#include "ps_x.h"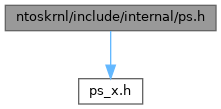
Go to the source code of this file.
Classes | |
| struct | _GET_SET_CTX_CONTEXT |
Macros | |
| #define | _PS_DEBUG_ 0x00 |
| #define | PS_THREAD_DEBUG 0x01 |
| #define | PS_PROCESS_DEBUG 0x02 |
| #define | PS_SECURITY_DEBUG 0x04 |
| #define | PS_JOB_DEBUG 0x08 |
| #define | PS_NOTIFICATIONS_DEBUG 0x10 |
| #define | PS_WIN32K_DEBUG 0x20 |
| #define | PS_STATE_DEBUG 0x40 |
| #define | PS_QUOTA_DEBUG 0x80 |
| #define | PS_KILL_DEBUG 0x100 |
| #define | PS_REF_DEBUG 0x200 |
| #define | PSTRACE(x, fmt, ...) DPRINT(fmt, ##__VA_ARGS__) |
| #define | PSREFTRACE(x) |
| #define | PSP_MAX_CREATE_THREAD_NOTIFY 8 |
| #define | PSP_MAX_LOAD_IMAGE_NOTIFY 8 |
| #define | PSP_MAX_CREATE_PROCESS_NOTIFY 8 |
| #define | PSP_JOB_SCHEDULING_CLASSES 10 |
| #define | PSP_NON_PAGED_POOL_QUOTA_THRESHOLD 0x10000 |
| #define | PSP_PAGED_POOL_QUOTA_THRESHOLD 0x80000 |
Typedefs | |
| typedef struct _GET_SET_CTX_CONTEXT | GET_SET_CTX_CONTEXT |
| typedef struct _GET_SET_CTX_CONTEXT * | PGET_SET_CTX_CONTEXT |
Macro Definition Documentation
◆ _PS_DEBUG_
◆ PS_JOB_DEBUG
◆ PS_KILL_DEBUG
◆ PS_NOTIFICATIONS_DEBUG
◆ PS_PROCESS_DEBUG
◆ PS_QUOTA_DEBUG
◆ PS_REF_DEBUG
◆ PS_SECURITY_DEBUG
◆ PS_STATE_DEBUG
◆ PS_THREAD_DEBUG
◆ PS_WIN32K_DEBUG
◆ PSP_JOB_SCHEDULING_CLASSES
◆ PSP_MAX_CREATE_PROCESS_NOTIFY
◆ PSP_MAX_CREATE_THREAD_NOTIFY
◆ PSP_MAX_LOAD_IMAGE_NOTIFY
◆ PSP_NON_PAGED_POOL_QUOTA_THRESHOLD
◆ PSP_PAGED_POOL_QUOTA_THRESHOLD
◆ PSREFTRACE
◆ PSTRACE
Typedef Documentation
◆ GET_SET_CTX_CONTEXT
◆ PGET_SET_CTX_CONTEXT
| typedef struct _GET_SET_CTX_CONTEXT * PGET_SET_CTX_CONTEXT |
Function Documentation
◆ ApphelpCacheInitialize()
Definition at line 439 of file apphelp.c.
Referenced by IoInitSystem().
◆ ApphelpCacheShutdown()
Definition at line 465 of file apphelp.c.
Referenced by PopGracefulShutdown().
◆ PsChangeQuantumTable()
Definition at line 235 of file process.c.
Referenced by PspInitPhase0(), and SSI_DEF().
◆ PsChargeProcessPageFileQuota()
Charges the process page file quota. The function is used internally by the kernel.
- Parameters
-
[in] Process The process which page file quota is to be charged. [in] Amount The amount of page file quota to charge.
- Returns
- Returns STATUS_SUCCESS if quota charging has been done with success, otherwise a NTSTATUS code of STATUS_PAGEFILE_QUOTA_EXCEEDED is returned.
