#include "ws2tcpip.h"#include <time.h>#include <stdarg.h>#include <stdlib.h>#include <string.h>#include <stdio.h>#include <assert.h>#include "windef.h"#include "winbase.h"#include "wininet.h"#include "winerror.h"#include "wine/debug.h"#include "internet.h"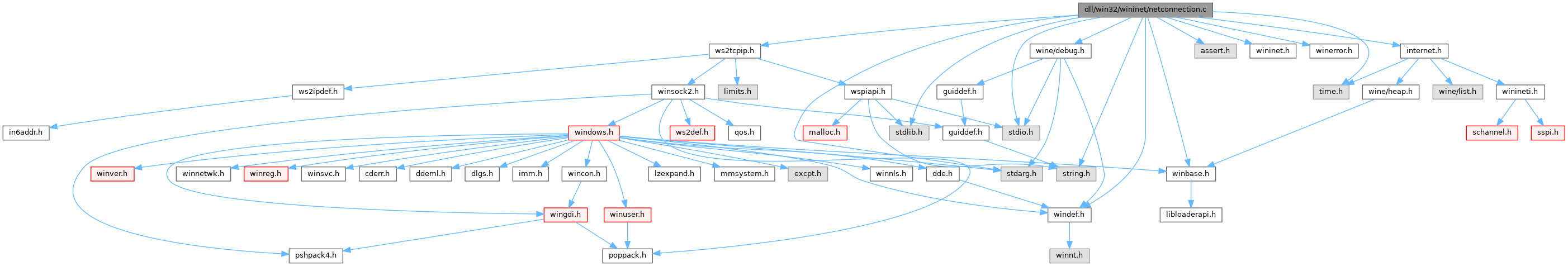
Go to the source code of this file.
Macros | |
| #define | NONAMELESSUNION |
Variables | |
| static SecHandle | cred_handle |
| static SecHandle | compat_cred_handle |
| static BOOL | cred_handle_initialized |
| static BOOL | have_compat_cred_handle |
| static CRITICAL_SECTION | init_sechandle_cs = { &init_sechandle_cs_debug, -1, 0, 0, 0, 0 } |
| static CRITICAL_SECTION_DEBUG | init_sechandle_cs_debug |
| static BOOL | winsock_loaded = FALSE |
Macro Definition Documentation
◆ NONAMELESSUNION
| #define NONAMELESSUNION |
Definition at line 28 of file netconnection.c.
Function Documentation
◆ close_netconn()
Definition at line 379 of file netconnection.c.
Referenced by free_netconn(), and http_release_netconn().
◆ create_netconn()
| DWORD create_netconn | ( | server_t * | server, |
| DWORD | security_flags, | ||
| BOOL | mask_errors, | ||
| DWORD | timeout, | ||
| netconn_t ** | ret | ||
| ) |
Definition at line 347 of file netconnection.c.
Referenced by open_http_connection().
◆ create_netconn_socket()
Definition at line 296 of file netconnection.c.
Referenced by create_netconn(), and NETCON_secure_connect().
◆ ensure_cred_handle()
Definition at line 231 of file netconnection.c.
Referenced by netcon_secure_connect_setup(), and open_connection().
◆ free_netconn()
Definition at line 385 of file netconnection.c.
Referenced by collect_connections(), and open_http_connection().
◆ init_winsock()
Definition at line 281 of file netconnection.c.
Referenced by create_netconn_socket(), FTP_Connect(), FTP_InitListenSocket(), InternetCheckConnectionW(), and InternetOpenW().
◆ is_valid_netconn()
Definition at line 374 of file netconnection.c.
Referenced by drain_content(), HTTP_GetResponseHeaders(), HTTP_HttpEndRequestW(), http_release_netconn(), HTTPREQ_QueryOption(), HTTPREQ_SetOption(), netconn_end_of_data(), netconn_read(), open_http_connection(), and WININET_InvalidCertificateDialog().
