#include <ntoskrnl.h>#include <debug.h>
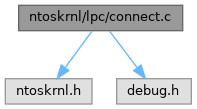
Include dependency graph for connect.c:
Go to the source code of this file.
Macros | |
| #define | NDEBUG |
Functions | |
| PVOID NTAPI | LpcpFreeConMsg (IN OUT PLPCP_MESSAGE *Message, IN OUT PLPCP_CONNECTION_MESSAGE *ConnectMessage, IN PETHREAD CurrentThread) |
| NTSTATUS NTAPI | NtSecureConnectPort (OUT PHANDLE PortHandle, IN PUNICODE_STRING PortName, IN PSECURITY_QUALITY_OF_SERVICE SecurityQos, IN OUT PPORT_VIEW ClientView OPTIONAL, IN PSID ServerSid OPTIONAL, IN OUT PREMOTE_PORT_VIEW ServerView OPTIONAL, OUT PULONG MaxMessageLength OPTIONAL, IN OUT PVOID ConnectionInformation OPTIONAL, IN OUT PULONG ConnectionInformationLength OPTIONAL) |
| NTSTATUS NTAPI | NtConnectPort (OUT PHANDLE PortHandle, IN PUNICODE_STRING PortName, IN PSECURITY_QUALITY_OF_SERVICE SecurityQos, IN OUT PPORT_VIEW ClientView OPTIONAL, IN OUT PREMOTE_PORT_VIEW ServerView OPTIONAL, OUT PULONG MaxMessageLength OPTIONAL, IN OUT PVOID ConnectionInformation OPTIONAL, IN OUT PULONG ConnectionInformationLength OPTIONAL) |
Macro Definition Documentation
◆ NDEBUG
Function Documentation
◆ LpcpFreeConMsg()
| PVOID NTAPI LpcpFreeConMsg | ( | IN OUT PLPCP_MESSAGE * | Message, |
| IN OUT PLPCP_CONNECTION_MESSAGE * | ConnectMessage, | ||
| IN PETHREAD | CurrentThread | ||
| ) |
Definition at line 19 of file connect.c.
22{
23 PVOID SectionToMap;
25
26 /* Acquire the LPC lock */
28
29 /* Check if the reply chain is not empty */
31 {
32 /* Remove this entry and re-initialize it */
33 RemoveEntryList(&CurrentThread->LpcReplyChain);
34 InitializeListHead(&CurrentThread->LpcReplyChain);
35 }
36
37 /* Check if there's a reply message */
40 {
41 /* Get the message */
43
44 /* Check if it's got messages */
46 {
47 /* Clear the list */
50 }
51
52 /* Clear message data */
53 CurrentThread->LpcReceivedMessageId = 0;
54 CurrentThread->LpcReplyMessage = NULL;
55
56 /* Get the connection message and clear the section */
58 SectionToMap = (*ConnectMessage)->SectionToMap;
59 (*ConnectMessage)->SectionToMap = NULL;
60 }
61 else
62 {
63 /* No message to return */
65 SectionToMap = NULL;
66 }
67
68 /* Release the lock and return the section */
70 return SectionToMap;
71}
VOID FASTCALL KeReleaseGuardedMutex(IN OUT PKGUARDED_MUTEX GuardedMutex)
Definition: gmutex.c:53
VOID FASTCALL KeAcquireGuardedMutex(IN PKGUARDED_MUTEX GuardedMutex)
Definition: gmutex.c:42
Definition: nsiface.idl:2307
FORCEINLINE PLPCP_MESSAGE LpcpGetMessageFromThread(IN PETHREAD Thread)
Definition: lpc_x.h:129
struct _LPCP_CONNECTION_MESSAGE * PLPCP_CONNECTION_MESSAGE
Definition: lpctypes.h:238
BOOL WINAPI ReplyMessage(_In_ LRESULT)
Referenced by NtSecureConnectPort().