Definition at line 738 of file quota.c.
◆ PsChargeSharedPoolQuota()
| PEPROCESS_QUOTA_BLOCK NTAPI PsChargeSharedPoolQuota | ( | _In_ PEPROCESS | Process, |
| _In_ SIZE_T | AmountToChargePaged, | ||
| _In_ SIZE_T | AmountToChargeNonPaged | ||
| ) |
Charges the shared (paged and non paged) pool quotas. The function is used exclusively by the Object Manager to manage quota charges handling of objects.
- Parameters
-
[in] Process The process which quotas are to be charged within its quota block. [in] AmountToChargePaged The amount of paged quotas quotas to be charged. [in] AmountToChargeNonPaged The amount of non paged quotas to be charged.
- Returns
- Returns the charged quota block, which it'll be used by the Object Manager to attach the charged quotas information to the object. If the function fails to charge quotas, NULL is returned to the caller.
Definition at line 674 of file quota.c.
Referenced by ObpChargeQuotaForObject().
◆ PsExitSpecialApc()
| VOID NTAPI PsExitSpecialApc | ( | PKAPC | Apc, |
| PKNORMAL_ROUTINE * | NormalRoutine, | ||
| PVOID * | NormalContext, | ||
| PVOID * | SystemArgument1, | ||
| PVOID * | SystemArgument2 | ||
| ) |
Referenced by KiInsertQueueApc().
◆ PsGetNextProcess()
Definition at line 128 of file process.c.
Referenced by DbgkpCloseObject(), ExpDebuggerWorker(), PopGracefulShutdown(), PsChangeQuantumTable(), PspShutdownProcessManager(), and QSI_DEF().
◆ PsGetNextProcessThread()
Definition at line 75 of file process.c.
Referenced by DbgkpPostFakeThreadMessages(), DbgkpSetProcessDebugObject(), ExSwapinWorkerThreads(), NtSetInformationThread(), NtTerminateProcess(), PspTerminateProcess(), PsResumeProcess(), and PsSuspendProcess().
◆ PsIdleThreadMain()
◆ PsInitSystem()
| BOOLEAN NTAPI PsInitSystem | ( | IN PLOADER_PARAMETER_BLOCK | LoaderBlock | ) |
Definition at line 532 of file psmgr.c.
Referenced by ExpInitializeExecutive(), and Phase1InitializationDiscard().
◆ PsLocateSystemDll()
Definition at line 187 of file psmgr.c.
Referenced by IoInitSystem().
◆ PsOpenTokenOfProcess()
Definition at line 471 of file security.c.
Referenced by NtOpenProcessTokenEx().
◆ PspCreateProcess()
| NTSTATUS NTAPI PspCreateProcess | ( | OUT PHANDLE | ProcessHandle, |
| IN ACCESS_MASK | DesiredAccess, | ||
| IN POBJECT_ATTRIBUTES ObjectAttributes | OPTIONAL, | ||
| IN HANDLE ParentProcess | OPTIONAL, | ||
| IN ULONG | Flags, | ||
| IN HANDLE SectionHandle | OPTIONAL, | ||
| IN HANDLE DebugPort | OPTIONAL, | ||
| IN HANDLE ExceptionPort | OPTIONAL, | ||
| IN BOOLEAN | InJob | ||
| ) |
Definition at line 347 of file process.c.
Referenced by NtCreateProcessEx(), PsCreateSystemProcess(), and PspInitPhase0().
◆ PspDeleteJob()
Referenced by PspInitPhase0().
◆ PspDeleteProcess()
Definition at line 253 of file kill.c.
Referenced by PspInitPhase0().
◆ PspDeleteProcessSecurity()
Definition at line 30 of file security.c.
Referenced by PspDeleteProcess().
◆ PspDeleteThread()
Definition at line 391 of file kill.c.
Referenced by PspInitPhase0().