◆ NETCON_GetCert()
Definition at line 887 of file netconnection.c.
Referenced by get_security_cert_struct().
◆ NETCON_GetCipherStrength()
Definition at line 896 of file netconnection.c.
Referenced by get_security_cert_struct(), and netcon_secure_connect_setup().
◆ NETCON_is_alive()
Definition at line 876 of file netconnection.c.
Referenced by open_http_connection().
◆ NETCON_recv()
Definition at line 824 of file netconnection.c.
Referenced by chunked_read(), netconn_drain_content(), netconn_read(), and read_more_data().
◆ NETCON_secure_connect()
Definition at line 604 of file netconnection.c.
Referenced by HTTP_HttpSendRequestW().
◆ netcon_secure_connect_setup()
Definition at line 440 of file netconnection.c.
Referenced by NETCON_secure_connect().
◆ NETCON_send()
Definition at line 669 of file netconnection.c.
Referenced by HTTP_HttpSendRequestW(), and HTTPREQ_WriteFile().
◆ NETCON_set_timeout()
Definition at line 910 of file netconnection.c.
Referenced by HTTP_GetResponseHeaders(), and HTTP_HttpSendRequestW().
◆ NETCON_unload()
Definition at line 407 of file netconnection.c.
Referenced by DllMain().
◆ netconn_verify_cert()
|
static |
Definition at line 50 of file netconnection.c.
Referenced by netcon_secure_connect_setup().
◆ read_ssl_chunk()
|
static |
Definition at line 701 of file netconnection.c.
Referenced by NETCON_recv().
◆ send_ssl_chunk()
Definition at line 638 of file netconnection.c.
Referenced by NETCON_send().
◆ set_socket_blocking()
Definition at line 287 of file netconnection.c.
Referenced by create_netconn_socket(), NETCON_is_alive(), NETCON_recv(), netcon_secure_connect_setup(), NETCON_send(), and read_ssl_chunk().
◆ sock_recv()
Definition at line 429 of file netconnection.c.
Referenced by NETCON_is_alive(), NETCON_recv(), netcon_secure_connect_setup(), and read_ssl_chunk().
◆ sock_send()
Definition at line 418 of file netconnection.c.
Referenced by netcon_secure_connect_setup(), NETCON_send(), and send_ssl_chunk().
◆ WINE_DEFAULT_DEBUG_CHANNEL()
| WINE_DEFAULT_DEBUG_CHANNEL | ( | wininet | ) |
◆ winsock_startup()
Definition at line 268 of file netconnection.c.
Referenced by init_winsock().
Variable Documentation
◆ compat_cred_handle
|
static |
Definition at line 219 of file netconnection.c.
Referenced by ensure_cred_handle(), netcon_secure_connect_setup(), NETCON_unload(), and tcp_disconnect().
◆ cred_handle
|
static |
Definition at line 219 of file netconnection.c.
Referenced by ensure_cred_handle(), netcon_secure_connect_setup(), NETCON_unload(), netconn_secure_connect(), tcp_disconnect(), test_communication(), and test_InitializeSecurityContext().
◆ cred_handle_initialized
|
static |
Definition at line 220 of file netconnection.c.
Referenced by ensure_cred_handle(), NETCON_unload(), and tcp_disconnect().
◆ have_compat_cred_handle
|
static |
Definition at line 220 of file netconnection.c.
Referenced by ensure_cred_handle(), NETCON_secure_connect(), netcon_secure_connect_setup(), NETCON_unload(), and tcp_disconnect().
◆ init_sechandle_cs
|
static |
Definition at line 222 of file netconnection.c.
Referenced by ensure_cred_handle(), and NETCON_unload().
◆ init_sechandle_cs_debug
|
static |
Definition at line 223 of file netconnection.c.
◆ winsock_loaded
Definition at line 266 of file netconnection.c.
Referenced by NETCON_unload(), and winsock_startup().