#include "rpc_defs.h"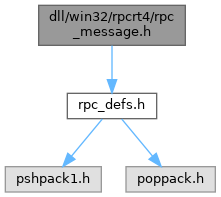
Go to the source code of this file.
Typedefs | |
| typedef unsigned int | NCA_STATUS |
Typedef Documentation
◆ NCA_STATUS
| typedef unsigned int NCA_STATUS |
Definition at line 26 of file rpc_message.h.
Function Documentation
◆ RPC2NCA_STATUS()
| NCA_STATUS RPC2NCA_STATUS | ( | RPC_STATUS | status | ) |
Definition at line 404 of file rpc_message.c.
Referenced by process_request_packet().
◆ RPCRT4_AuthorizeConnection()
| RPC_STATUS RPCRT4_AuthorizeConnection | ( | RpcConnection * | conn, |
| BYTE * | challenge, | ||
| ULONG | count | ||
| ) |
◆ RPCRT4_BuildBindAckHeader()
| RpcPktHdr * RPCRT4_BuildBindAckHeader | ( | ULONG | DataRepresentation, |
| unsigned short | MaxTransmissionSize, | ||
| unsigned short | MaxReceiveSize, | ||
| ULONG | AssocGroupId, | ||
| LPCSTR | ServerAddress, | ||
| unsigned char | ResultCount, | ||
| const RpcResult * | Results | ||
| ) |
Definition at line 254 of file rpc_message.c.
Referenced by process_bind_packet_no_send().
◆ RPCRT4_BuildBindHeader()
| RpcPktHdr * RPCRT4_BuildBindHeader | ( | ULONG | DataRepresentation, |
| unsigned short | MaxTransmissionSize, | ||
| unsigned short | MaxReceiveSize, | ||
| ULONG | AssocGroupId, | ||
| const RPC_SYNTAX_IDENTIFIER * | AbstractId, | ||
| const RPC_SYNTAX_IDENTIFIER * | TransferId | ||
| ) |
Definition at line 186 of file rpc_message.c.
Referenced by RpcAssoc_BindConnection().
◆ RPCRT4_BuildBindNackHeader()
| RpcPktHdr * RPCRT4_BuildBindNackHeader | ( | ULONG | DataRepresentation, |
| unsigned char | RpcVersion, | ||
| unsigned char | RpcVersionMinor, | ||
| unsigned short | RejectReason | ||
| ) |
Definition at line 229 of file rpc_message.c.
Referenced by handle_bind_error().
◆ RPCRT4_BuildFaultHeader()
| RpcPktHdr * RPCRT4_BuildFaultHeader | ( | ULONG | DataRepresentation, |
| RPC_STATUS | Status | ||
| ) |
Definition at line 170 of file rpc_message.c.
Referenced by process_request_packet().
◆ RPCRT4_BuildHttpConnectHeader()
| RpcPktHdr * RPCRT4_BuildHttpConnectHeader | ( | int | out_pipe, |
| const UUID * | connection_uuid, | ||
| const UUID * | pipe_uuid, | ||
| const UUID * | association_uuid | ||
| ) |
Definition at line 345 of file rpc_message.c.
Referenced by rpcrt4_http_prepare_in_pipe(), and rpcrt4_http_prepare_out_pipe().
◆ RPCRT4_BuildHttpFlowControlHeader()
| RpcPktHdr * RPCRT4_BuildHttpFlowControlHeader | ( | BOOL | server, |
| ULONG | bytes_transmitted, | ||
| ULONG | flow_control_increment, | ||
| const UUID * | pipe_uuid | ||
| ) |
Definition at line 385 of file rpc_message.c.
Referenced by rpcrt4_ncacn_http_receive_fragment().
◆ RPCRT4_BuildHttpHeader()
| RpcPktHdr * RPCRT4_BuildHttpHeader | ( | ULONG | DataRepresentation, |
| unsigned short | flags, | ||
| unsigned short | num_data_items, | ||
| unsigned int | payload_size | ||
| ) |
Definition at line 292 of file rpc_message.c.
Referenced by RPCRT4_BuildHttpConnectHeader(), RPCRT4_BuildHttpFlowControlHeader(), and rpcrt4_http_keep_connection_active_timer_proc().
◆ RPCRT4_BuildResponseHeader()
Definition at line 154 of file rpc_message.c.
Referenced by process_request_packet().
◆ RPCRT4_ClientConnectionAuth()
| RPC_STATUS RPCRT4_ClientConnectionAuth | ( | RpcConnection * | conn, |
| BYTE * | challenge, | ||
| ULONG | count | ||
| ) |
Definition at line 988 of file rpc_message.c.
Referenced by RpcAssoc_BindConnection().
◆ RPCRT4_default_authorize()
| RPC_STATUS RPCRT4_default_authorize | ( | RpcConnection * | conn, |
| BOOL | first_time, | ||
| unsigned char * | in_buffer, | ||
| unsigned int | in_size, | ||
| unsigned char * | out_buffer, | ||
| unsigned int * | out_size | ||
| ) |
Definition at line 868 of file rpc_message.c.
◆ RPCRT4_default_impersonate_client()
| RPC_STATUS RPCRT4_default_impersonate_client | ( | RpcConnection * | conn | ) |
Definition at line 1127 of file rpc_message.c.
Referenced by rpcrt4_conn_np_impersonate_client().
◆ RPCRT4_default_inquire_auth_client()
| RPC_STATUS RPCRT4_default_inquire_auth_client | ( | RpcConnection * | conn, |
| RPC_AUTHZ_HANDLE * | privs, | ||
| RPC_WSTR * | server_princ_name, | ||
| ULONG * | authn_level, | ||
| ULONG * | authn_svc, | ||
| ULONG * | authz_svc, | ||
| ULONG | flags | ||
| ) |
Definition at line 1185 of file rpc_message.c.