◆ PspDeleteThreadSecurity()
Definition at line 46 of file security.c.
Referenced by PspDeleteThread().
◆ PspDereferenceQuotaBlock()
| VOID NTAPI PspDereferenceQuotaBlock | ( | _In_opt_ PEPROCESS | Process, |
| _In_ PEPROCESS_QUOTA_BLOCK | QuotaBlock | ||
| ) |
De-references a quota block when quotas have been returned back because of an object de-allocation or when a process gets destroyed. If the last instance that held up the block gets de-referenced the function will perform a cleanup against that block and it'll free the quota block from memory.
- Parameters
-
[in] Process A pointer to a process that de-references the quota block. [in] QuotaBlock A pointer to a quota block that is to be de-referenced. This block can come from a process that references it or an object.
- Returns
- Nothing.
Definition at line 553 of file quota.c.
Referenced by PspDeleteProcess(), and PsReturnSharedPoolQuota().
◆ PspExitProcess()
Definition at line 1083 of file kill.c.
Referenced by PspDeleteProcess(), and PspExitThread().
◆ PspExitProcessFromJob()
◆ PspExitThread()
Definition at line 458 of file kill.c.
Referenced by PsExitSpecialApc(), and PspTerminateThreadByPointer().
◆ PspGetOrSetContextKernelRoutine()
| VOID NTAPI PspGetOrSetContextKernelRoutine | ( | IN PKAPC | Apc, |
| IN OUT PKNORMAL_ROUTINE * | NormalRoutine, | ||
| IN OUT PVOID * | NormalContext, | ||
| IN OUT PVOID * | SystemArgument1, | ||
| IN OUT PVOID * | SystemArgument2 | ||
| ) |
Definition at line 38 of file psctx.c.
Referenced by PsGetContextThread(), and PsSetContextThread().
◆ PspInheritQuota()
Referenced by PspCreateProcess().
◆ PspInitializeJobStructures()
Definition at line 111 of file job.c.
Referenced by PspInitPhase0().
◆ PspInitializeProcessSecurity()
Definition at line 71 of file security.c.
Referenced by PspCreateProcess().
◆ PspIsProcessExiting()
Definition at line 1076 of file kill.c.
Referenced by MmpPageOutPhysicalAddress().
◆ PspMapSystemDll()
| NTSTATUS NTAPI PspMapSystemDll | ( | IN PEPROCESS | Process, |
| OUT PVOID * | DllBase, | ||
| IN BOOLEAN | UseLargePages | ||
| ) |
Referenced by PspCreateProcess().
◆ PspReapRoutine()
Definition at line 167 of file kill.c.
Referenced by PspInitPhase0().
◆ PspRemoveProcessFromJob()
◆ PspSetPrimaryToken()
| NTSTATUS NTAPI PspSetPrimaryToken | ( | IN PEPROCESS | Process, |
| IN HANDLE TokenHandle | OPTIONAL, | ||
| IN PACCESS_TOKEN Token | OPTIONAL | ||
| ) |
Definition at line 215 of file security.c.
Referenced by NtSetInformationProcess().
◆ PspSetQuotaLimits()
| NTSTATUS NTAPI PspSetQuotaLimits | ( | _In_ PEPROCESS | Process, |
| _In_ ULONG | Unused, | ||
| _In_ PVOID | QuotaLimits, | ||
| _In_ ULONG | QuotaLimitsLength, | ||
| _In_ KPROCESSOR_MODE | PreviousMode | ||
| ) |
This function adjusts the working set limits of a process and sets up new quota limits when necessary. The function is used when the caller requests to set up new working set sizes.
- Parameters
-
[in] Process The process which quota limits or working set sizes are to be changed. [in] Unused This parameter is unused. [in] QuotaLimits An arbitrary pointer that points to a quota limits structure, needed to determine on setting up new working set sizes. [in] QuotaLimitsLength The length of QuotaLimits buffer, which size is expressed in bytes. [in] PreviousMode The processor level access mode.
