#include <wintirpc.h>#include <stdio.h>#include <stdlib.h>#include <string.h>#include <rpc/rpc.h>#include <gssapi/gssapi.h>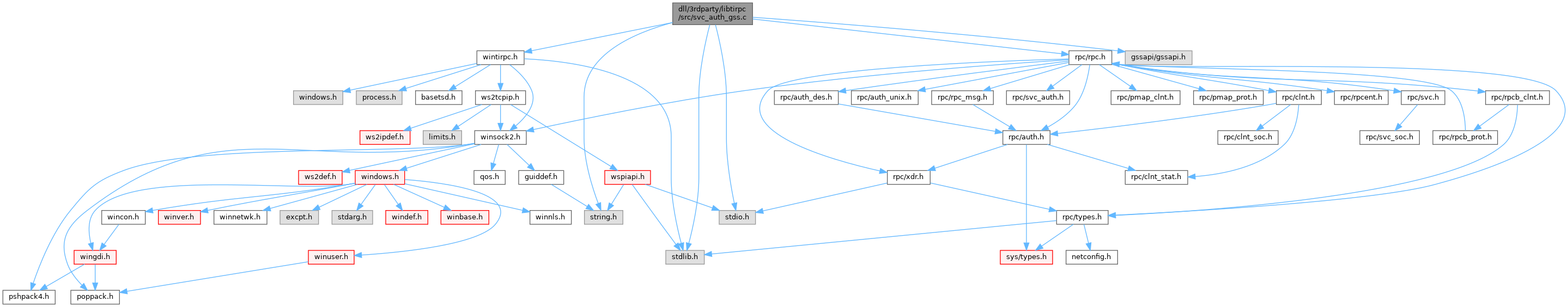
Go to the source code of this file.
Classes | |
| struct | gss_union_ctx_id_t |
| struct | svc_rpc_gss_data |
Macros | |
| #define | SVCAUTH_PRIVATE(auth) ((struct svc_rpc_gss_data *)(auth)->svc_ah_private) |
Typedefs | |
| typedef struct gss_union_ctx_id_t | gss_union_ctx_id_desc |
| typedef struct gss_union_ctx_id_t * | gss_union_ctx_id_t |
Functions | |
| static bool_t | svcauth_gss_destroy () |
| static bool_t | svcauth_gss_wrap () |
| static bool_t | svcauth_gss_unwrap () |
| bool_t | svcauth_gss_set_svc_name (gss_name_t name) |
| static bool_t | svcauth_gss_import_name (char *service) |
| static bool_t | svcauth_gss_acquire_cred (void) |
| static bool_t | svcauth_gss_release_cred (void) |
| static bool_t | svcauth_gss_accept_sec_context (struct svc_req *rqst, struct rpc_gss_init_res *gr) |
| static bool_t | svcauth_gss_validate (struct svc_rpc_gss_data *gd, struct rpc_msg *msg) |
| bool_t | svcauth_gss_nextverf (struct svc_req *rqst, u_int num) |
| enum auth_stat | _svcauth_gss (struct svc_req *rqst, struct rpc_msg *msg, bool_t *no_dispatch) |
| bool_t | svcauth_gss_destroy (SVCAUTH *auth) |
| bool_t | svcauth_gss_wrap (SVCAUTH *auth, XDR *xdrs, xdrproc_t xdr_func, caddr_t xdr_ptr) |
| bool_t | svcauth_gss_unwrap (SVCAUTH *auth, XDR *xdrs, xdrproc_t xdr_func, caddr_t xdr_ptr) |
| char * | svcauth_gss_get_principal (SVCAUTH *auth) |
Variables | |
| SVCAUTH | svc_auth_none |
| struct svc_auth_ops | svc_auth_gss_ops |
| gss_cred_id_t | _svcauth_gss_creds |
| static gss_name_t | _svcauth_gss_name = NULL |
Macro Definition Documentation
◆ SVCAUTH_PRIVATE
| #define SVCAUTH_PRIVATE | ( | auth | ) | ((struct svc_rpc_gss_data *)(auth)->svc_ah_private) |
Definition at line 78 of file svc_auth_gss.c.
Typedef Documentation
◆ gss_union_ctx_id_desc
◆ gss_union_ctx_id_t
| typedef struct gss_union_ctx_id_t * gss_union_ctx_id_t |
Function Documentation
◆ _svcauth_gss()
Definition at line 367 of file svc_auth_gss.c.
◆ svcauth_gss_accept_sec_context()
|
static |
Definition at line 175 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_acquire_cred()
Definition at line 138 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_destroy() [1/2]
|
static |
◆ svcauth_gss_destroy() [2/2]
Definition at line 517 of file svc_auth_gss.c.
◆ svcauth_gss_get_principal()
Definition at line 573 of file svc_auth_gss.c.
◆ svcauth_gss_import_name()
Definition at line 112 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_nextverf()
Definition at line 336 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_release_cred()
Definition at line 156 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_set_svc_name()
| bool_t svcauth_gss_set_svc_name | ( | gss_name_t | name | ) |
Definition at line 86 of file svc_auth_gss.c.
Referenced by svcauth_gss_import_name().
◆ svcauth_gss_unwrap() [1/2]
|
static |
◆ svcauth_gss_unwrap() [2/2]
Definition at line 556 of file svc_auth_gss.c.
◆ svcauth_gss_validate()
|
static |
Definition at line 284 of file svc_auth_gss.c.
Referenced by _svcauth_gss().
◆ svcauth_gss_wrap() [1/2]
|
static |
◆ svcauth_gss_wrap() [2/2]
Definition at line 539 of file svc_auth_gss.c.
Variable Documentation
◆ _svcauth_gss_creds
| gss_cred_id_t _svcauth_gss_creds |
Definition at line 82 of file svc_auth_gss.c.
Referenced by svcauth_gss_accept_sec_context(), svcauth_gss_acquire_cred(), and svcauth_gss_release_cred().
◆ _svcauth_gss_name
|
static |
Definition at line 83 of file svc_auth_gss.c.
Referenced by _svcauth_gss(), svcauth_gss_acquire_cred(), and svcauth_gss_set_svc_name().
◆ svc_auth_gss_ops
| struct svc_auth_ops svc_auth_gss_ops |
Definition at line 60 of file svc_auth_gss.c.
Referenced by _svcauth_gss(), and svc_getreq_common().
◆ svc_auth_none
|
extern |
Definition at line 63 of file svc_auth_none.c.
Referenced by _svcauth_gss(), and _svcauth_none().