#include <ntoskrnl.h>#include <debug.h>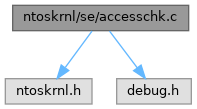
Go to the source code of this file.
Macros | |
| #define | NDEBUG |
Functions | |
| static VOID | SepDenyAccessObjectTypeResultList (_Inout_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ ACCESS_MASK AccessMask, _In_opt_ PGUID ObjectTypeGuid) |
| Denies access of a target object and the children objects in an object type list. | |
| static VOID | SepAllowAccessObjectTypeResultList (_Inout_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ ACCESS_MASK AccessMask, _In_opt_ PGUID ObjectTypeGuid) |
| Allows access of a target object and the children objects in an object type list. | |
| static VOID | SepDenyAccessObjectTypeList (_Inout_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ ACCESS_MASK AccessMask, _In_opt_ PGUID ObjectTypeGuid, _Out_opt_ PBOOLEAN BreakOnDeny) |
| Denies access of a target object in the object type list. This access is denied for the whole hierarchy in the list. | |
| static VOID | SepAllowAccessObjectTypeList (_Inout_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ ACCESS_MASK AccessMask, _In_ BOOLEAN RemoveRemainingRights, _In_opt_ PGUID ObjectTypeGuid) |
| Allows access of a target object in the object type list. This access is allowed for the whole hierarchy in the list. | |
| static VOID | SepAnalyzeAcesFromDacl (_In_ ACCESS_CHECK_RIGHT_TYPE ActionType, _In_ ACCESS_MASK RemainingAccess, _In_ PACL Dacl, _In_ PACCESS_TOKEN AccessToken, _In_ PACCESS_TOKEN PrimaryAccessToken, _In_ BOOLEAN IsTokenRestricted, _In_opt_ PSID PrincipalSelfSid, _In_ PGENERIC_MAPPING GenericMapping, _In_opt_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ BOOLEAN UseResultList, _Inout_ PACCESS_CHECK_RIGHTS AccessCheckRights) |
| Analyzes an access control entry that is present in a discretionary access control list (DACL) for access right masks of each entry with the purpose to judge whether the calling thread can be warranted access check to a certain object or not. | |
| static BOOLEAN | SepAccessCheckWorker (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_opt_ PACCESS_TOKEN ClientAccessToken, _In_ PACCESS_TOKEN PrimaryAccessToken, _In_opt_ PSID PrincipalSelfSid, _In_ ACCESS_MASK DesiredAccess, _In_opt_ POBJECT_TYPE_LIST_INTERNAL ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ ACCESS_MASK PreviouslyGrantedAccess, _In_ PGENERIC_MAPPING GenericMapping, _In_ KPROCESSOR_MODE AccessMode, _In_ BOOLEAN UseResultList, _Out_opt_ PPRIVILEGE_SET *Privileges, _Out_ PACCESS_MASK GrantedAccessList, _Out_ PNTSTATUS AccessStatusList) |
| Private worker function that determines whether security access rights can be givento the calling thread in order to access an object depending on the security descriptor and other security context entities, such as an owner. This function is the heart and brain of the whole access check algorithm in the kernel. | |
| static ULONG | SepGetPrivilegeSetLength (_In_ PPRIVILEGE_SET PrivilegeSet) |
| Retrieves the length size of a set list of privileges structure. | |
| static NTSTATUS | SepAccessCheck (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_ HANDLE ClientToken, _In_opt_ PSID PrincipalSelfSid, _In_ ACCESS_MASK DesiredAccess, _In_ PGENERIC_MAPPING GenericMapping, _Out_writes_bytes_(*PrivilegeSetLength) PPRIVILEGE_SET PrivilegeSet, _Inout_ PULONG PrivilegeSetLength, _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ BOOLEAN UseResultList, _Out_ PACCESS_MASK GrantedAccess, _Out_ PNTSTATUS AccessStatus) |
| Internal function that performs a security check against the client who requests access on a resource object. This function is used by access check NT system calls. | |
