#include <ntoskrnl.h>#include <debug.h>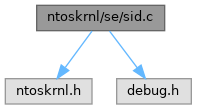
Go to the source code of this file.
Classes | |
| struct | _SID_VALIDATE |
Macros | |
| #define | NDEBUG |
| #define | SE_MAXIMUM_GROUP_LIMIT 0x1000 |
Typedefs | |
| typedef struct _SID_VALIDATE | SID_VALIDATE |
| typedef struct _SID_VALIDATE * | PSID_VALIDATE |
Functions | |
| VOID NTAPI | FreeInitializedSids (VOID) |
| Frees all the known initialized SIDs in the system from the memory. | |
| BOOLEAN NTAPI | SepInitSecurityIDs (VOID) |
| Initializes all the SIDs known in the system. | |
| NTSTATUS NTAPI | SepCaptureSid (_In_ PSID InputSid, _In_ KPROCESSOR_MODE AccessMode, _In_ POOL_TYPE PoolType, _In_ BOOLEAN CaptureIfKernel, _Out_ PSID *CapturedSid) |
| Captures a SID. | |
| VOID NTAPI | SepReleaseSid (_In_ PSID CapturedSid, _In_ KPROCESSOR_MODE AccessMode, _In_ BOOLEAN CaptureIfKernel) |
| Releases a captured SID. | |
| BOOLEAN NTAPI | SepSidInTokenEx (_In_ PACCESS_TOKEN _Token, _In_ PSID PrincipalSelfSid, _In_ PSID _Sid, _In_ BOOLEAN Deny, _In_ BOOLEAN Restricted) |
| Checks if a SID is present in a token. | |
| BOOLEAN NTAPI | SepSidInToken (_In_ PACCESS_TOKEN _Token, _In_ PSID Sid) |
| Checks if a SID is present in a token. | |
| PSID NTAPI | SepGetSidFromAce (_In_ PACE Ace) |
| Captures a security identifier from a given access control entry. This identifier is valid for the whole of its lifetime. | |
| NTSTATUS NTAPI | SeCaptureSidAndAttributesArray (_In_ PSID_AND_ATTRIBUTES SrcSidAndAttributes, _In_ ULONG AttributeCount, _In_ KPROCESSOR_MODE PreviousMode, _In_opt_ PVOID AllocatedMem, _In_ ULONG AllocatedLength, _In_ POOL_TYPE PoolType, _In_ BOOLEAN CaptureIfKernel, _Out_ PSID_AND_ATTRIBUTES *CapturedSidAndAttributes, _Out_ PULONG ResultLength) |
| Captures a SID with attributes. | |
| VOID NTAPI | SeReleaseSidAndAttributesArray (_In_ _Post_invalid_ PSID_AND_ATTRIBUTES CapturedSidAndAttributes, _In_ KPROCESSOR_MODE AccessMode, _In_ BOOLEAN CaptureIfKernel) |
| Releases a captured SID with attributes. | |
Macro Definition Documentation
◆ NDEBUG
◆ SE_MAXIMUM_GROUP_LIMIT
Typedef Documentation
◆ PSID_VALIDATE
| typedef struct _SID_VALIDATE * PSID_VALIDATE |
◆ SID_VALIDATE
| typedef struct _SID_VALIDATE SID_VALIDATE |
Function Documentation
◆ FreeInitializedSids()
Frees all the known initialized SIDs in the system from the memory.
- Returns
- Nothing.
Definition at line 72 of file sid.c.
Referenced by SepInitSecurityIDs().
◆ SeCaptureSidAndAttributesArray()
| NTSTATUS NTAPI SeCaptureSidAndAttributesArray | ( | _In_ PSID_AND_ATTRIBUTES | SrcSidAndAttributes, |
| _In_ ULONG | AttributeCount, | ||
| _In_ KPROCESSOR_MODE | PreviousMode, | ||
| _In_opt_ PVOID | AllocatedMem, | ||
| _In_ ULONG | AllocatedLength, | ||
| _In_ POOL_TYPE | PoolType, | ||
| _In_ BOOLEAN | CaptureIfKernel, | ||
| _Out_ PSID_AND_ATTRIBUTES * | CapturedSidAndAttributes, | ||
| _Out_ PULONG | ResultLength | ||
| ) |
Captures a SID with attributes.
