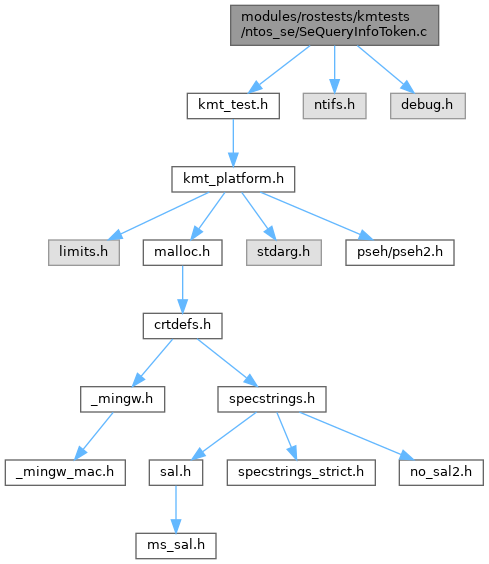
Include dependency graph for SeQueryInfoToken.c:
Go to the source code of this file.
Macros | |
| #define | NDEBUG |
Functions | |
| void | TestsSeQueryInformationToken (PACCESS_TOKEN Token) |
| START_TEST (SeQueryInfoToken) | |
Variables | |
| static GENERIC_MAPPING | ProcessGenericMapping |
Macro Definition Documentation
◆ NDEBUG
| #define NDEBUG |
Definition at line 13 of file SeQueryInfoToken.c.
Function Documentation
◆ START_TEST()
| START_TEST | ( | SeQueryInfoToken | ) |
Definition at line 224 of file SeQueryInfoToken.c.
225{
231 PPRIVILEGE_SET NewPrivilegeSet;
232 ULONG InitialPrivilegeCount;
233 BOOLEAN Checker;
237 PTOKEN_PRIVILEGES TPrivileges;
240
242
246
247 // Testing SQIT with current Token
249
250 //----------------------------------------------------------------//
251 // Creating an ACCESS_STATE structure //
252 //----------------------------------------------------------------//
253
255 // AUX_ACCESS_DATA gets larger in newer Windows version.
256 // This is the largest known size, found in Windows 10/11.
258
260 AuxData,
261 DesiredAccess,
263 );
264
266
270
271 // Testing SQIT with AccessState Token
273
274 //----------------------------------------------------------------//
275 // Testing other functions //
276 //----------------------------------------------------------------//
277
278 //----------------------------------------------------------------//
279 // Testing SeAppendPrivileges //
280 //----------------------------------------------------------------//
281
284
285 // Testing SeAppendPrivileges. Must change PrivilegeCount to 2 (1 + 1)
286
289 'QSmK');
290 NewPrivilegeSet->PrivilegeCount = 1;
291
296
297 //----------------------------------------------------------------//
298
299 // Testing SeAppendPrivileges. Must change PrivilegeCount to 6 (2 + 4)
300
303 'QSmK');
304 NewPrivilegeSet->PrivilegeCount = 4;
305
310
311 //----------------------------------------------------------------//
312 // Testing SePrivilegeCheck //
313 //----------------------------------------------------------------//
314
315 // KPROCESSOR_MODE is set to KernelMode ===> Always return TRUE
316 ok(SePrivilegeCheck(AuxData->PrivilegesUsed, &(AccessState->SubjectSecurityContext), KernelMode), "SePrivilegeCheck failed with KernelMode mode arg\n");
317 // and call it again
318 ok(SePrivilegeCheck(AuxData->PrivilegesUsed, &(AccessState->SubjectSecurityContext), KernelMode), "SePrivilegeCheck failed with KernelMode mode arg\n");
319
320 //----------------------------------------------------------------//
321
322 // KPROCESSOR_MODE is set to UserMode. Expect false
323 ok(!SePrivilegeCheck(AuxData->PrivilegesUsed, &(AccessState->SubjectSecurityContext), UserMode), "SePrivilegeCheck unexpected success with UserMode arg\n");
324
325 //----------------------------------------------------------------//
326
327 //----------------------------------------------------------------//
328 // Testing SeFreePrivileges //
329 //----------------------------------------------------------------//
330
331 // FIXME: KernelMode will automatically get all access granted without
332 // getting Privileges filled in. For UserMode, Privileges will only get
333 // filled if either WRITE_OWNER or ACCESS_SYSTEM_SECURITY is requested
334 // and granted. So this doesn't really test SeFreePrivileges.