| BOOLEAN NTAPI | SeAccessCheck (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_ PSECURITY_SUBJECT_CONTEXT SubjectSecurityContext, _In_ BOOLEAN SubjectContextLocked, _In_ ACCESS_MASK DesiredAccess, _In_ ACCESS_MASK PreviouslyGrantedAccess, _Out_ PPRIVILEGE_SET *Privileges, _In_ PGENERIC_MAPPING GenericMapping, _In_ KPROCESSOR_MODE AccessMode, _Out_ PACCESS_MASK GrantedAccess, _Out_ PNTSTATUS AccessStatus) |
| Determines whether security access rights can be given to an object depending on the security descriptor and other security context entities, such as an owner. | |
| BOOLEAN NTAPI | SeFastTraverseCheck (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_ PACCESS_STATE AccessState, _In_ ACCESS_MASK DesiredAccess, _In_ KPROCESSOR_MODE AccessMode) |
| Determines whether security access rights can be given to an object depending on the security descriptor. Unlike the regular access check procedure in the NT kernel, the fast traverse check is a faster way to quickly check if access can be made into an object. | |
| NTSTATUS NTAPI | NtAccessCheck (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_ HANDLE ClientToken, _In_ ACCESS_MASK DesiredAccess, _In_ PGENERIC_MAPPING GenericMapping, _Out_writes_bytes_(*PrivilegeSetLength) PPRIVILEGE_SET PrivilegeSet, _Inout_ PULONG PrivilegeSetLength, _Out_ PACCESS_MASK GrantedAccess, _Out_ PNTSTATUS AccessStatus) |
| Determines whether security access can be granted to a client that requests such access on an object. | |
| NTSTATUS NTAPI | NtAccessCheckByType (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_opt_ PSID PrincipalSelfSid, _In_ HANDLE ClientToken, _In_ ACCESS_MASK DesiredAccess, _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ PGENERIC_MAPPING GenericMapping, _Out_writes_bytes_(*PrivilegeSetLength) PPRIVILEGE_SET PrivilegeSet, _Inout_ PULONG PrivilegeSetLength, _Out_ PACCESS_MASK GrantedAccess, _Out_ PNTSTATUS AccessStatus) |
| Determines whether security access can be granted to a client that requests such access on the object type list. The access is either granted or denied for the whole object hierarchy in the list. | |
| NTSTATUS NTAPI | NtAccessCheckByTypeResultList (_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_opt_ PSID PrincipalSelfSid, _In_ HANDLE ClientToken, _In_ ACCESS_MASK DesiredAccess, _In_reads_(ObjectTypeListLength) POBJECT_TYPE_LIST ObjectTypeList, _In_ ULONG ObjectTypeListLength, _In_ PGENERIC_MAPPING GenericMapping, _Out_writes_bytes_(*PrivilegeSetLength) PPRIVILEGE_SET PrivilegeSet, _Inout_ PULONG PrivilegeSetLength, _Out_writes_(ObjectTypeListLength) PACCESS_MASK GrantedAccess, _Out_writes_(ObjectTypeListLength) PNTSTATUS AccessStatus) |
| Determines whether security access can be granted to a client that requests such access on the object type list. Unlike the NtAccessCheckByType variant, this function will grant or deny access to each individual object and sub-object in the list. | |
Macro Definition Documentation
◆ NDEBUG
| #define NDEBUG |
Definition at line 13 of file accesschk.c.
Function Documentation
◆ NtAccessCheck()
| NTSTATUS NTAPI NtAccessCheck | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on an object.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2214 of file accesschk.c.
Referenced by AccessCheck(), AccessCheckEmptyMappingTest(), and CheckTokenMembership().
◆ NtAccessCheckByType()
| NTSTATUS NTAPI NtAccessCheckByType | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_reads_opt_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on the object type list. The access is either granted or denied for the whole object hierarchy in the list.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2254 of file accesschk.c.
Referenced by AccessCheckByType(), AccessGrantedMultipleObjectsTests(), AccessGrantedNoDaclTests(), AccessGrantedTests(), DenyAccessTests(), and ParamsValidationTests().