- Parameters
-
[in] SrcSidAndAttributes Source of the SID with attributes to be captured. [in] AttributeCount The number count of attributes, in total. [in] PreviousMode Processor access level mode. [in] AllocatedMem The allocated memory buffer for the captured SID. If the caller supplies no allocated block of memory then the function will allocate some buffer block of memory for the captured SID automatically. [in] AllocatedLength The length of the buffer that points to the allocated memory, in bytes. [in] PoolType The pool type for the captured SID and attributes to assign. [in] CaptureIfKernel If set to TRUE, the capturing is done within the kernel. Otherwise the capturing is done in a kernel mode driver. [out] CapturedSidAndAttributes The captured SID and attributes. [out] ResultLength The length of the captured SID and attributes, in bytes.
- Returns
- Returns STATUS_SUCCESS if SID and attributes capturing has been completed successfully. STATUS_INVALID_PARAMETER is returned if the count of attributes exceeds the maximum threshold that the kernel can permit, with the purpose of avoiding integer overflows. STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation for the captured SID has failed. STATUS_BUFFER_TOO_SMALL is returned if the length of the allocated buffer is less than the required size. STATUS_INVALID_SID is returned if a SID doesn't meet certain requirements to be considered a valid SID by the security manager. A failure NTSTATUS code is returned otherwise.
- Remarks
- A security identifier (SID) is a variable-length data structure that can change in size over time, depending on the factors that influence this effect in question. An attacker can take advantage of this fact and can potentially modify certain properties of a SID making it different in size than it was originally before. This is what we'd call, a TOCTOU vulnerability.
For this reason, the logic of copying the SIDs and their attributes into a new buffer goes like this: first, allocate a buffer array that just holds the lengths and subauthority count of each SID. Such information is copied in the first loop. Then in a second loop, iterate over the array with SID provided and copy them into the final array. The moment we're doing this, validate the lengths of each SID basing upon the captured lengths we've got before. In this way we ensure that the SIDs have remained intact. The validation checks are done in user mode as a general rule that we just cannot trust UM and whatever data is coming from it.
Definition at line 693 of file sid.c.
Referenced by NtAdjustGroupsToken(), NtCreateToken(), and NtFilterToken().
◆ SepCaptureSid()
| NTSTATUS NTAPI SepCaptureSid | ( | _In_ PSID | InputSid, |
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _In_ POOL_TYPE | PoolType, | ||
| _In_ BOOLEAN | CaptureIfKernel, | ||
| _Out_ PSID * | CapturedSid | ||
| ) |
Captures a SID.
- Parameters
-
[in] InputSid A valid security identifier to be captured. [in] AccessMode Processor level access mode. [in] PoolType Pool memory type for the captured SID to assign upon allocation. [in] CaptureIfKernel If set to TRUE, the capturing is done within the kernel. Otherwise the capturing is done in a kernel mode driver. [out] CapturedSid The captured security identifier, returned to the caller.
- Returns
- Returns STATUS_SUCCESS if the SID was captured. STATUS_INSUFFICIENT_RESOURCES is returned if memory pool allocation for the captured SID has failed.
Definition at line 314 of file sid.c.
Referenced by NtCreateToken(), NtSecureConnectPort(), NtSetInformationToken(), SepAccessCheck(), and SepAccessCheckAndAuditAlarm().
◆ SepGetSidFromAce()
Captures a security identifier from a given access control entry. This identifier is valid for the whole of its lifetime.
- Parameters
-
[in] Ace A pointer to an access control entry, which can be obtained from a DACL.
- Returns
- Returns a pointer to a security identifier (SID), otherwise NULL is returned if an unsupported ACE type was given to the function.
Definition at line 572 of file sid.c.
Referenced by SepAnalyzeAcesFromDacl().
◆ SepInitSecurityIDs()
Initializes all the SIDs known in the system.
- Returns
- Returns TRUE if all the SIDs have been initialized, FALSE otherwise.
Definition at line 115 of file sid.c.
Referenced by SepInitializationPhase0().
◆ SepReleaseSid()
| VOID NTAPI SepReleaseSid | ( | _In_ PSID | CapturedSid, |
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _In_ BOOLEAN | CaptureIfKernel | ||
| ) |
Releases a captured SID.
- Parameters
-
[in] CapturedSid The captured SID to be released. [in] AccessMode Processor level access mode. [in] CaptureIfKernel If set to TRUE, the releasing is done within the kernel. Otherwise the releasing is done in a kernel mode driver.
