#include <windows.h>#include <stdlib.h>#include <ndk/ntndk.h>#include <ddk/ntddk.h>#include <stdio.h>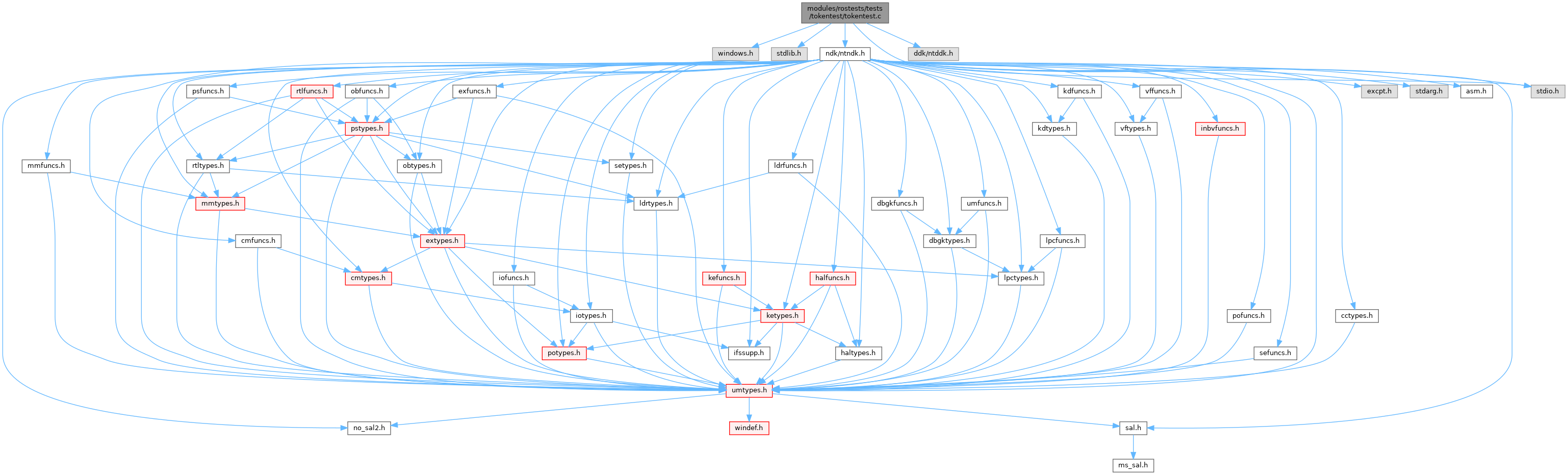
Go to the source code of this file.
Classes | |
| struct | _SID_2 |
Typedefs | |
| typedef struct _SID_2 | SID_2 |
Functions | |
| void | PrintSid (SID_AND_ATTRIBUTES *pSid, TOKEN_OWNER *pOwner, TOKEN_PRIMARY_GROUP *pPrimary) |
| void | DisplayTokenSids (TOKEN_USER *pUser, TOKEN_GROUPS *pGroups, TOKEN_OWNER *pOwner, TOKEN_PRIMARY_GROUP *pPrimary) |
| void | DisplayTokenPrivileges (TOKEN_PRIVILEGES *pPriv) |
| void | DisplayDacl (PACL pAcl) |
| PVOID | GetFromToken (HANDLE hToken, TOKEN_INFORMATION_CLASS tic) |
| void | DisplayToken (HANDLE hTokenSource) |
| BOOL | EnablePrivilege (LPWSTR wszName) |
| NTSTATUS | CreateInitialSystemToken (HANDLE *phSystemToken) |
| int | main (int argc, char *argv[]) |
Variables | |
| LUID_AND_ATTRIBUTES | InitialPrivilegeSet [] |
Macro Definition Documentation
◆ _UNICODE
| #define _UNICODE |
Definition at line 2 of file tokentest.c.
◆ ANONYMOUSUNIONS
| #define ANONYMOUSUNIONS |
Definition at line 4 of file tokentest.c.
◆ INCLUDE_THE_DDK_HEADERS
| #define INCLUDE_THE_DDK_HEADERS |
Definition at line 12 of file tokentest.c.
◆ INITIAL_PRIV_DISABLED
| #define INITIAL_PRIV_DISABLED 0 |
Definition at line 118 of file tokentest.c.
◆ INITIAL_PRIV_ENABLED
| #define INITIAL_PRIV_ENABLED SE_PRIVILEGE_ENABLED_BY_DEFAULT|SE_PRIVILEGE_ENABLED |
Definition at line 117 of file tokentest.c.
◆ NTOS_MODE_USER
| #define NTOS_MODE_USER |
Definition at line 8 of file tokentest.c.
◆ ROS_ACE
Definition at line 16 of file tokentest.c.
◆ ROS_ACE_HEADER
| #define ROS_ACE_HEADER ACE_HEADER |
Definition at line 15 of file tokentest.c.
◆ UNICODE
Definition at line 1 of file tokentest.c.
Typedef Documentation
◆ SID_2
Function Documentation
◆ CreateInitialSystemToken()
Definition at line 342 of file tokentest.c.
Referenced by main().
◆ DisplayDacl()
Definition at line 231 of file tokentest.c.
Referenced by CreateInitialSystemToken(), and DisplayToken().
◆ DisplayToken()
Definition at line 300 of file tokentest.c.
Referenced by main().
◆ DisplayTokenPrivileges()
| void DisplayTokenPrivileges | ( | TOKEN_PRIVILEGES * | pPriv | ) |
Definition at line 205 of file tokentest.c.
◆ DisplayTokenSids()
| void DisplayTokenSids | ( | TOKEN_USER * | pUser, |
| TOKEN_GROUPS * | pGroups, | ||
| TOKEN_OWNER * | pOwner, | ||
| TOKEN_PRIMARY_GROUP * | pPrimary | ||
| ) |
Definition at line 189 of file tokentest.c.
Referenced by CreateInitialSystemToken(), and DisplayToken().
◆ EnablePrivilege()
Definition at line 323 of file tokentest.c.
Referenced by main().
◆ GetFromToken()
| PVOID GetFromToken | ( | HANDLE | hToken, |
| TOKEN_INFORMATION_CLASS | tic | ||
| ) |
Definition at line 277 of file tokentest.c.
Referenced by DisplayToken().
◆ main()
hosttype.c Copyright (C) 2002 by Brian Palmer brian.nosp@m.p@sg.nosp@m.inet..nosp@m.com
Definition at line 482 of file tokentest.c.
◆ PrintSid()
| void PrintSid | ( | SID_AND_ATTRIBUTES * | pSid, |
| TOKEN_OWNER * | pOwner, | ||
| TOKEN_PRIMARY_GROUP * | pPrimary | ||
| ) |
Definition at line 155 of file tokentest.c.
Referenced by DisplayTokenSids().
Variable Documentation
◆ InitialPrivilegeSet
| LUID_AND_ATTRIBUTES InitialPrivilegeSet[] |
Definition at line 119 of file tokentest.c.
Referenced by CreateInitialSystemToken().