◆ NtAccessCheckByTypeResultList()
| NTSTATUS NTAPI NtAccessCheckByTypeResultList | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_opt_ PSID | PrincipalSelfSid, | ||
| _In_ HANDLE | ClientToken, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_reads_(ObjectTypeListLength) POBJECT_TYPE_LIST | ObjectTypeList, | ||
| _In_ ULONG | ObjectTypeListLength, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _Out_writes_bytes_ *PrivilegeSetLength PPRIVILEGE_SET | PrivilegeSet, | ||
| _Inout_ PULONG | PrivilegeSetLength, | ||
| _Out_writes_(ObjectTypeListLength) PACCESS_MASK | GrantedAccess, | ||
| _Out_writes_(ObjectTypeListLength) PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access can be granted to a client that requests such access on the object type list. Unlike the NtAccessCheckByType variant, this function will grant or deny access to each individual object and sub-object in the list.
- Remarks
- For more documentation details about the parameters and overall function behavior, see SepAccessCheck.
Definition at line 2297 of file accesschk.c.
Referenced by AccessCheckByTypeResultList(), DenyAccessTests(), GrantedAccessTests(), and ParamValidationNoObjsList().
◆ SeAccessCheck()
| BOOLEAN NTAPI SeAccessCheck | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_ PSECURITY_SUBJECT_CONTEXT | SubjectSecurityContext, | ||
| _In_ BOOLEAN | SubjectContextLocked, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ ACCESS_MASK | PreviouslyGrantedAccess, | ||
| _Out_ PPRIVILEGE_SET * | Privileges, | ||
| _In_ PGENERIC_MAPPING | GenericMapping, | ||
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _Out_ PACCESS_MASK | GrantedAccess, | ||
| _Out_ PNTSTATUS | AccessStatus | ||
| ) |
Determines whether security access rights can be given to an object depending on the security descriptor and other security context entities, such as an owner.
- Parameters
-
[in] SecurityDescriptor Security descriptor of the object that is being accessed. [in] SubjectSecurityContext The captured subject security context. [in] SubjectContextLocked If set to TRUE, the caller acknowledges that the subject context has already been locked by the caller himself. If set to FALSE, the function locks the subject context. [in] DesiredAccess Access right bitmask that the calling thread wants to acquire. [in] PreviouslyGrantedAccess The access rights previously acquired in the past. [out] Privileges The returned set of privileges. [in] GenericMapping The generic mapping of access rights of an object type. [in] AccessMode The processor request level mode. [out] GrantedAccess A list of granted access rights. [out] AccessStatus The returned status code specifying why access cannot be made onto an object (if said access is denied in the first place).
- Returns
- Returns TRUE if access onto the specific object is allowed, FALSE otherwise.
Definition at line 1994 of file accesschk.c.
Referenced by create_stream(), FatExplicitDeviceAccessGranted(), file_create(), IopParseDevice(), NpCreateClientEnd(), NpCreateExistingNamedPipe(), ObCheckCreateObjectAccess(), ObCheckObjectAccess(), ObpCheckObjectReference(), ObpCheckTraverseAccess(), open_file2(), PspCreateProcess(), PspCreateThread(), PspSetPrimaryToken(), set_link_information(), set_rename_information(), START_TEST(), and UDFCheckAccessRights().
◆ SeFastTraverseCheck()
| BOOLEAN NTAPI SeFastTraverseCheck | ( | _In_ PSECURITY_DESCRIPTOR | SecurityDescriptor, |
| _In_ PACCESS_STATE | AccessState, | ||
| _In_ ACCESS_MASK | DesiredAccess, | ||
| _In_ KPROCESSOR_MODE | AccessMode | ||
| ) |
Determines whether security access rights can be given to an object depending on the security descriptor. Unlike the regular access check procedure in the NT kernel, the fast traverse check is a faster way to quickly check if access can be made into an object.
- Parameters
-
[in] SecurityDescriptor Security descriptor of the object that is being accessed. [in] AccessState An access state to determine if the access token in the current security context of the object is an restricted token. [in] DesiredAccess The access right bitmask where the calling thread wants to acquire. [in] AccessMode Process level request mode.
- Returns
- Returns TRUE if access onto the specific object is allowed, FALSE otherwise.
Definition at line 2138 of file accesschk.c.
