#include <stdio.h>#include <stdarg.h>#include <windef.h>#include <winbase.h>#include <winerror.h>#include <wintrust.h>#include <softpub.h>#include <mssip.h>#include <winuser.h>#include "winnls.h"#include "wine/test.h"#include <pshpack1.h>#include <poppack.h>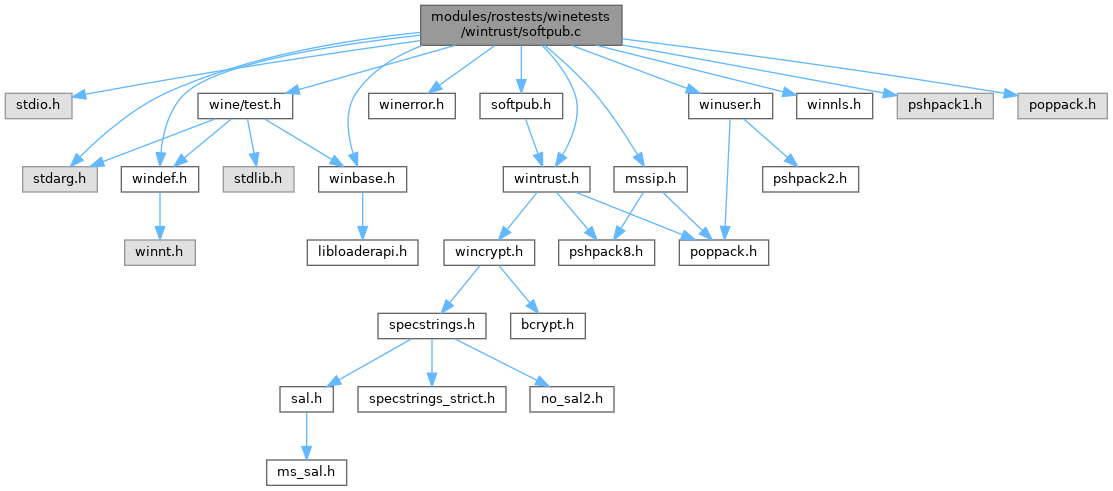
Go to the source code of this file.
Classes | |
| struct | _SAFE_PROVIDER_FUNCTIONS |
| struct | Imports |
| struct | Imports::__IMPORT_BY_NAME |
| struct | _PeImage |
Macros | |
| #define | WINTRUST_GET_PROC(func) |
| #define | CRYPT32_GET_PROC(func) |
| #define | VA_START 0x400000 |
| #define | FILE_PE_START 0x50 |
| #define | NUM_SECTIONS 3 |
| #define | FILE_TEXT 0x200 |
| #define | RVA_TEXT 0x1000 |
| #define | RVA_BSS 0x2000 |
| #define | FILE_IDATA 0x400 |
| #define | RVA_IDATA 0x3000 |
| #define | FILE_TOTAL 0x600 |
| #define | RVA_TOTAL 0x4000 |
| #define | EXIT_PROCESS (VA_START+RVA_IDATA+FIELD_OFFSET(struct Imports, thunks)) |
Functions | |
| static | BOOL (WINAPI *pWTHelperGetKnownUsages)(DWORD action |
| static DWORD SIP_INDIRECT_DATA *static | VOID (WINAPI *CertFreeCertificateChain_p)(PCCERT_CHAIN_CONTEXT) |
| static void | InitFunctionPtrs (void) |
| static void | test_utils (SAFE_PROVIDER_FUNCTIONS *funcs) |
| static void | testInitialize (SAFE_PROVIDER_FUNCTIONS *funcs, GUID *actionID) |
| static void | getNotepadPath (WCHAR *notepadPathW, DWORD size) |
| static HANDLE | create_temp_file (WCHAR *temp_file) |
| static void | testObjTrust (SAFE_PROVIDER_FUNCTIONS *funcs, GUID *actionID) |
| static void | testCertTrust (SAFE_PROVIDER_FUNCTIONS *funcs, GUID *actionID) |
| static void | test_provider_funcs (void) |
| static void | test_sip_create_indirect_data (void) |
| static void | test_wintrust (void) |
| static void | call_winverify (WCHAR *pathW, LONG *status, BOOL hash_only) |
| static void | test_wintrust_digest (void) |
| static void | test_get_known_usages (void) |
| static void | test_multiple_signatures (void) |
| static void | test_pe_image_hash (void) |
| START_TEST (softpub) | |
Variables | |
| static PCCRYPT_OID_INFO ** | usages |
| static const BYTE | v1CertWithPubKey [] |
| static const BYTE | selfSignedCert [] |
| static struct _PeImage | bin |
| static const BYTE | SelfSignedFile32 [] |
| static const BYTE | SelfSignedFile64 [] |
| static const BYTE | self_signed_3certs [] |
| static DWORD BYTE | DWORD |
Macro Definition Documentation
◆ CRYPT32_GET_PROC
◆ EXIT_PROCESS
◆ FILE_IDATA
◆ FILE_PE_START
◆ FILE_TEXT
◆ FILE_TOTAL
◆ NUM_SECTIONS
◆ RVA_BSS
◆ RVA_IDATA
◆ RVA_TEXT
◆ RVA_TOTAL
◆ VA_START
◆ WINTRUST_GET_PROC
Typedef Documentation
◆ SAFE_ADD_CERT
| typedef BOOL(WINAPI * SAFE_ADD_CERT) (CRYPT_PROVIDER_DATA *, DWORD, BOOL, DWORD, PCCERT_CONTEXT) |
◆ SAFE_ADD_PRIVDATA
| typedef BOOL(WINAPI * SAFE_ADD_PRIVDATA) (CRYPT_PROVIDER_DATA *, CRYPT_PROVIDER_PRIVDATA *) |
◆ SAFE_ADD_SGNR
| typedef BOOL(WINAPI * SAFE_ADD_SGNR) (CRYPT_PROVIDER_DATA *, BOOL, DWORD, struct _CRYPT_PROVIDER_SGNR *) |
◆ SAFE_ADD_STORE
| typedef BOOL(WINAPI * SAFE_ADD_STORE) (CRYPT_PROVIDER_DATA *, HCERTSTORE) |
◆ SAFE_MEM_ALLOC
◆ SAFE_MEM_FREE
◆ SAFE_PROVIDER_CERTCHKPOLICY_CALL
