#include <stdarg.h>#include "windef.h"#include "winbase.h"#include "wincrypt.h"#include "winerror.h"#include "winreg.h"#include "wine/test.h"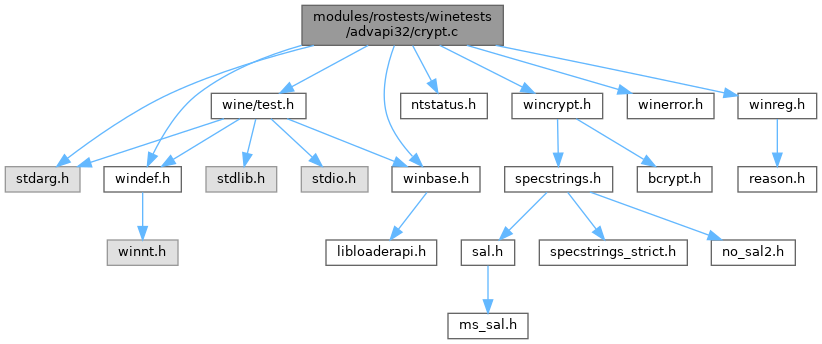
Go to the source code of this file.
Macros | |
| #define | NON_DEF_PROV_TYPE 999 |
| #define | key_length 16 |
Variables | |
| static const char | szRsaBaseProv [] = MS_DEF_PROV_A |
| static const char | szNonExistentProv [] = "Wine Nonexistent Cryptographic Provider v11.2" |
| static const char | szKeySet [] = "wine_test_keyset" |
| static const char | szBadKeySet [] = "wine_test_bad_keyset" |
| static DWORD | DWORD |
| static DWORD DWORD | LPSTR |
| static BYTE *static DWORD HCRYPTHASH *static | HCRYPTKEY |
| static | LPCWSTR |
| static | ULONG |
| static const BYTE | privKey [] |
| static const unsigned char | key [key_length] |
Macro Definition Documentation
◆ key_length
◆ NON_DEF_PROV_TYPE
Function Documentation
◆ BOOL()
◆ BOOLEAN()
◆ clean_up_environment()
Definition at line 95 of file crypt.c.
Referenced by START_TEST().
◆ FindDfltProvRegVals()
|
static |
Definition at line 857 of file crypt.c.
Referenced by test_get_default_provider().
◆ FindProvRegVals()
|
static |
Definition at line 582 of file crypt.c.
Referenced by test_enum_providers().
◆ FindProvTypesRegVals()
|
static |
Definition at line 704 of file crypt.c.
Referenced by test_enum_provider_types().
◆ init_environment()
Definition at line 64 of file crypt.c.
Referenced by START_TEST().
◆ init_function_pointers()
Definition at line 48 of file crypt.c.
Referenced by START_TEST().
◆ START_TEST()
| START_TEST | ( | crypt | ) |
Definition at line 1292 of file crypt.c.
◆ test_acquire_context()
Definition at line 183 of file crypt.c.
Referenced by START_TEST().
◆ test_container_sd()
Definition at line 1258 of file crypt.c.
Referenced by START_TEST().
◆ test_CryptReleaseContext()
Definition at line 128 of file crypt.c.
Referenced by START_TEST().
◆ test_enum_provider_types()
Definition at line 764 of file crypt.c.
Referenced by START_TEST().
◆ test_enum_providers()
Definition at line 611 of file crypt.c.
Referenced by START_TEST().
◆ test_get_default_provider()
Definition at line 907 of file crypt.c.
Referenced by START_TEST().
◆ test_incorrect_api_usage()
Definition at line 253 of file crypt.c.
Referenced by START_TEST().
◆ test_machine_guid()
Definition at line 1052 of file crypt.c.
Referenced by START_TEST().
◆ test_rc2_keylen()
Definition at line 1106 of file crypt.c.
Referenced by START_TEST().
◆ test_set_provider_ex()
Definition at line 989 of file crypt.c.
Referenced by START_TEST().
◆ test_SystemFunction036()
Definition at line 1229 of file crypt.c.
Referenced by START_TEST().
◆ test_verify_sig()
Definition at line 513 of file crypt.c.
Referenced by START_TEST().
Variable Documentation
◆ DWORD
◆ HCRYPTKEY
◆ key
|
static |
◆ LPCWSTR
◆ LPSTR
◆ privKey
Definition at line 487 of file crypt.c.
Referenced by test_verify_sig().
◆ szBadKeySet
Definition at line 34 of file crypt.c.
Referenced by clean_up_environment(), init_environment(), and test_incorrect_api_usage().
◆ szKeySet
Definition at line 33 of file crypt.c.
Referenced by clean_up_environment(), init_environment(), test_acquire_context(), test_CryptReleaseContext(), test_machine_guid(), and test_verify_sig().
◆ szNonExistentProv
Definition at line 32 of file crypt.c.
Referenced by test_acquire_context().
◆ szRsaBaseProv
|
static |
Definition at line 31 of file crypt.c.
Referenced by clean_up_environment(), init_environment(), test_acquire_context(), test_CryptReleaseContext(), and test_incorrect_api_usage().