Referenced by IopParseDevice(), and ObpCheckTraverseAccess().
◆ SepAccessCheck()
|
static |
Internal function that performs a security check against the client who requests access on a resource object. This function is used by access check NT system calls.
- Parameters
-
[in] SecurityDescriptor A pointer to a security descriptor that identifies the security information of an object being accessed. This function walks through this descriptor for any ACLs and respective access rights if access can be granted. [in] ClientToken A handle to an access token, that identifies the client of which requests access to the target object. [in] PrincipalSelfSid A pointer to a principal self SID. This parameter can be NULL if the associated object being checked for access does not represent a principal. [in] DesiredAccess The access right bitmask where the client wants to acquire. This can be an OR'ed set of multiple access rights or MAXIMUM_ALLOWED to request all of possible access rights the target object allows. If only some rights were granted but not all the access is deemed as denied. [in] GenericMapping The generic mapping of access rights of an object type. [out] PrivilegeSet A pointer to a set of privileges that were used to perform the access check, returned to caller. This function will return no privileges (privilege count set to 0) if no privileges were used to accomplish the access check. This parameter must not be NULL! [in,out] PrivilegeSetLength The total length size of a set of privileges. This length represents the count of elements in the privilege set array. [in] ObjectTypeList A pointer to a given object type list. If this parameter is not NULL the function will perform an access check against the main object and sub-objects of this list. If this parameter is NULL and ObjectTypeListLength is 0, the function will perform a normal access check instead. [in] ObjectTypeListLength The length of the object type list array, pointed by ObjectTypeList. This length in question represents the number of elements in such array. This parameter must be 0 if no array list is provided. [in] UseResultList If this parameter is set to TRUE, the function will return the GrantedAccess and AccessStatus parameter as arrays of granted rights and status value for each individual object element pointed by ObjectTypeList. [out] GrantedAccess A pointer to granted access rights, returned to the caller. If ObjectTypeList is not NULL this paramater is an array of granted access rights for the object and each individual sub-object of the list. [out] AccessStatus A pointer to a status code, returned to the caller. This status code represents whether access is granted or denied to the client on the target object. The difference between the status code of the function is that code indicates whether the function has successfully completed the access check operation. If ObjectTypeList is not NULL, this parameter is an array of access status for the object and each individual sub-object of the list.
- Returns
- Returns STATUS_SUCCESS if access check has been done without problems and that the object can be accessed. STATUS_GENERIC_NOT_MAPPED is returned if no generic access right is mapped. STATUS_NO_IMPERSONATION_TOKEN is returned if the token from the handle is not an impersonation token. STATUS_BAD_IMPERSONATION_LEVEL is returned if the token cannot be impersonated because the current security impersonation level doesn't permit so. STATUS_INVALID_SECURITY_DESCR is returned if the security descriptor given to the call is not a valid one. STATUS_BUFFER_TOO_SMALL is returned if the buffer to the captured privileges has a length that is less than the required size of the set of privileges. STATUS_INVALID_PARAMETER is returned if the caller did not provide an object type list but the caller wanted to invoke an object type result list access check, or if the list is out of order or the list is invalid. A failure NTSTATUS code is returned otherwise.
- Remarks
- The function performs an access check against the object type list, if provided, depending on the UseResultList parameter. That is, if that parameter was set to TRUE the function will either grant or deny access to each individual sub-object and return an array of access status and granted rights for the corresponding object type list. Otherwise the function will grant or deny access to the object type list hierarchy as a whole.
Definition at line 1592 of file accesschk.c.
Referenced by NtAccessCheck(), NtAccessCheckByType(), and NtAccessCheckByTypeResultList().
◆ SepAccessCheckWorker()
|
static |
Private worker function that determines whether security access rights can be givento the calling thread in order to access an object depending on the security descriptor and other security context entities, such as an owner. This function is the heart and brain of the whole access check algorithm in the kernel.
