor. [in] SubjectSecurityContext If specified, the function will check if security auditing is currently being done with this context.
- Returns
- Returns TRUE if auditing is being currently done, FALSE otherwise.
◆ SeAuditingFileOrGlobalEvents()
| BOOLEAN NTAPI SeAuditingFileOrGlobalEvents | ( | _In_ BOOLEAN | AccessGranted, |
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ PSECURITY_SUBJECT_CONTEXT | SubjectSecurityContext | ||
| ) |
Determines whether auditing against files or global events with subject context is being done or not.
@unimplemented
- Parameters
-
[in] AccessGranted If set to TRUE, the access attempt is deemed as successful otherwise set it to FALSE. [in] SecurityDescriptor A security descriptor. [in] SubjectSecurityContext If specified, the function will check if security auditing is currently being done with this context.
- Returns
- Returns TRUE if auditing is being currently done, FALSE otherwise.
◆ SeAuditingHardLinkEvents()
| BOOLEAN NTAPI SeAuditingHardLinkEvents | ( | _In_ BOOLEAN | AccessGranted, |
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor | ||
| ) |
Determines whether auditing against hard links events is being done or not.
@unimplemented
- Parameters
-
[in] AccessGranted If set to TRUE, the access attempt is deemed as successful otherwise set it to FALSE. [in] SecurityDescriptor A security descriptor.
- Returns
- Returns TRUE if auditing is being currently done, FALSE otherwise.
◆ SeAuditingHardLinkEventsWithContext()
| BOOLEAN NTAPI SeAuditingHardLinkEventsWithContext | ( | _In_ BOOLEAN | AccessGranted, |
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSECURITY_SUBJECT_CONTEXT | SubjectSecurityContext | ||
| ) |
Determines whether auditing against hard links events with subject context is being done or not.
@unimplemented
- Parameters
-
[in] AccessGranted If set to TRUE, the access attempt is deemed as successful otherwise set it to FALSE. [in] SecurityDescriptor A security descriptor. [in] SubjectSecurityContext If specified, the function will check if security auditing is currently being done with this context.
- Returns
- Returns TRUE if auditing is being currently done, FALSE otherwise.
◆ SeAuditProcessCreate()
Peforms a security auditing against a process that is about to be created.
@unimplemented
- Parameters
-
[in] Process An object that points to a process which is in process of creation.
- Returns
- Nothing.
Definition at line 56 of file audit.c.
Referenced by PspCreateProcess().
◆ SeAuditProcessExit()
Peforms a security auditing against a process that is about to be terminated.
@unimplemented
- Parameters
-
[in] Process An object that points to a process which is in process of termination.
- Returns
- Nothing.
Definition at line 77 of file audit.c.
Referenced by PspExitThread().
◆ SeCloseObjectAuditAlarm()
| VOID NTAPI SeCloseObjectAuditAlarm | ( | _In_ PVOID | Object, |
| _In_ HANDLE | Handle, | ||
| _In_ BOOLEAN | PerformAction | ||
| ) |
Closes an alarm audit of an object.
@unimplemented
- Parameters
-
[in] Object An arbitrary pointer data that points to the object. [in] Handle A handle of the said object. [in] PerformAction Set this to TRUE to perform any auxiliary action, otherwise set to FALSE.
- Returns
- Nothing.
◆ SeDeleteObjectAuditAlarm()
Deletes an alarm audit of an object.
@unimplemented
- Parameters
-
[in] Object An arbitrary pointer data that points to the object. [in] Handle A handle of the said object.
- Returns
- Nothing.
◆ SeDetailedAuditingWithToken()
Peforms a detailed security auditing with an access token.
@unimplemented
- Returns
- To be added...
Definition at line 34 of file audit.c.
Referenced by ObInitProcess(), PspCreateProcess(), and PspExitThread().
◆ SeInitializeProcessAuditName()
| NTSTATUS NTAPI SeInitializeProcessAuditName | ( | _In_ PFILE_OBJECT | FileObject, |
| _In_ BOOLEAN | DoAudit, | ||
| _Out_ POBJECT_NAME_INFORMATION * | AuditInfo | ||
| ) |
Initializes a process audit name and returns it to the caller.
- Parameters
-
[in] FileObject File object that points to a name to be queried. [in] DoAudit If set to TRUE, the function will perform various security auditing onto the audit name. [out] AuditInfo The returned audit info data.
- Returns
- Returns STATUS_SUCCESS if process audit name initialization has completed successfully. STATUS_NO_MEMORY is returned if pool allocation for object name info has failed. A failure NTSTATUS code is returned otherwise.
Definition at line 105 of file audit.c.
Referenced by MmInitializeProcessAddressSpace(), and SeLocateProcessImageName().