◆ NtConnectPort()
| NTSTATUS NTAPI NtConnectPort | ( | OUT PHANDLE | PortHandle, |
| IN PUNICODE_STRING | PortName, | ||
| IN PSECURITY_QUALITY_OF_SERVICE | SecurityQos, | ||
| IN OUT PPORT_VIEW ClientView | OPTIONAL, | ||
| IN OUT PREMOTE_PORT_VIEW ServerView | OPTIONAL, | ||
| OUT PULONG MaxMessageLength | OPTIONAL, | ||
| IN OUT PVOID ConnectionInformation | OPTIONAL, | ||
| IN OUT PULONG ConnectionInformationLength | OPTIONAL | ||
| ) |
Definition at line 777 of file connect.c.
785{
786 /* Call the newer API */
788 PortName,
789 SecurityQos,
790 ClientView,
791 NULL,
792 ServerView,
793 MaxMessageLength,
794 ConnectionInformation,
795 ConnectionInformationLength);
796}
NTSTATUS NTAPI NtSecureConnectPort(OUT PHANDLE PortHandle, IN PUNICODE_STRING PortName, IN PSECURITY_QUALITY_OF_SERVICE SecurityQos, IN OUT PPORT_VIEW ClientView OPTIONAL, IN PSID ServerSid OPTIONAL, IN OUT PREMOTE_PORT_VIEW ServerView OPTIONAL, OUT PULONG MaxMessageLength OPTIONAL, IN OUT PVOID ConnectionInformation OPTIONAL, IN OUT PULONG ConnectionInformationLength OPTIONAL)
Definition: connect.c:80
Referenced by ClientThread(), LsaConnectUntrusted(), LsapOpenLsaPort(), LsapRmInitializeServer(), main(), SmConnectToSm(), and SmpHandleConnectionRequest().
◆ NtSecureConnectPort()
| NTSTATUS NTAPI NtSecureConnectPort | ( | OUT PHANDLE | PortHandle, |
| IN PUNICODE_STRING | PortName, | ||
| IN PSECURITY_QUALITY_OF_SERVICE | SecurityQos, | ||
| IN OUT PPORT_VIEW ClientView | OPTIONAL, | ||
| IN PSID ServerSid | OPTIONAL, | ||
| IN OUT PREMOTE_PORT_VIEW ServerView | OPTIONAL, | ||
| OUT PULONG MaxMessageLength | OPTIONAL, | ||
| IN OUT PVOID ConnectionInformation | OPTIONAL, | ||
| IN OUT PULONG ConnectionInformationLength | OPTIONAL | ||
| ) |
Definition at line 80 of file connect.c.
89{
93#if DBG
94 UNICODE_STRING CapturedPortName;
95#endif
96 SECURITY_QUALITY_OF_SERVICE CapturedQos;
97 PORT_VIEW CapturedClientView;
98 PSID CapturedServerSid;
99 ULONG ConnectionInfoLength = 0;
102 PLPCP_CONNECTION_MESSAGE ConnectMessage;
103 ULONG PortMessageLength;
105 PVOID SectionToMap;
108 PTOKEN_USER TokenUserInfo;
109
110 PAGED_CODE();
111
112 /* Check if the call comes from user mode */
114 {
115 /* Enter SEH for probing the parameters */
116 _SEH2_TRY
117 {
118 /* Probe the PortHandle */
119 ProbeForWriteHandle(PortHandle);
120
121 /* Probe and capture the QoS */
124 /* NOTE: Do not care about CapturedQos.Length */
125
126 /* The following parameters are optional */
127
128 /* Capture the client view */
129 if (ClientView)
130 {
133
134 /* Validate the size of the client view */
136 {
137 /* Invalid size */
139 }
140 }
141
142 /* Capture the server view */
143 if (ServerView)
144 {
146
147 /* Validate the size of the server view */
149 {
150 /* Invalid size */
152 }
153 }
154
155 if (MaxMessageLength)
156 ProbeForWriteUlong(MaxMessageLength);
157
158 /* Capture connection information length */
159 if (ConnectionInformationLength)
