#include "lsasrv.h"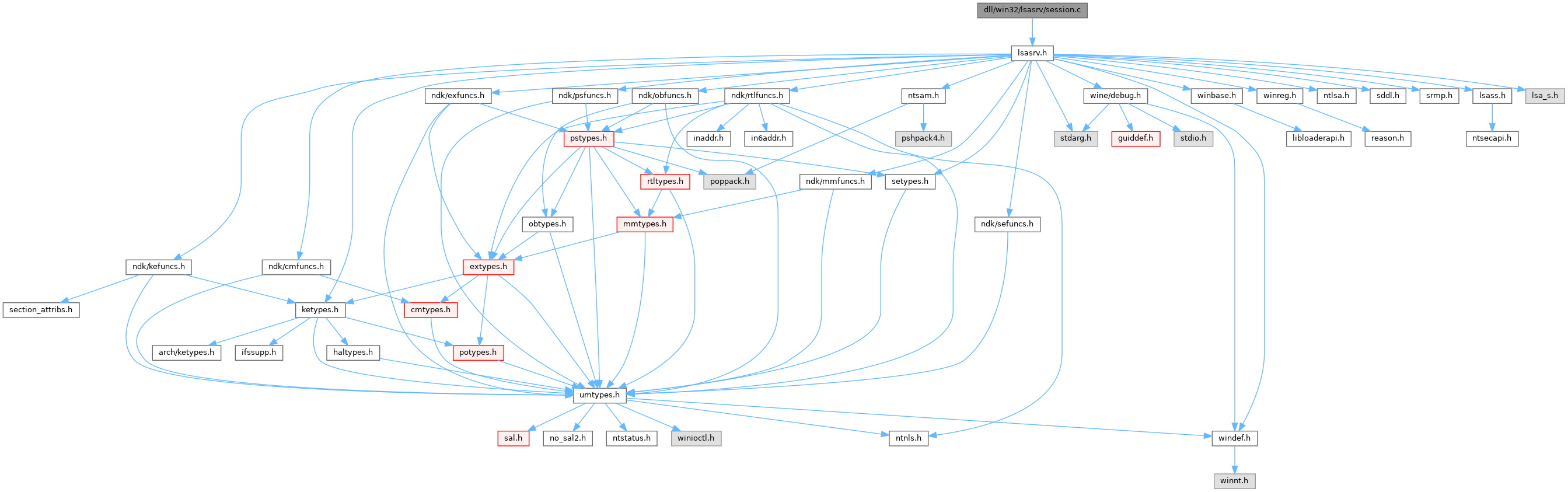
Go to the source code of this file.
Classes | |
| struct | _LSAP_LOGON_SESSION |
Typedefs | |
| typedef struct _LSAP_LOGON_SESSION | LSAP_LOGON_SESSION |
| typedef struct _LSAP_LOGON_SESSION * | PLSAP_LOGON_SESSION |
Variables | |
| LIST_ENTRY | SessionListHead |
| ULONG | SessionCount |
Typedef Documentation
◆ LSAP_LOGON_SESSION
◆ PLSAP_LOGON_SESSION
| typedef struct _LSAP_LOGON_SESSION * PLSAP_LOGON_SESSION |
Function Documentation
◆ LsapAddCredential()
| NTSTATUS NTAPI LsapAddCredential | ( | _In_ PLUID | LogonId, |
| _In_ ULONG | AuthenticationPackage, | ||
| _In_ PLSA_STRING | PrimaryKeyValue, | ||
| _In_ PLSA_STRING | Credential | ||
| ) |
◆ LsapCreateLogonSession()
Definition at line 159 of file session.c.
Referenced by LsapInitAuthPackages().
◆ LsapDeleteCredential()
| NTSTATUS NTAPI LsapDeleteCredential | ( | _In_ PLUID | LogonId, |
| _In_ ULONG | AuthenticationPackage, | ||
| _In_ PLSA_STRING | PrimaryKeyValue | ||
| ) |
Definition at line 288 of file session.c.
Referenced by LsapInitAuthPackages().
◆ LsapDeleteLogonSession()
Definition at line 201 of file session.c.
Referenced by LsapInitAuthPackages(), and LsapLogonUser().
◆ LsapEnumLogonSessions()
| NTSTATUS LsapEnumLogonSessions | ( | IN OUT PLSA_API_MSG | RequestMsg | ) |
Definition at line 299 of file session.c.
Referenced by AuthPortThreadRoutine().
◆ LsapGetCredentials()
| NTSTATUS NTAPI LsapGetCredentials | ( | _In_ PLUID | LogonId, |
| _In_ ULONG | AuthenticationPackage, | ||
| _Inout_ PULONG | QueryContext, | ||
| _In_ BOOLEAN | RetrieveAllCredentials, | ||
| _Inout_ PLSA_STRING | PrimaryKeyValue, | ||
| _Out_ PULONG | PrimaryKeyLength, | ||
| _Out_ PLSA_STRING | Credentials | ||
| ) |
Definition at line 272 of file session.c.
Referenced by LsapInitAuthPackages().
◆ LsapGetLogonSession()
|
static |
Definition at line 45 of file session.c.
Referenced by LsapCreateLogonSession(), LsapDeleteLogonSession(), LsapGetLogonSessionData(), and LsapSetLogonSessionData().
◆ LsapGetLogonSessionData()
| NTSTATUS LsapGetLogonSessionData | ( | IN OUT PLSA_API_MSG | RequestMsg | ) |
Definition at line 395 of file session.c.
Referenced by AuthPortThreadRoutine().
◆ LsapInitLogonSessions()
◆ LsapSetLogonSessionData()
| NTSTATUS LsapSetLogonSessionData | ( | _In_ PLUID | LogonId, |
| _In_ ULONG | LogonType, | ||
| _In_ PUNICODE_STRING | UserName, | ||
| _In_ PUNICODE_STRING | LogonDomain, | ||
| _In_ PSID | Sid | ||
| ) |
Definition at line 67 of file session.c.
Referenced by LsapLogonUser().
Variable Documentation
◆ SessionCount
| ULONG SessionCount |
Definition at line 31 of file session.c.
Referenced by LsapCreateLogonSession(), LsapDeleteLogonSession(), LsapEnumLogonSessions(), and LsapInitLogonSessions().
◆ SessionListHead
| LIST_ENTRY SessionListHead |
Definition at line 30 of file session.c.
Referenced by LsapCreateLogonSession(), LsapEnumLogonSessions(), LsapGetLogonSession(), and LsapInitLogonSessions().