◆ SAFE_PROVIDER_CERTTRUST_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_CERTTRUST_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_CLEANUP_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_CLEANUP_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_FINALPOLICY_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_FINALPOLICY_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_FUNCTIONS
◆ SAFE_PROVIDER_INIT_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_INIT_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_OBJTRUST_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_OBJTRUST_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_SIGTRUST_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_SIGTRUST_CALL) (CRYPT_PROVIDER_DATA *) |
◆ SAFE_PROVIDER_TESTFINALPOLICY_CALL
| typedef HRESULT(WINAPI * SAFE_PROVIDER_TESTFINALPOLICY_CALL) (CRYPT_PROVIDER_DATA *) |
Function Documentation
◆ BOOL()
◆ call_winverify()
Definition at line 1596 of file softpub.c.
Referenced by test_wintrust_digest().
◆ create_temp_file()
Definition at line 286 of file softpub.c.
Referenced by test_bind_image_ex(), test_get_digest_stream(), test_image_load(), test_multiple_signatures(), test_pe_image_hash(), test_sip_create_indirect_data(), test_wintrust(), test_wintrust_digest(), and testObjTrust().
◆ getNotepadPath()
Definition at line 272 of file softpub.c.
Referenced by test_wintrust(), and testObjTrust().
◆ InitFunctionPtrs()
Definition at line 85 of file softpub.c.
Referenced by START_TEST().
◆ START_TEST()
| START_TEST | ( | softpub | ) |
Definition at line 1928 of file softpub.c.
◆ test_get_known_usages()
Definition at line 1721 of file softpub.c.
Referenced by START_TEST().
◆ test_multiple_signatures()
Definition at line 1785 of file softpub.c.
Referenced by START_TEST().
◆ test_pe_image_hash()
Definition at line 1897 of file softpub.c.
Referenced by START_TEST().
◆ test_provider_funcs()
Definition at line 629 of file softpub.c.
Referenced by START_TEST().
◆ test_sip_create_indirect_data()
Definition at line 740 of file softpub.c.
Referenced by START_TEST().
◆ test_utils()
|
static |
Definition at line 125 of file softpub.c.
Referenced by test_provider_funcs().
◆ test_wintrust()
Definition at line 827 of file softpub.c.
Referenced by START_TEST().
◆ test_wintrust_digest()
Definition at line 1618 of file softpub.c.
Referenced by START_TEST().
◆ testCertTrust()
|
static |
Definition at line 548 of file softpub.c.
Referenced by test_provider_funcs().
◆ testInitialize()
|
static |
Definition at line 229 of file softpub.c.
◆ testObjTrust()
|
static |
Definition at line 302 of file softpub.c.
Referenced by test_provider_funcs().
◆ VOID()
|
static |
Variable Documentation
◆ bin
◆ DWORD
◆ self_signed_3certs
Definition at line 1141 of file softpub.c.
Referenced by test_multiple_signatures().
◆ selfSignedCert
Definition at line 434 of file softpub.c.
Referenced by testCertTrust().
◆ SelfSignedFile32
Definition at line 893 of file softpub.c.
Referenced by test_wintrust_digest().
◆ SelfSignedFile64
Definition at line 999 of file softpub.c.
Referenced by test_wintrust_digest().
◆ usages
| PCCRYPT_OID_INFO** usages |
Definition at line 81 of file softpub.c.
Referenced by add_cert_to_list(), add_known_usages_to_list(), create_advanced_filter(), get_device(), initialize_purpose_selection(), test_get_known_usages(), WINTRUST_enumUsages(), and WTHelperGetKnownUsages().
◆ v1CertWithPubKey
Definition at line 112 of file softpub.c.
Referenced by test_utils(), and testObjTrust().