160 {
161 ProbeForWriteUlong(ConnectionInformationLength);
163 }
164
165 /* Probe the ConnectionInformation */
166 if (ConnectionInformation)
168
169 CapturedServerSid = ServerSid;
170 if (ServerSid)
171 {
172 /* Capture it */
174 PreviousMode,
175 PagedPool,
176 TRUE,
177 &CapturedServerSid);
179 {
182 }
183 }
184 }
186 {
187 /* There was an exception, return the exception code */
189 }
190 _SEH2_END;
191 }
192 else
193 {
194 CapturedQos = *SecurityQos;
195 /* NOTE: Do not care about CapturedQos.Length */
196
197 /* The following parameters are optional */
198
199 /* Capture the client view */
200 if (ClientView)
201 {
202 /* Validate the size of the client view */
203 if (ClientView->Length != sizeof(*ClientView))
204 {
205 /* Invalid size */
207 }
208 CapturedClientView = *ClientView;
209 }
210
211 /* Capture the server view */
212 if (ServerView)
213 {
214 /* Validate the size of the server view */
216 {
217 /* Invalid size */
219 }
220 }
221
222 /* Capture connection information length */
223 if (ConnectionInformationLength)
224 ConnectionInfoLength = *ConnectionInformationLength;
225
226 CapturedServerSid = ServerSid;
227 }
228
229#if DBG
230 /* Capture the port name for DPRINT only - ObReferenceObjectByName does
231 * its own capture. As it is used only for debugging, ignore any failure;
232 * the string is zeroed out in such case. */
234
236 "Name: %wZ. SecurityQos: %p. Views: %p/%p. Sid: %p\n",
237 &CapturedPortName,
238 SecurityQos,
239 ClientView,
240 ServerView,
241 ServerSid);
242#endif
243
244 /* Get the port */
246 0,
247 NULL,
248 PORT_CONNECT,
249 LpcPortObjectType,
250 PreviousMode,
251 NULL,
254 {
255#if DBG
258#endif
259
260 if (CapturedServerSid != ServerSid)
262
264 }
265
266 /* This has to be a connection port */
268 {
269#if DBG
270 DPRINT1("Port '%wZ' is not a connection port (Flags: 0x%lx)\n", &CapturedPortName, Port->Flags);
272#endif
273
274 /* It isn't, so fail */
276
277 if (CapturedServerSid != ServerSid)
279
281 }
282
283 /* Check if we have a (captured) SID */
284 if (ServerSid)
285 {
286 /* Make sure that we have a server */
288 {
289 /* Get its token and query user information */
293
294 /* Check for success */
296 {
297 /* Compare the SIDs */
299 {
300 /* Fail */
301#if DBG
303#endif
305 }
306
307 /* Free token information */
309 }
310 }
311 else
312 {
313 /* Invalid SID */
314#if DBG
316#endif
318 }
319
320 /* Finally release the captured SID, we don't need it anymore */
321 if (CapturedServerSid != ServerSid)
323 }
324
325#if DBG
327#endif
328
329 /* Check if SID failed */
331 {
332 /* Quit */
335 }
336
337 /* Create the client port */
339 LpcPortObjectType,
340 NULL,
341 PreviousMode,
342 NULL,
344 0,
345 0,
348 {
349 /* Failed, dereference the server port and return */
353 }
354
355 /*
356 * Setup the client port -- From now on, dereferencing the client port
357 * will automatically dereference the connection port too.