- Returns
- Returns STATUS_SUCCESS if the function has completed successfully. STATUS_INVALID_PARAMETER is returned if the caller has given a quota limits structure with invalid data. STATUS_INFO_LENGTH_MISMATCH is returned if the length of QuotaLimits pointed by QuotaLimitsLength is not right. STATUS_PRIVILEGE_NOT_HELD is returned if the calling thread of the process doesn't hold the necessary right privilege to increase quotas. STATUS_NO_MEMORY is returned if a memory pool allocation has failed. A failure NTSTATUS code is returned otherwise.
Definition at line 1045 of file quota.c.
Referenced by NtSetInformationProcess().
◆ PspShutdownProcessManager()
Definition at line 135 of file kill.c.
◆ PspSystemThreadStartup()
| VOID NTAPI PspSystemThreadStartup | ( | PKSTART_ROUTINE | StartRoutine, |
| PVOID | StartContext | ||
| ) |
◆ PspTerminateThreadByPointer()
| NTSTATUS NTAPI PspTerminateThreadByPointer | ( | IN PETHREAD | Thread, |
| IN NTSTATUS | ExitStatus, | ||
| IN BOOLEAN | bSelf | ||
| ) |
Definition at line 996 of file kill.c.
Referenced by NtTerminateProcess(), NtTerminateThread(), PspSystemThreadStartup(), PspTerminateProcess(), PspUserThreadStartup(), and PsTerminateSystemThread().
◆ PsReferenceEffectiveToken()
| PACCESS_TOKEN NTAPI PsReferenceEffectiveToken | ( | IN PETHREAD | Thread, |
| OUT IN PTOKEN_TYPE | TokenType, | ||
| OUT PBOOLEAN | EffectiveOnly, | ||
| OUT PSECURITY_IMPERSONATION_LEVEL | ImpersonationLevel | ||
| ) |
Definition at line 802 of file security.c.
Referenced by SeCreateClientSecurity().
◆ PsReferenceProcessFilePointer()
| NTSTATUS NTAPI PsReferenceProcessFilePointer | ( | _In_ PEPROCESS | Process, |
| _Outptr_ PFILE_OBJECT * | FileObject | ||
| ) |
Definition at line 24 of file query.c.
Referenced by NtQueryInformationProcess(), and SeLocateProcessImageName().
◆ PsResumeThread()
Definition at line 32 of file state.c.
Referenced by DbgkpPostFakeThreadMessages(), DbgkpWakeTarget(), and NtResumeThread().
◆ PsReturnProcessPageFileQuota()
Returns the page file quota that the process was taking up. The function is used exclusively by the kernel.
- Parameters
-
[in] Process The process which pagefile quota is to be returned. [in] Amount The amount of quotas to return from a process.
- Returns
- Returns STATUS_SUCCESS.
Definition at line 993 of file quota.c.
◆ PsReturnSharedPoolQuota()
| VOID NTAPI PsReturnSharedPoolQuota | ( | _In_ PEPROCESS_QUOTA_BLOCK | QuotaBlock, |
| _In_ SIZE_T | AmountToReturnPaged, | ||
| _In_ SIZE_T | AmountToReturnNonPaged | ||
| ) |
Returns the shared (paged and non paged) pool quotas. The function is used exclusively by the Object Manager to manage quota returns handling of objects.
- Parameters
-
[in] QuotaBlock The quota block which quotas are to be returned. [in] AmountToReturnPaged The amount of paged quotas quotas to be returned. [in] AmountToReturnNonPaged The amount of non paged quotas to be returned.
- Returns
- Nothing.
Definition at line 621 of file quota.c.
Referenced by ObpDeallocateObject().
◆ PsSuspendThread()
Definition at line 48 of file state.c.
Referenced by DbgkpPostFakeThreadMessages(), NtSuspendThread(), and PsSuspendProcess().