- Parameters
-
[in] ClientAccessToken A pointer to a client (thread) access token that requests access rights of an object or subset of multiple objects. [in] PrimaryAccessToken A pointer to a primary access token that describes the primary security context of the main calling process. [in] PrincipalSelfSid A pointer to a security identifier that represents a security principal, that is, a user object associated with its security descriptor. [in] DesiredAccess The access rights desired by the calling thread to acquire in order to access an object. [in] ObjectTypeList An array list of object types to be checked against for access. The function will act accordingly in this case by checking each sub-object of an object of primary level and such. If this parameter is NULL, the function will perform a normal access check against the target object itself. [in] ObjectTypeListLength The length of a object type list. Such length represents the number of elements in this list. [in] PreviouslyGrantedAccess The access rights previously acquired in the past. If this parameter is 0, it is deemed that the calling thread hasn't acquired any rights. Access checks are more tighten in this case. [in] GenericMapping A pointer to a generic mapping of access rights of the target object. [in] AccessMode The processor request level mode. [in] UseResultList If set to TRUE, the function will return a list of granted access rights of each sub-object as well as status code for each. If this parameter is set to FALSE, then the function will just return only the granted access rights and status code for single object that's been target for access checks. [out] Privileges A pointer to a definite set of privileges that have been audited whilst doing access check procedures. Such set of privileges are optionally returned to the caller. This can be set to NULL if the caller doesn't want to obtain a set of privileges. [out] GrantedAccessList A list of granted access rights returned to the caller. This list can comprehend multiple elements which represent the sub-objects that have been checked or a single element which is the target object itself. [out] AccessStatusList A list of access status codes returned to the caller. This list can comprehend multiple elements which represent the sub-objects that have been checked or a single element which is the target object itself.
- Returns
- Returns TRUE if access onto the specific object is allowed, FALSE otherwise.
Definition at line 942 of file accesschk.c.
Referenced by SeAccessCheck(), and SepAccessCheck().
◆ SepAllowAccessObjectTypeList()
|
static |
Allows access of a target object in the object type list. This access is allowed for the whole hierarchy in the list.
- Parameters
-
[in,out] ObjectTypeList A pointer to an object type list where access is to be allowed for the target object. This operation applies for the entire hierarchy of the object type list. [in] ObjectTypeListLength The length of the object type list. This length represents the number of object elements in the list. [in] AccessMask The access mask right that is to be allowed for the object. [in] RemoveRemainingRights If set to TRUE, the function will remove the remaining rights of a target object. It will also grant access of the said object. Otherwise if set to FALSE, the function will only grant access. [in] ObjectTypeGuid A pointer to a object type GUID, that identifies the object. This GUID is used to search for the target object in the list. If this parameter is set to NULL, the function will allow access to the object itself in the list (aka the root).
Definition at line 324 of file accesschk.c.
Referenced by SepAnalyzeAcesFromDacl().
◆ SepAllowAccessObjectTypeResultList()
|
static |
Allows access of a target object and the children objects in an object type list.
- Parameters
-
[in,out] ObjectTypeList A pointer to an object type list where access is to be allowed for the target object and its children in the hierarchy list. [in] ObjectTypeListLength The length of the object type list. This length represents the number of object elements in the list. [in] AccessMask The access mask right that is to be allowed for the object. [in] ObjectTypeGuid A pointer to a object type GUID, that identifies the object. This GUID is used to search for the target object in the list. If this parameter is set to NULL, the function will allow access starting from the object itself in the list (aka the root).
Definition at line 135 of file accesschk.c.
Referenced by SepAnalyzeAcesFromDacl().
◆ SepAnalyzeAcesFromDacl()
|
static |
Analyzes an access control entry that is present in a discretionary access control list (DACL) for access right masks of each entry with the purpose to judge whether the calling thread can be warranted access check to a certain object or not.