◆ SeLocateProcessImageName()
| NTSTATUS NTAPI SeLocateProcessImageName | ( | _In_ PEPROCESS | Process, |
| _Out_ PUNICODE_STRING * | ProcessImageName | ||
| ) |
Finds the process image name of a specific process.
- Parameters
-
[in] Process Process object submitted by the caller, where the image name is to be located. [out] ProcessImageName An output Unicode string structure with the located process image name.
- Returns
- Returns STATUS_SUCCESS if process image name has been located successfully. STATUS_NO_MEMORY is returned if pool allocation for the image name has failed. A failure NTSTATUS code is returned otherwise.
Definition at line 199 of file audit.c.
Referenced by NtQueryInformationProcess(), and QSI_DEF().
◆ SeOpenObjectAuditAlarm()
| VOID NTAPI SeOpenObjectAuditAlarm | ( | _In_ PUNICODE_STRING | ObjectTypeName, |
| _In_opt_ PVOID | Object, | ||
| _In_opt_ PUNICODE_STRING | AbsoluteObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ PACCESS_STATE | AccessState, | ||
| _In_ BOOLEAN | ObjectCreated, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Creates an audit with alarm notification of an object that is being opened.
@unimplemented
- Parameters
-
[in] ObjectTypeName A Unicode string that points to the object type name. [in] Object If specified, the function will use this parameter to directly open the object. [in] AbsoluteObjectName If specified, the function will use this parameter to directly open the object through the absolute name of the object. [in] SecurityDescriptor A security descriptor. [in] AccessState An access state right mask when opening the object. [in] ObjectCreated Set this to TRUE if the object has been fully created, FALSE otherwise. [in] AccessGranted Set this to TRUE if access was deemed as granted. [in] AccessMode Processor level access mode. [out] GenerateOnClose A boolean flag returned to the caller once audit generation procedure finishes.
- Returns
- Nothing.
Definition at line 1213 of file audit.c.
Referenced by IopParseDevice(), NpCreateClientEnd(), NpCreateExistingNamedPipe(), and ObCheckObjectAccess().
◆ SeOpenObjectForDeleteAuditAlarm()
| VOID NTAPI SeOpenObjectForDeleteAuditAlarm | ( | _In_ PUNICODE_STRING | ObjectTypeName, |
| _In_opt_ PVOID | Object, | ||
| _In_opt_ PUNICODE_STRING | AbsoluteObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ PACCESS_STATE | AccessState, | ||
| _In_ BOOLEAN | ObjectCreated, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Creates an audit with alarm notification of an object that is being opened for deletion.
@unimplemented
- Parameters
-
[in] ObjectTypeName A Unicode string that points to the object type name. [in] Object If specified, the function will use this parameter to directly open the object. [in] AbsoluteObjectName If specified, the function will use this parameter to directly open the object through the absolute name of the object. [in] SecurityDescriptor A security descriptor. [in] AccessState An access state right mask when opening the object. [in] ObjectCreated Set this to TRUE if the object has been fully created, FALSE otherwise. [in] AccessGranted Set this to TRUE if access was deemed as granted. [in] AccessMode Processor level access mode. [out] GenerateOnClose A boolean flag returned to the caller once audit generation procedure finishes.
- Returns
- Nothing.
◆ SepAccessCheckAndAuditAlarm()
| _Must_inspect_result_ NTSTATUS NTAPI SepAccessCheckAndAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_opt_ PVOID | HandleId, | ||
| _In_ PHANDLE | ClientTokenHandle, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ AUDIT_EVENT_TYPE | AuditType, | ||
| _In_ ULONG | Flags, | ||
| _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_(ObjectTypeListLength) PACCESS_MASK | GrantedAccessList, | ||
| _Out_writes_(ObjectTypeListLength) PNTSTATUS | AccessStatusList, | ||
| _Out_ PBOOLEAN | GenerateOnClose, | ||
| _In_ BOOLEAN | UseResultList | ||
| ) |
Performs security auditing, if the specific object can be granted security access or not.
- Parameters
-
[in] SubsystemName A Unicode string that represents the name of a subsystem that actuates the auditing process. [in] HandleId A handle to an ID used to identify an object where auditing is to be done. [in] SubjectContext Security subject context. [in] ObjectTypeName A Unicode string that represents the name of an object type. [in] ObjectName The name of the object. [in] SecurityDescriptor A security descriptor with internal security information details for audit. [in] PrincipalSelfSid A principal self user SID. [in] DesiredAccess The desired access rights masks requested by the caller. [in] AuditType Type of audit to start. This parameter influences how an audit should be done. [in] Flags Flag bitmask parameter. [in] HaveAuditPrivilege If set to TRUE, the security subject context has the audit privilege thus it is allowed the ability to perform the audit. [in] ObjectTypeList A list of object types. [in] ObjectTypeListLength The length size of the list. [in] GenericMapping The generic mapping table of access rights used whilst performing auditing sequence procedure. [out] GrantedAccessList This parameter is used to return to the caller a list of actual granted access rights masks that the audited object has. [out] AccessStatusList This parameter is used to return to the caller a list of status return codes. The function may actually return a single NTSTATUS code if the calling thread sets UseResultList parameter to FALSE. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise. [in] UseResultList If set to TRUE, the caller wants that the function should only return a single NTSTATUS code.