◆ PsTerminateProcess()
Definition at line 126 of file kill.c.
Referenced by DbgkpCloseObject(), and ExpDebuggerWorker().
Variable Documentation
◆ _PsProcessType
| POBJECT_TYPE _PsProcessType |
◆ _PsThreadType
|
extern |
◆ PsActiveProcessHead
|
extern |
Definition at line 22 of file process.c.
Referenced by KdbpCmdProc(), PsGetNextProcess(), PspCreateProcess(), and PspInitPhase0().
◆ PsDefaultSystemLocaleId
|
extern |
Definition at line 20 of file locale.c.
Referenced by CmGetSystemControlValues(), MiSessionCreateInternal(), NtQueryDefaultLocale(), and NtSetDefaultLocale().
◆ PsDefaultThreadLocaleId
|
extern |
Definition at line 24 of file locale.c.
Referenced by _IRQL_requires_max_(), CmGetSystemControlValues(), MmCreateTeb(), and MmGetSessionLocaleId().
◆ PsIdleProcess
|
extern |
Definition at line 51 of file psmgr.c.
Referenced by MmInitSystem(), PopGracefulShutdown(), PspInitPhase0(), PspShutdownProcessManager(), and QSI_DEF().
◆ PsImageNotifyEnabled
|
extern |
Definition at line 18 of file psnotify.c.
Referenced by DbgkCreateThread(), MmLoadSystemImage(), and PsSetLoadImageNotifyRoutine().
◆ PsJobType
|
extern |
Definition at line 20 of file job.c.
Referenced by PspInitPhase0(), and TestWin2003ObjectTypes().
◆ PsLoadedModuleList
|
extern |
Definition at line 21 of file sysldr.c.
Referenced by IopInitializeBuiltinDriver(), KdbpSymFindModule(), KdbSymInit(), KdInitSystem(), KiInitModuleList(), KiPcToFileHeader(), MiBuildImportsForBootDrivers(), MiFindInitializationCode(), MiInitializeLoadedModuleList(), MiLookupDataTableEntry(), MiProcessLoaderEntry(), MiResolveImageReferences(), MiSnapThunk(), MmGetSystemRoutineAddress(), MmInitSystem(), MmLoadSystemImage(), and QSI_DEF().
◆ PsLoadedModuleResource
|
extern |
Definition at line 24 of file sysldr.c.
Referenced by MiFindInitializationCode(), MiInitializeLoadedModuleList(), MiProcessLoaderEntry(), MmGetSystemRoutineAddress(), MmInitSystem(), and QSI_DEF().
◆ PsLoadedModuleSpinLock
|
extern |
Definition at line 23 of file sysldr.c.
Referenced by KdbpSymFindModule(), KdbSymInit(), MiInitializeLoadedModuleList(), MiProcessLoaderEntry(), and RtlPcToFileHeader().
◆ PsNtDllPathName
|
extern |
Definition at line 45 of file psmgr.c.
Referenced by DbgkCreateThread(), and PsLocateSystemDll().
◆ PsNtosImageBase
|
extern |
Definition at line 25 of file sysldr.c.
Referenced by KdInitSystem(), and MiInitializeLoadedModuleList().
◆ PspActiveProcessMutex
|
extern |
Definition at line 23 of file process.c.
Referenced by PsGetNextProcess(), PspCreateProcess(), PspDeleteProcess(), and PspInitPhase0().
◆ PspBootAccessToken
|
extern |
Definition at line 17 of file security.c.
Referenced by PspInitializeProcessSecurity(), and PspInitPhase0().
◆ PspCidTable
|
extern |
Definition at line 48 of file psmgr.c.
Referenced by PsLookupProcessByProcessId(), PsLookupProcessThreadByCid(), PsLookupThreadByThreadId(), PspCreateProcess(), PspCreateThread(), PspDeleteProcess(), PspDeleteThread(), and PspInitPhase0().