- Parameters
-
[in] ActionType The type of analysis to be done against an access entry. This type influences how access rights are gathered. This can either be AccessCheckMaximum which means the algorithm will perform analysis against ACEs on behalf of the requestor that gave us the acknowledgement that he desires MAXIMUM_ALLOWED access right or AccessCheckRegular if the requestor wants a subset of access rights. [in] RemainingAccess The remaining access rights that have yet to be granted to the calling thread whomst requests access to a certain object. This parameter mustn't be 0 as the remaining rights are left to be addressed. This is the case if we have to address the remaining rights on a regular subset basis (the requestor didn't ask for MAXIMUM_ALLOWED). Otherwise this parameter can be 0. [in] Dacl The discretionary access control list to be given to this function. This DACL must have at least one ACE currently present in the list. [in] AccessToken A pointer to an access token, where an equality comparison check is performed if the security identifier (SID) from a ACE of a certain object is present in this token. This token represents the effective (calling thread) token of the caller. [in] PrimaryAccessToken A pointer to an access token, represented as an access token associated with the primary calling process. This token describes the primary security context of the main process. [in] IsTokenRestricted If this parameter is set to TRUE, the function considers the token pointed by AccessToken parameter argument as restricted. That is, the token has restricted SIDs therefore the function will act accordingly against that token by checking for restricted SIDs only when doing an equaility comparison check between the two identifiers. [in] PrincipalSelfSid A pointer to a security identifier that represents a principal. A principal identifies a user object which is associated with its own security descriptor. [in] GenericMapping A pointer to a generic mapping that is associated with the object in question being checked for access. If certain set of desired access rights have a generic access right, this parameter is needed to map generic rights. [in] ObjectTypeList A pointer to a list array of object types. If such array is provided to the function, the algorithm will perform a different approach by doing analysis against ACEs each sub-object of an object of primary level (level 0) or sub-objects of a sub-object of an object. If this parameter is NULL, the function will normally analyze the ACEs of a DACL of the target object itself. [in] ObjectTypeListLength The length of the object type list array, pointed by ObjectTypeList. This length in question represents the number of elements in such array. This parameter must be 0 if no array list is provided. [in] UseResultList This parameter is to used to determine how to perform an object type access check. If set to TRUE, the function will either grant or deny access to the object and sub-objects in the hierarchy list. If set to FALSE, the function will either grant or deny access to the target that will affect the entire hierarchy of the list. This parameter is used if the access action type is AccessCheckMaximum. [in,out] AccessCheckRights A pointer to a structure that contains the access check rights. This function fills up this structure with remaining, granted and denied rights to the caller for access check. Henceforth, this parameter must not be NULL!
Definition at line 460 of file accesschk.c.
Referenced by SepAccessCheckWorker().
◆ SepDenyAccessObjectTypeList()
|
static |
Denies access of a target object in the object type list. This access is denied for the whole hierarchy in the list.
- Parameters
-
[in,out] ObjectTypeList A pointer to an object type list where access is to be denied for the target object. This operation applies for the entire hierarchy of the object type list. [in] ObjectTypeListLength The length of the object type list. This length represents the number of object elements in the list. [in] AccessMask The access mask right that is to be denied for the object. [in] ObjectTypeGuid A pointer to a object type GUID, that identifies the object. This GUID is used to search for the target object in the list. If this parameter is set to NULL, the function will deny access to the object itself in the list (aka the root). [out] BreakOnDeny A pointer returned boolean value to the caller. The function will return TRUE if the requested remaining right is denied by the ACE, otherwise it returns FALSE.
Definition at line 228 of file accesschk.c.
Referenced by SepAnalyzeAcesFromDacl().
◆ SepDenyAccessObjectTypeResultList()
|
static |
Denies access of a target object and the children objects in an object type list.
- Parameters
-
[in,out] ObjectTypeList A pointer to an object type list where access is to be denied for the target object and its children in the hierarchy list. [in] ObjectTypeListLength The length of the object type list. This length represents the number of object elements in the list. [in] AccessMask The access mask right that is to be denied for the object. [in] ObjectTypeGuid A pointer to a object type GUID, that identifies the object. This GUID is used to search for the target object in the list. If this parameter is set to NULL, the function will deny access starting from the object itself in the list (aka the root).
Definition at line 43 of file accesschk.c.
Referenced by SepAnalyzeAcesFromDacl().
◆ SepGetPrivilegeSetLength()
|
static |
Retrieves the length size of a set list of privileges structure.
- Parameters
-
[in] PrivilegeSet A valid set of privileges.
- Returns
- Returns the total length of a set of privileges.
Definition at line 1482 of file accesschk.c.
Referenced by SepAccessCheck().