- Returns
- Nothing.
Definition at line 400 of file sid.c.
Referenced by NtCreateToken(), NtSecureConnectPort(), NtSetInformationToken(), SepAccessCheck(), and SepAccessCheckAndAuditAlarm().
◆ SepSidInToken()
Checks if a SID is present in a token.
- Returns
- Returns TRUE if the specified SID in the call is present in the token, FALSE otherwise.
Definition at line 547 of file sid.c.
Referenced by SepTokenIsOwner().
◆ SepSidInTokenEx()
| BOOLEAN NTAPI SepSidInTokenEx | ( | _In_ PACCESS_TOKEN | _Token, |
| _In_ PSID | PrincipalSelfSid, | ||
| _In_ PSID | _Sid, | ||
| _In_ BOOLEAN | Deny, | ||
| _In_ BOOLEAN | Restricted | ||
| ) |
Checks if a SID is present in a token.
- Parameters
-
[in] _Token A valid token object. [in] PrincipalSelfSid A principal self SID. [in] _Sid A regular SID. [in] Deny If set to TRUE, the caller expected that a SID in a token must be a deny-only SID, that is, access checks are performed only for deny-only ACEs of the said SID. [in] Restricted If set to TRUE, the caller expects that a SID in a token is restricted (by the general definition, a token is restricted).
- Returns
- Returns TRUE if the specified SID in the call is present in the token, FALSE otherwise.
Definition at line 443 of file sid.c.
Referenced by SepAnalyzeAcesFromDacl(), SepSidInToken(), and SepTokenIsOwner().
◆ SeReleaseSidAndAttributesArray()
| VOID NTAPI SeReleaseSidAndAttributesArray | ( | _In_ _Post_invalid_ PSID_AND_ATTRIBUTES | CapturedSidAndAttributes, |
| _In_ KPROCESSOR_MODE | AccessMode, | ||
| _In_ BOOLEAN | CaptureIfKernel | ||
| ) |
Releases a captured SID with attributes.
- Parameters
-
[in] CapturedSidAndAttributes The captured SID with attributes to be released. [in] AccessMode Processor access level mode. [in] CaptureIfKernel If set to TRUE, the releasing is done within the kernel. Otherwise the releasing is done in a kernel mode driver.
- Returns
- Nothing.
Definition at line 976 of file sid.c.
Referenced by NtAdjustGroupsToken(), NtCreateToken(), and NtFilterToken().
Variable Documentation
◆ SeAliasAccountOpsSid
Definition at line 45 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasAdminsSid
Definition at line 41 of file sid.c.
Referenced by FreeInitializedSids(), IopCreateDefaultDeviceSecurityDescriptor(), MiCreateMemoryEvent(), NtCreatePagingFile(), ObpCreateKernelObjectsSD(), ObpGetDosDevicesProtection(), SepCreateImpersonationTokenDacl(), SepCreateSystemProcessToken(), SepCreateToken(), SepDuplicateToken(), SepInitDACLs(), SepInitExports(), SepInitializationPhase1(), SepInitSecurityIDs(), and SepPerformTokenFiltering().
◆ SeAliasBackupOpsSid
Definition at line 48 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasGuestsSid
Definition at line 43 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasPowerUsersSid
Definition at line 44 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasPrintOpsSid
Definition at line 47 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasSystemOpsSid
Definition at line 46 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAliasUsersSid
Definition at line 42 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAnonymousLogonSid
Definition at line 51 of file sid.c.
Referenced by FreeInitializedSids(), SepCreateSystemAnonymousLogonToken(), SepCreateSystemAnonymousLogonTokenNoEveryone(), SepInitDACLs(), SepInitExports(), and SepInitSecurityIDs().
◆ SeAuthenticatedUserSid
Definition at line 39 of file sid.c.
Referenced by FreeInitializedSids(), and SepInitSecurityIDs().
◆ SeAuthenticatedUsersSid
Definition at line 49 of file sid.c.
Referenced by FreeInitializedSids(), SepCreateSystemProcessToken(), SepInitExports(), and SepInitSecurityIDs().
◆ SeBatchSid
Definition at line 34 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeCreatorGroupServerSid
Definition at line 30 of file sid.c.
Referenced by FreeInitializedSids(), and SepInitSecurityIDs().