336 Checker = SeAccessCheck(
337 AccessState->SecurityDescriptor,
338 &AccessState->SubjectSecurityContext,
339 FALSE,
340 AccessState->OriginalDesiredAccess,
341 AccessState->PreviouslyGrantedAccess,
342 &Privileges,
343 &ProcessGenericMapping,
344 KernelMode,
345 &AccessMask,
346 &Status
347 );
351 {
354 }
356
357
358 //----------------------------------------------------------------//
359 // Testing SePrivilegeCheck //
360 //----------------------------------------------------------------//
361 // I'm trying to make success call of SePrivilegeCheck from UserMode
362 // If we sets Privileges properly, can we expect true from SePrivilegeCheck?
363 // answer: yes
364 // This test demonstrates it
365
369 {
370 ok(Buffer != NULL, "Wrong. SQIT call was successful with TokenPrivileges arg. But Buffer == NULL\n");
372 {
374 //trace("TPCount = %u\n\n", TPrivileges->PrivilegeCount);
375
378 'QSmK');
379 NewPrivilegeSet->PrivilegeCount = 14;
380
381 ok((SeAppendPrivileges(AccessState, NewPrivilegeSet)) == STATUS_SUCCESS, "SeAppendPrivileges failed\n");
385 {
388 }
389 //trace("AccessState->privCount = %u\n\n", ((PAUX_ACCESS_DATA)(AccessState->AuxData))->PrivilegesUsed->PrivilegeCount);
390
391 ok(SePrivilegeCheck(AuxData->PrivilegesUsed, &(AccessState->SubjectSecurityContext), UserMode), "SePrivilegeCheck fails in UserMode, but I wish it will success\n");
392 }
393 }
394
395 // Call SeFreePrivileges again
396
397 // FIXME: See other SeAccessCheck call above, we're not really testing
398 // SeFreePrivileges here.
400 Checker = SeAccessCheck(
401 AccessState->SecurityDescriptor,
402 &AccessState->SubjectSecurityContext,
403 TRUE,
404 AccessState->OriginalDesiredAccess,
405 AccessState->PreviouslyGrantedAccess,
406 &Privileges,
407 &ProcessGenericMapping,
408 KernelMode,
409 &AccessMask,
410 &Status
411 );
415 {
418 }
420
421 //----------------------------------------------------------------//
422 // Missing for now //
423 //----------------------------------------------------------------//
424
427
429
433}
void TestsSeQueryInformationToken(PACCESS_TOKEN Token)
Definition: SeQueryInfoToken.c:35
BOOLEAN NTAPI SeAccessCheck(_In_ PSECURITY_DESCRIPTOR SecurityDescriptor, _In_ PSECURITY_SUBJECT_CONTEXT SubjectSecurityContext, _In_ BOOLEAN SubjectContextLocked, _In_ ACCESS_MASK DesiredAccess, _In_ ACCESS_MASK PreviouslyGrantedAccess, _Out_ PPRIVILEGE_SET *Privileges, _In_ PGENERIC_MAPPING GenericMapping, _In_ KPROCESSOR_MODE AccessMode, _Out_ PACCESS_MASK GrantedAccess, _Out_ PNTSTATUS AccessStatus)
Determines whether security access rights can be given to an object depending on the security descrip...
Definition: accesschk.c:1994
Definition: bufpool.h:45
Definition: tokenizer.hpp:28
_Inout_ PLIST_ENTRY _In_ PVOID _In_ PSTRING _In_ BOOLEAN _In_ BOOLEAN _In_ ULONG _In_ PFLT_CALLBACK_DATA _In_opt_ PCHECK_FOR_TRAVERSE_ACCESS _In_opt_ PSECURITY_SUBJECT_CONTEXT SubjectContext
Definition: fltkernel.h:2246
GLsizei GLenum const GLvoid GLsizei GLenum GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLint GLint GLint GLshort GLshort GLshort GLubyte GLubyte GLubyte GLuint GLuint GLuint GLushort GLushort GLushort GLbyte GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLfloat GLint GLint GLint GLint GLshort GLshort GLshort GLshort GLubyte GLubyte GLubyte GLubyte GLuint GLuint GLuint GLuint GLushort GLushort GLushort GLushort GLboolean const GLdouble const GLfloat const GLint const GLshort const GLbyte const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLdouble const GLfloat const GLfloat const GLint const GLint const GLshort const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort GLenum GLenum GLenum GLfloat GLenum GLint GLenum GLenum GLenum GLfloat GLenum GLenum GLint GLenum GLfloat GLenum GLint GLint GLushort GLenum GLenum GLfloat GLenum GLenum GLint GLfloat const GLubyte GLenum GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLint GLint GLsizei GLsizei GLint GLenum GLenum const GLvoid GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLenum const GLdouble GLenum GLenum const GLfloat GLenum GLenum const GLint GLsizei GLuint GLfloat GLuint GLbitfield GLfloat GLint GLuint GLboolean GLenum GLfloat GLenum GLbitfield GLenum GLfloat GLfloat GLint GLint const GLfloat GLenum GLfloat GLfloat GLint GLint GLfloat GLfloat GLint GLint const GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat const GLdouble const GLfloat const GLdouble const GLfloat GLint i
Definition: glfuncs.h:248
Definition: nsiface.idl:2307
static PVOID ExAllocatePoolZero(ULONG PoolType, SIZE_T NumberOfBytes, ULONG Tag)
Definition: precomp.h:45
VOID NTAPI SeDeleteAccessState(_In_ PACCESS_STATE AccessState)
Deletes an allocated access state from the memory.