358 */
363 ClientPort->SecurityQos = CapturedQos;
366
367 /* Check if we have dynamic security */
369 {
370 /* Remember that */
372 }
373 else
374 {
375 /* Create our own client security */
377 &CapturedQos,
378 FALSE,
379 &ClientPort->StaticSecurity);
381 {
382 /* Security failed, dereference and return */
386 }
387 }
388
389 /* Initialize the port queue */
392 {
393 /* Failed */
397 }
398
399 /* Check if we have a client view */
400 if (ClientView)
401 {
402 /* Get the section handle */
404 SECTION_MAP_READ |
405 SECTION_MAP_WRITE,
406 MmSectionObjectType,
407 PreviousMode,
408 (PVOID*)&SectionToMap,
409 NULL);
411 {
412 /* Fail */
416 }
417
418 /* Set the section offset */
420
421 /* Map it */
423 PsGetCurrentProcess(),
424 &ClientPort->ClientSectionBase,
425 0,
426 0,
427 &SectionOffset,
428 &CapturedClientView.ViewSize,
429 ViewUnmap,
430 0,
431 PAGE_READWRITE);
432
433 /* Update the offset */
435
436 /* Check for failure */
438 {
439 /* Fail */
441 ObDereferenceObject(SectionToMap);
444 }
445
446 /* Update the base */
448
449 /* Reference and remember the process */
452 }
453 else
454 {
455 /* No section */
456 SectionToMap = NULL;
457 }
458
459 /* Normalize connection information */
461 {
462 /* Use the port's maximum allowed value */
463 ConnectionInfoLength = Port->MaxConnectionInfoLength;
464 }
465
466 /* Allocate a message from the port zone */
469 {
470 /* Fail if we couldn't allocate a message */
475 }
476
477 /* Set pointer to the connection message and fill in the CID */
480
481 /* Check if we have a client view */
482 if (ClientView)
483 {
484 /* Set the view size */
486
487 /* Copy the client view and clear the server view */
489 &CapturedClientView,
490 sizeof(CapturedClientView));
492 }
493 else
494 {
495 /* Set the size to 0 and clear the connect message */
496 Message->Request.ClientViewSize = 0;
498 }
499
500 /* Set the section and client port. Port is NULL for now */
502 ConnectMessage->SectionToMap = SectionToMap;
503
504 /* Set the data for the connection request message */
508 Message->Request.u1.s1.DataLength;
510
511 /* Check if we have connection information */
512 if (ConnectionInformation)
513 {
514 _SEH2_TRY
515 {
516 /* Copy it in */
517 RtlCopyMemory(ConnectMessage + 1,
518 ConnectionInformation,
519 ConnectionInfoLength);
520 }
522 {
524 _SEH2_GetExceptionCode());
525
526 /* Cleanup and return the exception code */
527
528 /* Free the message we have */
530
531 /* Dereference other objects */
534
535 /* Return status */
537 }
538 _SEH2_END;
539 }
540
541 /* Reset the status code */
543
544 /* Acquire the port lock */
546
547 /* Check if someone already deleted the port name */
549 {
550 /* Fail the request */
552 }
553 else
554 {
555 /* Associate no thread yet */
557
558 /* Generate the Message ID and set it */
562
563 /* Insert the message into the queue and thread chain */
567
568 /* Now we can finally reference the client port and link it */
571
572 /* Enter a critical region */
573 KeEnterCriticalRegion();
574 }
575
576 /* Add another reference to the port */
578
579 /* Release the lock */
581
582 /* Check for success */
584 {
586 "Messages: %p/%p. Ports: %p/%p. Status: %lx\n",
587 Message,
588 ConnectMessage,
589 Port,
590 ClientPort,
591 Status);
592
593 /* If this is a waitable port, set the event */
596
597 /* Release the queue semaphore and leave the critical region */
599 KeLeaveCriticalRegion();
600
601 /* Now wait for a reply and set 'Status' */
603 }
604
605 /* Now, always free the connection message */
607
608 /* Check for failure */
610 {
611 /* Check if the semaphore got signaled in the meantime */
613 {
614 /* Wait on it */
616 WrExecutive,
617 KernelMode,
618 FALSE,
619 NULL);
620 }
621
622 goto Failure;
623 }
624
625 /* Check if we got a message back */
627 {
628 /* Check for new return length */