◆ SeCreatorGroupSid
Definition at line 28 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), SepInitSecurityIDs(), and SepPropagateAcl().
◆ SeCreatorOwnerServerSid
Definition at line 29 of file sid.c.
Referenced by FreeInitializedSids(), and SepInitSecurityIDs().
◆ SeCreatorOwnerSid
Definition at line 27 of file sid.c.
Referenced by FreeInitializedSids(), ObpGetDosDevicesProtection(), SepInitExports(), SepInitSecurityIDs(), and SepPropagateAcl().
◆ SeCreatorSidAuthority
| SID_IDENTIFIER_AUTHORITY SeCreatorSidAuthority = {SECURITY_CREATOR_SID_AUTHORITY} |
Definition at line 21 of file sid.c.
Referenced by SepInitSecurityIDs().
◆ SeDialupSid
Definition at line 32 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeInteractiveSid
Definition at line 35 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeLocalServiceSid
Definition at line 52 of file sid.c.
Referenced by SepInitExports(), and SepInitSecurityIDs().
◆ SeLocalSid
Definition at line 26 of file sid.c.
Referenced by FreeInitializedSids(), SepCreateSystemProcessToken(), SepInitExports(), and SepInitSecurityIDs().
◆ SeLocalSidAuthority
| SID_IDENTIFIER_AUTHORITY SeLocalSidAuthority = {SECURITY_LOCAL_SID_AUTHORITY} |
Definition at line 20 of file sid.c.
Referenced by SepInitSecurityIDs().
◆ SeLocalSystemSid
Definition at line 38 of file sid.c.
Referenced by FreeInitializedSids(), MiCreateMemoryEvent(), NtCreatePagingFile(), ObpCreateKernelObjectsSD(), ObpGetDosDevicesProtection(), SepCreateImpersonationTokenDacl(), SepCreateSystemProcessToken(), SepInitDACLs(), SepInitExports(), SepInitializationPhase1(), SepInitSecurityIDs(), and SePrivilegedServiceAuditAlarm().
◆ SeNetworkServiceSid
Definition at line 53 of file sid.c.
Referenced by SepInitExports(), and SepInitSecurityIDs().
◆ SeNetworkSid
Definition at line 33 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeNtAuthoritySid
Definition at line 31 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeNtSidAuthority
| SID_IDENTIFIER_AUTHORITY SeNtSidAuthority = {SECURITY_NT_AUTHORITY} |
Definition at line 22 of file sid.c.
Referenced by SepInitSecurityIDs().
◆ SeNullSid
Definition at line 24 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeNullSidAuthority
| SID_IDENTIFIER_AUTHORITY SeNullSidAuthority = {SECURITY_NULL_SID_AUTHORITY} |
Definition at line 18 of file sid.c.
Referenced by SepInitSecurityIDs().
◆ SePrincipalSelfSid
Definition at line 37 of file sid.c.
Referenced by FreeInitializedSids(), SepInitSecurityIDs(), and SepSidInTokenEx().
◆ SeRestrictedCodeSid
Definition at line 40 of file sid.c.
Referenced by FreeInitializedSids(), SepCreateImpersonationTokenDacl(), SepInitDACLs(), and SepInitSecurityIDs().
◆ SeRestrictedSid
Definition at line 50 of file sid.c.
Referenced by FreeInitializedSids(), SepInitExports(), and SepInitSecurityIDs().
◆ SeServiceSid
Definition at line 36 of file sid.c.
Referenced by FreeInitializedSids(), and SepInitSecurityIDs().
◆ SeWorldSid
Definition at line 25 of file sid.c.
Referenced by CmpQuerySecurityDescriptor(), FreeInitializedSids(), IopCreateDefaultDeviceSecurityDescriptor(), MiCreateMemoryEvent(), ObpCreateKernelObjectsSD(), ObpGetDosDevicesProtection(), SeFastTraverseCheck(), SepCreateSystemAnonymousLogonToken(), SepCreateSystemProcessToken(), SepInitDACLs(), SepInitExports(), SepInitializationPhase1(), SepInitSecurityIDs(), and SeSetWorldSecurityDescriptor().
◆ SeWorldSidAuthority
| SID_IDENTIFIER_AUTHORITY SeWorldSidAuthority = {SECURITY_WORLD_SID_AUTHORITY} |
Definition at line 19 of file sid.c.
Referenced by SepInitSecurityIDs().