Definition: access.c:150
NTSTATUS NTAPI SeCreateAccessState(_Out_ PACCESS_STATE AccessState, _Out_ __drv_aliasesMem PAUX_ACCESS_DATA AuxData, _In_ ACCESS_MASK Access, _In_ PGENERIC_MAPPING GenericMapping)
Creates an access state.
Definition: access.c:121
BOOLEAN NTAPI SePrivilegeCheck(_In_ PPRIVILEGE_SET Privileges, _In_ PSECURITY_SUBJECT_CONTEXT SubjectContext, _In_ KPROCESSOR_MODE PreviousMode)
Checks if a set of privileges exist and match within a security subject context.
Definition: priv.c:698
VOID NTAPI SeFreePrivileges(_In_ PPRIVILEGE_SET Privileges)
Frees a set of privileges.
Definition: priv.c:669
NTSTATUS NTAPI SeAppendPrivileges(_Inout_ PACCESS_STATE AccessState, _In_ PPRIVILEGE_SET Privileges)
Appends additional privileges.
Definition: priv.c:588
Definition: setypes.h:224
Definition: setypes.h:257
Definition: setypes.h:85
Definition: setypes.h:217
Definition: setypes.h:1034
LUID_AND_ATTRIBUTES Privileges[ANYSIZE_ARRAY]
Definition: setypes.h:1036
VOID NTAPI SeLockSubjectContext(_In_ PSECURITY_SUBJECT_CONTEXT SubjectContext)
Locks both the referenced primary and client access tokens of a security subject context.
Definition: subject.c:107
VOID NTAPI SeUnlockSubjectContext(_In_ PSECURITY_SUBJECT_CONTEXT SubjectContext)
Unlocks both the referenced primary and client access tokens of a security subject context.
Definition: subject.c:138
VOID NTAPI SeCaptureSubjectContext(_Out_ PSECURITY_SUBJECT_CONTEXT SubjectContext)
Captures the security subject context of the calling thread and calling process.
Definition: subject.c:85
NTSTATUS NTAPI SeQueryInformationToken(_In_ PACCESS_TOKEN AccessToken, _In_ TOKEN_INFORMATION_CLASS TokenInformationClass, _Outptr_result_buffer_(_Inexpressible_(token-dependent)) PVOID *TokenInformation)
Queries information details about the given token to the call. The difference between NtQueryInformat...
Definition: tokencls.c:95
_Must_inspect_result_ _In_ WDFDEVICE _In_ ULONG _In_ ACCESS_MASK DesiredAccess
Definition: wdfdevice.h:2664
_In_ PSECURITY_SUBJECT_CONTEXT _In_ BOOLEAN _In_ ACCESS_MASK _In_ ACCESS_MASK _Outptr_opt_ PPRIVILEGE_SET * Privileges
Definition: sefuncs.h:17
#define SeQuerySubjectContextToken(SubjectContext)
Definition: sefuncs.h:583
_In_opt_ PVOID _In_opt_ PUNICODE_STRING _In_ PSECURITY_DESCRIPTOR _In_ PACCESS_STATE AccessState
Definition: sefuncs.h:417
struct _TOKEN_PRIVILEGES * PTOKEN_PRIVILEGES
◆ TestsSeQueryInformationToken()
| void TestsSeQueryInformationToken | ( | PACCESS_TOKEN | Token | ) |
Definition at line 35 of file SeQueryInfoToken.c.