◆ PspDefaultQuotaBlock
|
extern |
Definition at line 16 of file quota.c.
Referenced by NtQueryInformationProcess(), PsInitializeQuotaSystem(), PspChargeProcessQuotaSpecifiedPool(), PspDereferenceQuotaBlock(), PspInheritQuota(), PspReturnProcessQuotaSpecifiedPool(), and PspSetQuotaLimits().
◆ PspJobMapping
|
extern |
Definition at line 41 of file job.c.
Referenced by PspInitPhase0().
◆ PspJobSchedulingClasses
|
extern |
Definition at line 27 of file job.c.
Referenced by PsChangeQuantumTable(), and PspComputeQuantumAndPriority().
◆ PspLegoNotifyRoutine
|
extern |
Definition at line 24 of file psnotify.c.
Referenced by PspRunLegoRoutine(), and PsSetLegoNotifyRoutine().
◆ PspLoadImageNotifyRoutine
|
extern |
Definition at line 23 of file psnotify.c.
Referenced by PspInitPhase0(), PspRunLoadImageNotifyRoutines(), PsRemoveLoadImageNotifyRoutine(), and PsSetLoadImageNotifyRoutine().
◆ PspProcessNotifyRoutine
|
extern |
Definition at line 22 of file psnotify.c.
Referenced by PspInitPhase0(), PspRunCreateProcessNotifyRoutines(), and PsSetCreateProcessNotifyRoutine().
◆ PspProcessNotifyRoutineCount
| ULONG PspProcessNotifyRoutineCount |
Definition at line 463 of file ps.h.
Referenced by PspRunCreateProcessNotifyRoutines().
◆ PspReaperListHead
|
extern |
◆ PspReaperWorkItem
|
extern |
Definition at line 20 of file kill.c.
Referenced by KeTerminateThread(), and PspInitPhase0().
◆ PspReaping
|
extern |
◆ PsPrioritySeparation
|
extern |
Definition at line 28 of file process.c.
Referenced by KiDeferredReadyThread(), PsChangeQuantumTable(), and PspComputeQuantumAndPriority().
◆ PspSystemDllBase
|
extern |
Definition at line 41 of file psmgr.c.
Referenced by CODE_SEG(), DbgkCreateThread(), PsLocateSystemDll(), and PspUserThreadStartup().
◆ PspSystemDllEntryPoint
|
extern |
Definition at line 43 of file psmgr.c.
Referenced by PspInitializeSystemDll(), and PspUserThreadStartup().
◆ PspThreadNotifyRoutine
|
extern |
Definition at line 21 of file psnotify.c.
Referenced by PspInitPhase0(), PspRunCreateThreadNotifyRoutines(), PsRemoveCreateThreadNotifyRoutine(), and PsSetCreateThreadNotifyRoutine().
◆ PspThreadNotifyRoutineCount
|
extern |
Definition at line 19 of file psnotify.c.
Referenced by PspRunCreateThreadNotifyRoutines(), PsRemoveCreateThreadNotifyRoutine(), and PsSetCreateThreadNotifyRoutine().
◆ PspTraceLevel
◆ PspUseJobSchedulingClasses
|
extern |
Definition at line 25 of file job.c.
Referenced by PsChangeQuantumTable(), and PspComputeQuantumAndPriority().
◆ PspW32ProcessCallout
|
extern |
Definition at line 18 of file win32.c.
Referenced by PsConvertToGuiThread(), PsEstablishWin32Callouts(), and PspExitThread().
◆ PspW32ThreadCallout
|
extern |
Definition at line 19 of file win32.c.
Referenced by PsConvertToGuiThread(), PsEstablishWin32Callouts(), and PspExitThread().
◆ PsRawPrioritySeparation
|
extern |
Definition at line 27 of file process.c.
Referenced by PspInitPhase0().
◆ ShortPsLockDelay
|
extern |