631 {
632 /* Set new normalized connection length */
633 ConnectionInfoLength = Message->Request.u1.s1.DataLength -
635 }
636
637 /* Check if the caller had connection information */
638 if (ConnectionInformation)
639 {
640 _SEH2_TRY
641 {
642 /* Return the connection information length if needed */
643 if (ConnectionInformationLength)
644 *ConnectionInformationLength = ConnectionInfoLength;
645
646 /* Return the connection information */
647 RtlCopyMemory(ConnectionInformation,
648 ConnectMessage + 1,
649 ConnectionInfoLength);
650 }
652 {
653 /* Cleanup and return the exception code */
656 }
657 _SEH2_END;
658 }
659
660 /* Make sure we had a connected port */
662 {
663 /* Get the message length before the port might get killed */
664 PortMessageLength = Port->MaxMessageLength;
665
666 /* Insert the client port */
668 NULL,
669 PORT_ALL_ACCESS,
670 0,
671 NULL,
672 &Handle);
674 {
676 "Handle: %p. Length: %lx\n",
677 Handle,
678 PortMessageLength);
679
680 _SEH2_TRY
681 {
682 /* Return the handle */
683 *PortHandle = Handle;
684
685 /* Check if maximum length was requested */
686 if (MaxMessageLength)
687 *MaxMessageLength = PortMessageLength;
688
689 /* Check if we had a client view */
690 if (ClientView)
691 {
692 /* Copy it back */
693 RtlCopyMemory(ClientView,
694 &ConnectMessage->ClientView,
695 sizeof(*ClientView));
696 }
697
698 /* Check if we had a server view */
699 if (ServerView)
700 {
701 /* Copy it back */
702 RtlCopyMemory(ServerView,
703 &ConnectMessage->ServerView,
704 sizeof(*ServerView));
705 }
706 }
708 {
709 /* An exception happened, close the opened handle */
712 }
713 _SEH2_END;
714 }
715 }
716 else
717 {
718 /* No connection port, we failed */
720
721 /* Acquire the lock */
723
724 /* Check if it's because the name got deleted */
727 {
728 /* Set the correct status */
730 }
731 else
732 {
733 /* Otherwise, the caller refused us */
735 }
736
737 /* Release the lock */
739
740 /* Kill the port */
742 }
743
744 /* Free the message */
746 }
747 else
748 {
749 /* No reply message, fail */
751 goto Failure;
752 }
753
755
756 /* Return status */
758
759Failure:
760 /* Check if we had a message and free it */
762
763 /* Dereference other objects */
767
768 /* Return status */
770}
_In_ PVOID _In_ ULONG _Out_ PVOID _In_ ULONG _Inout_ PULONG _In_ KPROCESSOR_MODE PreviousMode
Definition: KdSystemDebugControl.c:35
Definition: tokenizer.hpp:28
#define KeWaitForSingleObject(pEvt, foo, a, b, c)
Definition: env_spec_w32.h:478
VOID NTAPI ProbeForRead(IN CONST VOID *Address, IN SIZE_T Length, IN ULONG Alignment)
Definition: exintrin.c:102
VOID NTAPI ProbeForWrite(IN PVOID Address, IN SIZE_T Length, IN ULONG Alignment)
Definition: exintrin.c:143
VOID NTAPI LpcpFreeToPortZone(IN PLPCP_MESSAGE Message, IN ULONG LockFlags)
Definition: close.c:52
NTSTATUS NTAPI LpcpInitializePortQueue(IN PLPCP_PORT_OBJECT Port)
Definition: create.c:19
static __inline PLPCP_MESSAGE LpcpAllocateFromPortZone(VOID)
Definition: lpc_x.h:100
struct _LPCP_MESSAGE LPCP_MESSAGE
struct _LPCP_CONNECTION_MESSAGE LPCP_CONNECTION_MESSAGE
NTKERNELAPI NTSTATUS NTAPI SeCreateClientSecurity(IN PETHREAD Thread, IN PSECURITY_QUALITY_OF_SERVICE QualityOfService, IN BOOLEAN RemoteClient, OUT PSECURITY_CLIENT_CONTEXT ClientContext)
_In_ HANDLE _Outptr_result_bytebuffer_ ViewSize _Pre_valid_ PVOID _In_ ULONG_PTR _In_ SIZE_T _Inout_opt_ PLARGE_INTEGER SectionOffset
Definition: mmfuncs.h:407
NTSYSAPI BOOLEAN NTAPI RtlEqualSid(_In_ PSID Sid1, _In_ PSID Sid2)
VOID NTAPI SepReleaseSid(_In_ PSID CapturedSid, _In_ KPROCESSOR_MODE AccessMode, _In_ BOOLEAN CaptureIfKernel)
Releases a captured SID.
Definition: sid.c:400
NTSTATUS NTAPI SepCaptureSid(_In_ PSID InputSid, _In_ KPROCESSOR_MODE AccessMode, _In_ POOL_TYPE PoolType, _In_ BOOLEAN CaptureIfKernel, _Out_ PSID *CapturedSid)
Captures a SID.
