#include <assert.h>#include <stdarg.h>#include "windef.h"#include "winbase.h"#include "ws2tcpip.h"#include "winhttp.h"#include "schannel.h"#include "winternl.h"#include "wine/debug.h"#include "winhttp_private.h"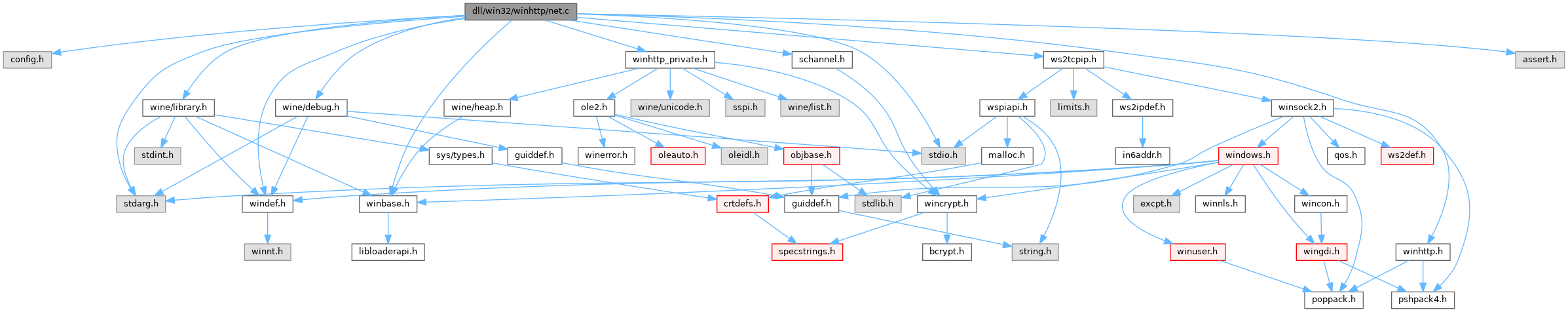
Go to the source code of this file.
Classes | |
| struct | async_resolve |
Variables | |
| static BOOL | winsock_loaded |
Function Documentation
◆ async_resolve_release()
|
static |
Definition at line 801 of file net.c.
Referenced by netconn_resolve(), and resolve_proc().
◆ create_async_resolve()
|
static |
Definition at line 780 of file net.c.
Referenced by netconn_resolve().
◆ netconn_addref()
◆ netconn_cancel_io()
Definition at line 674 of file net.c.
Referenced by socket_handle_closing().
◆ netconn_create()
| DWORD netconn_create | ( | struct hostdata * | host, |
| const struct sockaddr_storage * | sockaddr, | ||
| int | timeout, | ||
| struct netconn ** | ret_conn | ||
| ) |
Definition at line 212 of file net.c.
Referenced by open_connection().
◆ netconn_get_certificate()
Definition at line 850 of file net.c.
Referenced by open_connection().
◆ netconn_get_cipher_strength()
Definition at line 860 of file net.c.
Referenced by request_query_option().
◆ netconn_is_alive()
Definition at line 698 of file net.c.
Referenced by open_connection().
◆ netconn_query_data_available()
◆ netconn_recv()
Definition at line 618 of file net.c.
Referenced by read_more_data(), and receive_bytes().
◆ netconn_release()
Definition at line 295 of file net.c.
Referenced by close_connection(), connection_collector(), finished_reading(), handle_redirect(), open_connection(), and socket_destroy().
◆ netconn_resolve()
| DWORD netconn_resolve | ( | WCHAR * | hostname, |
| INTERNET_PORT | port, | ||
| struct sockaddr_storage * | addr, | ||
| int | timeout | ||
| ) |
Definition at line 819 of file net.c.
Referenced by open_connection().
◆ netconn_secure_connect()
| DWORD netconn_secure_connect | ( | struct netconn * | conn, |
| WCHAR * | hostname, | ||
| DWORD | security_flags, | ||
| CredHandle * | cred_handle, | ||
| BOOL | check_revocation | ||
| ) |
Definition at line 315 of file net.c.
Referenced by open_connection().
◆ netconn_send()
| DWORD netconn_send | ( | struct netconn * | conn, |
| const void * | msg, | ||
| size_t | len, | ||
| int * | sent, | ||
| WSAOVERLAPPED * | ovr | ||
| ) |
Definition at line 479 of file net.c.
Referenced by secure_proxy_connect(), send_bytes(), send_request(), and write_data().
◆ netconn_set_timeout()
Definition at line 686 of file net.c.
Referenced by open_connection(), receive_response(), send_request(), socket_set_option(), WinHttpSetTimeouts(), and WinHttpWebSocketCompleteUpgrade().
◆ netconn_unload()
◆ netconn_verify_cert()
|
static |
Definition at line 84 of file net.c.
Referenced by netconn_secure_connect().
◆ netconn_wait_overlapped_result()
| BOOL netconn_wait_overlapped_result | ( | struct netconn * | conn, |
| WSAOVERLAPPED * | ovr, | ||
| DWORD * | len | ||
| ) |
Definition at line 54 of file net.c.
Referenced by complete_send_frame().
◆ read_ssl_chunk()
|
static |
Definition at line 521 of file net.c.
Referenced by netconn_is_alive(), netconn_recv(), and tcp_recv().
◆ resolve_hostname()
|
static |
Definition at line 732 of file net.c.
Referenced by netconn_resolve(), and resolve_proc().
◆ resolve_proc()
|
static |
Definition at line 810 of file net.c.
Referenced by netconn_resolve().
◆ send_ssl_chunk()
|
static |
Definition at line 452 of file net.c.
Referenced by netconn_send(), and tcp_send().
◆ set_blocking()
Definition at line 206 of file net.c.
Referenced by netconn_create(), and netconn_is_alive().
◆ sock_recv()
Definition at line 73 of file net.c.
Referenced by FTP_GetNextLine(), FTP_ReceiveRequestData(), FTP_RetrieveFileData(), FTPFILE_QueryDataAvailable(), FTPFILE_ReadFile(), netconn_is_alive(), netconn_recv(), netconn_secure_connect(), and read_ssl_chunk().
◆ sock_send()
Definition at line 35 of file net.c.
Referenced by FTP_SendCommandA(), FTP_SendData(), FtpCommandW(), FTPFILE_WriteFile(), netconn_secure_connect(), netconn_send(), and send_ssl_chunk().
◆ WINE_DEFAULT_DEBUG_CHANNEL()
| WINE_DEFAULT_DEBUG_CHANNEL | ( | winhttp | ) |
◆ winsock_init()
Definition at line 199 of file net.c.
Referenced by netconn_create().
◆ winsock_startup()
Definition at line 187 of file net.c.
Referenced by winsock_init().
Variable Documentation
◆ winsock_loaded
|
static |
Definition at line 180 of file net.c.
Referenced by netconn_unload(), and winsock_startup().