◆ RPCRT4_default_is_authorized()
| BOOL RPCRT4_default_is_authorized | ( | RpcConnection * | Connection | ) |
Definition at line 1118 of file rpc_message.c.
◆ RPCRT4_default_revert_to_self()
| RPC_STATUS RPCRT4_default_revert_to_self | ( | RpcConnection * | conn | ) |
Definition at line 1155 of file rpc_message.c.
Referenced by rpcrt4_conn_np_revert_to_self().
◆ RPCRT4_default_secure_packet()
| RPC_STATUS RPCRT4_default_secure_packet | ( | RpcConnection * | Connection, |
| enum secure_packet_direction | dir, | ||
| RpcPktHdr * | hdr, | ||
| unsigned int | hdr_size, | ||
| unsigned char * | stub_data, | ||
| unsigned int | stub_data_size, | ||
| RpcAuthVerifier * | auth_hdr, | ||
| unsigned char * | auth_value, | ||
| unsigned int | auth_value_size | ||
| ) |
Definition at line 678 of file rpc_message.c.
◆ RPCRT4_GetHeaderSize()
Definition at line 58 of file rpc_message.c.
Referenced by RPCRT4_default_receive_fragment(), rpcrt4_ncacn_http_receive_fragment(), RPCRT4_ReceiveWithAuth(), and RPCRT4_ValidateCommonHeader().
◆ RPCRT4_IsValidHttpPacket()
Definition at line 479 of file rpc_message.c.
Referenced by rpcrt4_http_read_http_packet(), and rpcrt4_ncacn_http_receive_fragment().
◆ RPCRT4_ParseHttpFlowControlHeader()
| RPC_STATUS RPCRT4_ParseHttpFlowControlHeader | ( | RpcPktHdr * | header, |
| unsigned char * | data, | ||
| BOOL | server, | ||
| ULONG * | bytes_transmitted, | ||
| ULONG * | flow_control_increment, | ||
| UUID * | pipe_uuid | ||
| ) |
Definition at line 633 of file rpc_message.c.
Referenced by rpcrt4_ncacn_http_receive_fragment().
◆ RPCRT4_ParseHttpPrepareHeader1()
| RPC_STATUS RPCRT4_ParseHttpPrepareHeader1 | ( | RpcPktHdr * | header, |
| unsigned char * | data, | ||
| ULONG * | field1 | ||
| ) |
Definition at line 562 of file rpc_message.c.
Referenced by rpcrt4_http_prepare_out_pipe().
◆ RPCRT4_ParseHttpPrepareHeader2()
| RPC_STATUS RPCRT4_ParseHttpPrepareHeader2 | ( | RpcPktHdr * | header, |
| unsigned char * | data, | ||
| ULONG * | field1, | ||
| ULONG * | bytes_until_next_packet, | ||
| ULONG * | field3 | ||
| ) |
Definition at line 587 of file rpc_message.c.
Referenced by rpcrt4_http_prepare_out_pipe().
◆ RPCRT4_ReceiveWithAuth()
| RPC_STATUS RPCRT4_ReceiveWithAuth | ( | RpcConnection * | Connection, |
| RpcPktHdr ** | Header, | ||
| PRPC_MESSAGE | pMsg, | ||
| unsigned char ** | auth_data_out, | ||
| ULONG * | auth_length_out | ||
| ) |
Definition at line 1372 of file rpc_message.c.
Referenced by RpcAssoc_BindConnection(), RPCRT4_io_thread(), and RPCRT4_Receive().
◆ RPCRT4_Send()
| RPC_STATUS RPCRT4_Send | ( | RpcConnection * | Connection, |
| RpcPktHdr * | Header, | ||
| void * | Buffer, | ||
| unsigned int | BufferLength | ||
| ) |
Definition at line 1219 of file rpc_message.c.
Referenced by I_RpcSend(), process_request_packet(), and RpcAssoc_BindConnection().
◆ RPCRT4_SendWithAuth()
| RPC_STATUS RPCRT4_SendWithAuth | ( | RpcConnection * | Connection, |
| RpcPktHdr * | Header, | ||
| void * | Buffer, | ||
| unsigned int | BufferLength, | ||
| const void * | Auth, | ||
| unsigned int | AuthLength | ||
| ) |
Definition at line 757 of file rpc_message.c.
Referenced by process_bind_packet(), RPCRT4_ClientConnectionAuth(), and RPCRT4_Send().
◆ RPCRT4_ServerConnectionAuth()
| RPC_STATUS RPCRT4_ServerConnectionAuth | ( | RpcConnection * | conn, |
| BOOL | start, | ||
| RpcAuthVerifier * | auth_data_in, | ||
| ULONG | auth_length_in, | ||
| unsigned char ** | auth_data_out, | ||
| ULONG * | auth_length_out | ||
| ) |
Definition at line 1021 of file rpc_message.c.
Referenced by process_auth3_packet(), and process_bind_packet_no_send().
◆ RPCRT4_ServerGetRegisteredAuthInfo()
| RPC_STATUS RPCRT4_ServerGetRegisteredAuthInfo | ( | USHORT | auth_type, |
| CredHandle * | cred, | ||
| TimeStamp * | exp, | ||
| ULONG * | max_token | ||
| ) |
Definition at line 1365 of file rpc_server.c.
Referenced by RPCRT4_ServerConnectionAuth().
◆ RPCRT4_ValidateCommonHeader()
| RPC_STATUS RPCRT4_ValidateCommonHeader | ( | const RpcPktCommonHdr * | hdr | ) |
Definition at line 1251 of file rpc_message.c.
Referenced by RPCRT4_default_receive_fragment(), and rpcrt4_ncacn_http_receive_fragment().