- Returns
- Returns STATUS_SUCCESS if the function has completed the whole internal auditing procedure mechanism with success. STATUS_INVALID_PARAMETER is returned if one of the parameters do not satisfy the general requirements by the function. STATUS_INSUFFICIENT_RESOURCES is returned if pool memory allocation has failed. STATUS_PRIVILEGE_NOT_HELD is returned if the current security subject context does not have the required audit privilege to actually perform auditing in the first place. STATUS_INVALID_SECURITY_DESCR is returned if the security descriptor provided by the caller is not valid, that is, such descriptor doesn't belong to the main user (owner) and current group. STATUS_GENERIC_NOT_MAPPED is returned if the access rights masks aren't actually mapped. A failure NTSTATUS code is returned otherwise.
Definition at line 614 of file audit.c.
Referenced by NtAccessCheckAndAuditAlarm(), NtAccessCheckByTypeAndAuditAlarm(), NtAccessCheckByTypeResultListAndAuditAlarm(), and NtAccessCheckByTypeResultListAndAuditAlarmByHandle().
◆ SepAccessCheckAndAuditAlarmWorker()
|
static |
Worker function that serves as the main heart and brain of the whole concept and implementation of auditing in the kernel.
@unimplemented
- Parameters
-
[in] SubsystemName A Unicode string that represents the name of a subsystem that actuates the auditing process. [in] HandleId A handle to an ID used to identify an object where auditing is to be done. [in] SubjectContext Security subject context. [in] ObjectTypeName A Unicode string that represents the name of an object type. [in] ObjectName The name of the object. [in] SecurityDescriptor A security descriptor with internal security information details for audit. [in] PrincipalSelfSid A principal self user SID. [in] DesiredAccess The desired access rights masks requested by the caller. [in] AuditType Type of audit to start. This parameter influences how an audit should be done. [in] HaveAuditPrivilege If set to TRUE, the security subject context has the audit privilege thus it is allowed the ability to perform the audit. [in] ObjectTypeList A list of object types. [in] ObjectTypeListLength The length size of the list. [in] GenericMapping The generic mapping table of access rights used whilst performing auditing sequence procedure. [out] GrantedAccessList This parameter is used to return to the caller a list of actual granted access rights masks that the audited object has. [out] AccessStatusList This parameter is used to return to the caller a list of status return codes. The function may actually return a single NTSTATUS code if the calling thread sets UseResultList parameter to FALSE. [out] GenerateOnClose Returns TRUE if the function has generated a list of granted access rights and status codes on termination, FALSE otherwise. [in] UseResultList If set to TRUE, the caller wants that the function should only return a single NTSTATUS code.
- Returns
- Returns STATUS_SUCCESS if the function has completed the whole internal auditing procedure mechanism with success.
FIXME: we should do some real work here...
HACK: we just pretend all access is granted!
Definition at line 489 of file audit.c.
Referenced by SepAccessCheckAndAuditAlarm().
◆ SepAdtCloseObjectAuditAlarm()
| VOID NTAPI SepAdtCloseObjectAuditAlarm | ( | _In_ PUNICODE_STRING | SubsystemName, |
| _In_ PVOID | HandleId, | ||
| _In_ PSID | Sid | ||
| ) |
Closes an audit alarm event of an object.
- Parameters
-
[in] SubsystemName A Unicode string pointing to the name of the subsystem where auditing alarm event has to be closed. [in] HandleId A handle to an ID where such ID represents the identification of the object where audit alarm is to be closed. [in] Sid A SID that represents the user who attempted to close the audit alarm.
- Returns
- Nothing.
Definition at line 287 of file audit.c.
Referenced by NtCloseObjectAuditAlarm().
◆ SepAdtPrivilegedServiceAuditAlarm()
| VOID NTAPI SepAdtPrivilegedServiceAuditAlarm | ( | _In_ PSECURITY_SUBJECT_CONTEXT | SubjectContext, |
| _In_opt_ PUNICODE_STRING | SubsystemName, | ||
| _In_opt_ PUNICODE_STRING | ServiceName, | ||
| _In_ PTOKEN | Token, | ||
| _In_ PTOKEN | PrimaryToken, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
Performs an audit alarm to a privileged service request. This is a worker function.