Definition: sid.c:314
PVOID NTAPI LpcpFreeConMsg(IN OUT PLPCP_MESSAGE *Message, IN OUT PLPCP_CONNECTION_MESSAGE *ConnectMessage, IN PETHREAD CurrentThread)
Definition: connect.c:19
PACCESS_TOKEN NTAPI PsReferencePrimaryToken(PEPROCESS Process)
Definition: security.c:440
NTSTATUS NTAPI ObCloseHandle(IN HANDLE Handle, IN KPROCESSOR_MODE AccessMode)
Definition: obhandle.c:3379
NTSTATUS NTAPI ObInsertObject(IN PVOID Object, IN PACCESS_STATE AccessState OPTIONAL, IN ACCESS_MASK DesiredAccess, IN ULONG ObjectPointerBias, OUT PVOID *NewObject OPTIONAL, OUT PHANDLE Handle)
Definition: obhandle.c:2935
NTSTATUS NTAPI ObCreateObject(IN KPROCESSOR_MODE ProbeMode OPTIONAL, IN POBJECT_TYPE Type, IN POBJECT_ATTRIBUTES ObjectAttributes OPTIONAL, IN KPROCESSOR_MODE AccessMode, IN OUT PVOID ParseContext OPTIONAL, IN ULONG ObjectSize, IN ULONG PagedPoolCharge OPTIONAL, IN ULONG NonPagedPoolCharge OPTIONAL, OUT PVOID *Object)
Definition: oblife.c:1039
NTSTATUS NTAPI ObReferenceObjectByName(IN PUNICODE_STRING ObjectPath, IN ULONG Attributes, IN PACCESS_STATE PassedAccessState, IN ACCESS_MASK DesiredAccess, IN POBJECT_TYPE ObjectType, IN KPROCESSOR_MODE AccessMode, IN OUT PVOID ParseContext, OUT PVOID *ObjectPtr)
Definition: obref.c:409
NTSTATUS NTAPI ObReferenceObjectByHandle(IN HANDLE Handle, IN ACCESS_MASK DesiredAccess, IN POBJECT_TYPE ObjectType, IN KPROCESSOR_MODE AccessMode, OUT PVOID *Object, OUT POBJECT_HANDLE_INFORMATION HandleInformation OPTIONAL)
Definition: obref.c:494
static __inline NTSTATUS ProbeAndCaptureUnicodeString(OUT PUNICODE_STRING Dest, IN KPROCESSOR_MODE CurrentMode, IN const UNICODE_STRING *UnsafeSrc)
Definition: probe.h:142
static __inline VOID ReleaseCapturedUnicodeString(IN PUNICODE_STRING CapturedString, IN KPROCESSOR_MODE CurrentMode)
Definition: probe.h:239
NTSTATUS NTAPI MmMapViewOfSection(_In_ PVOID SectionObject, _In_ PEPROCESS Process, _Outptr_result_bytebuffer_(*ViewSize) _Pre_opt_valid_ PVOID *BaseAddress, _In_ ULONG_PTR ZeroBits, _In_ SIZE_T CommitSize, _Inout_opt_ PLARGE_INTEGER SectionOffset, _Inout_ PSIZE_T ViewSize, _In_range_(ViewShare, ViewUnmap) SECTION_INHERIT InheritDisposition, _In_ ULONG AllocationType, _In_ ULONG Protect)
Definition: section.c:4031
LONG NTAPI KeReadStateSemaphore(IN PKSEMAPHORE Semaphore)
Definition: semphobj.c:41
Definition: pstypes.h:1186
Definition: lpctypes.h:255
Definition: lpctypes.h:210
Definition: ntifs.template.h:1627
Definition: ntifs.template.h:1637
Definition: lsa.idl:63
SECURITY_CONTEXT_TRACKING_MODE ContextTrackingMode
Definition: lsa.idl:66
Definition: ms-dtyp.idl:198
Definition: setypes.h:1021
Definition: setypes.h:216
Definition: env_spec_w32.h:368
NTSTATUS NTAPI SeQueryInformationToken(_In_ PACCESS_TOKEN AccessToken, _In_ TOKEN_INFORMATION_CLASS TokenInformationClass, _Outptr_result_buffer_(_Inexpressible_(token-dependent)) PVOID *TokenInformation)
Queries information details about the given token to the call. The difference between NtQueryInformat...
Definition: tokencls.c:95
Definition: typedefs.h:103
Referenced by CsrpConnectToServer(), and NtConnectPort().