36{
40 PTOKEN_OWNER Towner;
41 PTOKEN_DEFAULT_DACL TDefDacl;
42 PTOKEN_GROUPS TGroups;
43 ULONG GroupCount;
44 PACL acl;
45 PTOKEN_STATISTICS TStats;
46 PTOKEN_TYPE TType;
47 PTOKEN_USER TUser;
50
51 //----------------------------------------------------------------//
52 // Testing SeQueryInformationToken with various args //
53 //----------------------------------------------------------------//
54
56
58
62 {
64
66 {
71 }
72 }
73
74 //----------------------------------------------------------------//
75
80 {
81 ok(Buffer != NULL, "Wrong. SQIT call was successful with TokenDefaultDacl arg. But Buffer == NULL\n");
83 {
85 acl = TDefDacl->DefaultDacl;
86 ok(((acl->AclRevision == ACL_REVISION || acl->AclRevision == ACL_REVISION_DS) == TRUE), "DACL is invalid\n");
88 }
89 }
90
91 //----------------------------------------------------------------//
92
97 {
98 ok(Buffer != NULL, "Wrong. SQIT call was successful with TokenGroups arg. But Buffer == NULL\n");
100 {
102 GroupCount = TGroups->GroupCount;
105 {
108 {
110 break;
111 }
112 }
115 }
116 }
117
118 //----------------------------------------------------------------//
119
120 // Call SQIT with TokenImpersonationLevel argument. Although our token
121 // is not an impersonation token, the call will outright fail.
122
125 ok(Status == STATUS_INVALID_INFO_CLASS, "SQIT with TokenImpersonationLevel must return STATUS_INVALID_INFO_CLASS but got 0x%08X\n", Status);
126 ok(Buffer == NULL, "SQIT has failed to query the impersonation level but buffer is not NULL!\n");
127
128 //----------------------------------------------------------------//
129
130 // Call SQIT with the 4 classes (TokenOrigin, TokenGroupsAndPrivileges,
131 // TokenRestrictedSids and TokenSandBoxInert) are not supported by
132 // SeQueryInformationToken (only NtQueryInformationToken supports them).
133 //
134
137 ok(Status == STATUS_INVALID_INFO_CLASS, "SQIT with TokenOrigin failed with Status 0x%08X; expected STATUS_INVALID_INFO_CLASS\n", Status);
139
142 ok(Status == STATUS_INVALID_INFO_CLASS, "SQIT with TokenGroupsAndPrivileges failed with Status 0x%08X; expected STATUS_INVALID_INFO_CLASS\n", Status);
144
147 ok(Status == STATUS_INVALID_INFO_CLASS, "SQIT with TokenRestrictedSids failed with Status 0x%08X; expected STATUS_INVALID_INFO_CLASS\n", Status);
149
152 ok(Status == STATUS_INVALID_INFO_CLASS, "SQIT with TokenSandBoxInert failed with Status 0x%08X; expected STATUS_INVALID_INFO_CLASS\n", Status);
154
155 //----------------------------------------------------------------//
156
161 {
162 ok(Buffer != NULL, "Wrong. SQIT call was successful with TokenStatistics arg. But Buffer == NULL\n");
164 {
166 // just put 0 into 1st arg or use trace to print TokenStatistics
167 ok(1, "print statistics:\n\tTokenID = %u_%d\n\tSecurityImperLevel = %d\n\tPrivCount = %d\n\tGroupCount = %d\n\n", TStats->TokenId.LowPart,
169 TStats->ImpersonationLevel,
170 TStats->PrivilegeCount,
171 TStats->GroupCount
172 );
174 }
175 } else {
177 }
178
179 //----------------------------------------------------------------//
180
185 {
188 {
190 ok((*TType == TokenPrimary || *TType == TokenImpersonation), "TokenType in not a primary nor impersonation. FAILED\n");
192 }
193 }
194
195 //----------------------------------------------------------------//
196
201 {
204 {
208 }
209 }
210
211 //----------------------------------------------------------------//
212
216}
_In_ ACCESS_MASK _In_opt_ POBJECT_ATTRIBUTES _In_ BOOLEAN _In_ TOKEN_TYPE TokenType
Definition: sefuncs.h:411
Definition: xml2sdb.h:97
Definition: ms-dtyp.idl:293
Definition: ms-dtyp.idl:198
Definition: setypes.h:1047
Definition: setypes.h:1025
Definition: setypes.h:1039
Definition: setypes.h:1097
SECURITY_IMPERSONATION_LEVEL ImpersonationLevel
Definition: setypes.h:1102
Definition: setypes.h:1021
struct _TOKEN_GROUPS * PTOKEN_GROUPS
struct _TOKEN_STATISTICS * PTOKEN_STATISTICS
struct _TOKEN_DEFAULT_DACL * PTOKEN_DEFAULT_DACL
struct _TOKEN_USER * PTOKEN_USER
enum _TOKEN_TYPE * PTOKEN_TYPE
Referenced by START_TEST().
Variable Documentation
◆ ProcessGenericMapping
|
static |
Initial value:
=
{
}
#define PROCESS_DUP_HANDLE
Definition at line 18 of file SeQueryInfoToken.c.
Referenced by START_TEST().