- Parameters
-
[in] SubjectContext A security subject context used for the auditing process. [in] SubsystemName A Unicode string that represents the name of a subsystem that actuated the procedure of alarm auditing of a privileged service. [in] ServiceName A Unicode string that represents the name of a privileged service request for auditing. [in] Token An access token. [in] PrimaryToken A primary access token. [in] Privileges An array set of privileges used to check if the privileged service does actually have all the required set of privileges for security access. [in] AccessGranted When auditing is done, the function will return TRUE to the caller if access is granted, FALSE otherwise.
- Returns
- Nothing.
Definition at line 332 of file audit.c.
Referenced by NtPrivilegedServiceAuditAlarm(), and SePrivilegedServiceAuditAlarm().
◆ SepOpenObjectAuditAlarm()
| VOID NTAPI SepOpenObjectAuditAlarm | ( | _In_ PSECURITY_SUBJECT_CONTEXT | SubjectContext, |
| _In_ PUNICODE_STRING | SubsystemName, | ||
| _In_opt_ PVOID | HandleId, | ||
| _In_ PUNICODE_STRING | ObjectTypeName, | ||
| _In_ PUNICODE_STRING | ObjectName, | ||
| _In_opt_ PSECURITY_DESCRIPTOR | SecurityDescriptor, | ||
| _In_ PTOKEN | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ ACCESS_MASK | GrantedAccess, | ||
| _In_opt_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | ObjectCreation, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _Out_ PBOOLEAN | GenerateOnClose | ||
| ) |
Raises an alarm audit message when an object is about to be opened.
@unimplemented
- Parameters
-
[in] SubjectContext A security subject context for auditing. [in] SubsystemName A Unicode string that points to a name of the subsystem. [in] HandleId A handle to an ID used for identification instance for auditing. [in] ObjectTypeName A Unicode string that points to an object type name. [in] ObjectName The name of the object. [in] SecurityDescriptor A security descriptor. [in] ClientToken A client access token, representing the client we want to impersonate. [in] DesiredAccess The desired access rights masks requested by the caller. [in] GrantedAccess The granted access mask rights. [in] Privileges If specified, the function will use this set of privileges to audit. [in] ObjectCreation Set this to TRUE if the object has just been created. [in] AccessGranted Set this to TRUE if the access attempt was deemed as granted. [out] GenerateOnClose A boolean flag returned to the caller once audit generation procedure finishes.
- Returns
- Nothing.
Definition at line 1535 of file audit.c.
Referenced by NtOpenObjectAuditAlarm().
◆ SePrivilegedServiceAuditAlarm()
| VOID NTAPI SePrivilegedServiceAuditAlarm | ( | _In_opt_ PUNICODE_STRING | ServiceName, |
| _In_ PSECURITY_SUBJECT_CONTEXT | SubjectContext, | ||
| _In_ PPRIVILEGE_SET | PrivilegeSet, | ||
| _In_ BOOLEAN | AccessGranted | ||
| ) |
Performs an audit alarm to a privileged service request.
- Parameters
-
[in] ServiceName A Unicode string that represents the name of a privileged service request for auditing. [in] SubjectContext A security subject context used for the auditing process. [in] PrivilegeSet An array set of privileges used to check if the privileged service does actually have all the required set of privileges for security access. [in] AccessGranted When auditing is done, the function will return TRUE to the caller if access is granted, FALSE otherwise.
- Returns
- Nothing.
Definition at line 369 of file audit.c.
Referenced by SeCheckAuditPrivilege(), and SeSinglePrivilegeCheck().
◆ SePrivilegeObjectAuditAlarm()
| VOID NTAPI SePrivilegeObjectAuditAlarm | ( | _In_ HANDLE | Handle, |
| _In_ PSECURITY_SUBJECT_CONTEXT | SubjectContext, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PPRIVILEGE_SET | Privileges, | ||
| _In_ BOOLEAN | AccessGranted, | ||
| _In_ KPROCESSOR_MODE | CurrentMode | ||
| ) |
Raises an audit with alarm notification message when an object tries to acquire this privilege.
@unimplemented
- Parameters
-
[in] Handle A handle to an object. [in] SubjectContext The security subject context for auditing. [in] DesiredAccess The desired right access masks requested by the caller. [in] Privileges An array set of privileges for auditing. [out] AccessGranted When the auditing procedure routine ends, it returns TRUE to the caller if the object has the required privileges for access, FALSE otherwise. [in] CurrentMode Processor level access mode.
- Returns
- Nothing.
Definition at line 1321 of file audit.c.
Referenced by HasPrivilege(), ObpCreateHandle(), and SeCheckPrivilegedObject().
Variable Documentation
◆ SeSubsystemName
| UNICODE_STRING SeSubsystemName = RTL_CONSTANT_STRING(L"Security") |
Definition at line 17 of file audit.c.
Referenced by SePrivilegedServiceAuditAlarm().