#include "samsrv.h"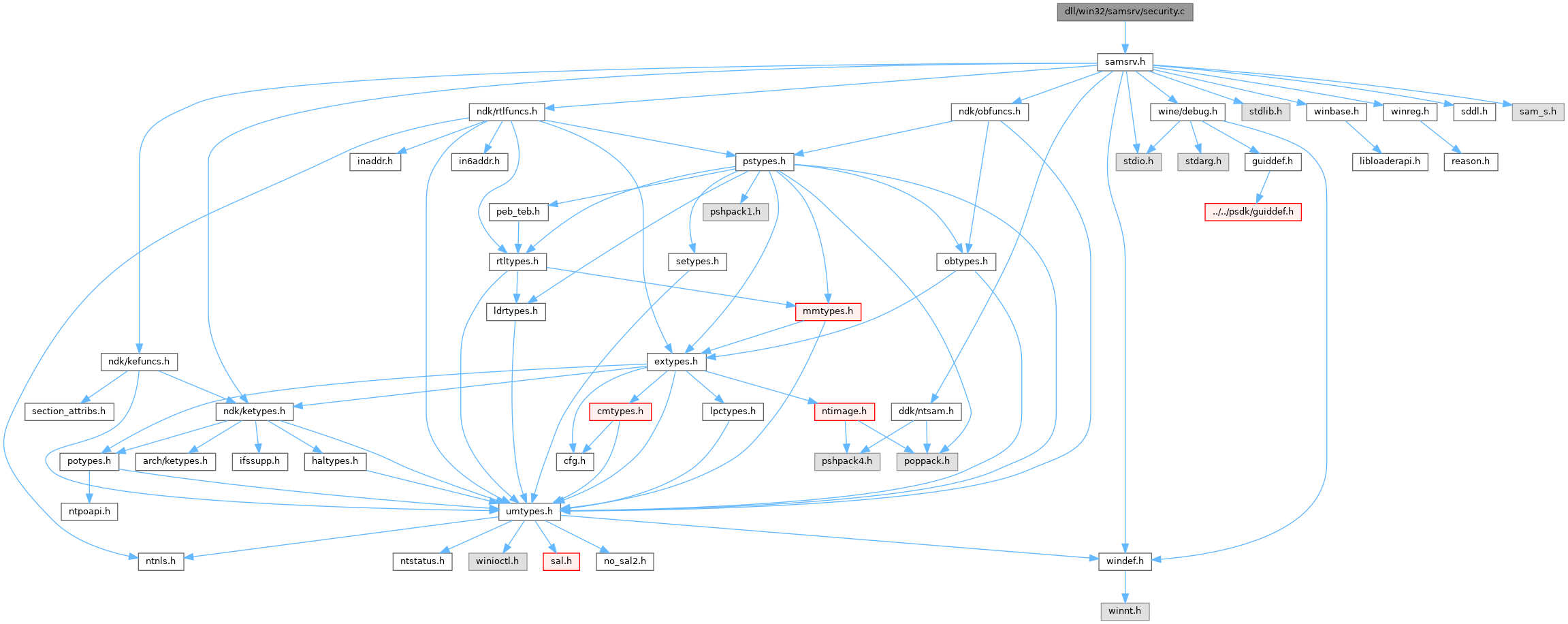
Go to the source code of this file.
Functions | |
| NTSTATUS | SampCreateServerSD (OUT PSECURITY_DESCRIPTOR *ServerSd, OUT PULONG Size) |
| NTSTATUS | SampCreateBuiltinDomainSD (OUT PSECURITY_DESCRIPTOR *ServerSd, OUT PULONG Size) |
| NTSTATUS | SampCreateAccountDomainSD (OUT PSECURITY_DESCRIPTOR *ServerSd, OUT PULONG Size) |
| NTSTATUS | SampCreateAliasSD (OUT PSECURITY_DESCRIPTOR *AliasSd, OUT PULONG Size) |
| NTSTATUS | SampCreateGroupSD (OUT PSECURITY_DESCRIPTOR *GroupSd, OUT PULONG Size) |
| NTSTATUS | SampCreateUserSD (IN PSID UserSid, OUT PSECURITY_DESCRIPTOR *UserSd, OUT PULONG Size) |
Variables | |
| static SID_IDENTIFIER_AUTHORITY | WorldAuthority = {SECURITY_WORLD_SID_AUTHORITY} |
| static SID_IDENTIFIER_AUTHORITY | NtAuthority = {SECURITY_NT_AUTHORITY} |
Function Documentation
◆ SampCreateAccountDomainSD()
| NTSTATUS SampCreateAccountDomainSD | ( | OUT PSECURITY_DESCRIPTOR * | ServerSd, |
| OUT PULONG | Size | ||
| ) |
Definition at line 545 of file security.c.
Referenced by SampSetupCreateDomain().
◆ SampCreateAliasSD()
| NTSTATUS SampCreateAliasSD | ( | OUT PSECURITY_DESCRIPTOR * | AliasSd, |
| OUT PULONG | Size | ||
| ) |
Definition at line 859 of file security.c.
Referenced by SampSetupCreateAliasAccount(), and SamrCreateAliasInDomain().
◆ SampCreateBuiltinDomainSD()
| NTSTATUS SampCreateBuiltinDomainSD | ( | OUT PSECURITY_DESCRIPTOR * | ServerSd, |
| OUT PULONG | Size | ||
| ) |
Definition at line 283 of file security.c.
Referenced by SampSetupCreateDomain().
◆ SampCreateGroupSD()
| NTSTATUS SampCreateGroupSD | ( | OUT PSECURITY_DESCRIPTOR * | GroupSd, |
| OUT PULONG | Size | ||
| ) |
Definition at line 1146 of file security.c.
Referenced by SampSetupCreateGroupAccount(), and SamrCreateGroupInDomain().
◆ SampCreateServerSD()
| NTSTATUS SampCreateServerSD | ( | OUT PSECURITY_DESCRIPTOR * | ServerSd, |
| OUT PULONG | Size | ||
| ) |
Definition at line 21 of file security.c.
Referenced by SampSetupCreateServer().
◆ SampCreateUserSD()
Definition at line 1433 of file security.c.
Referenced by SampSetupCreateUserAccount(), SamrCreateUser2InDomain(), and SamrCreateUserInDomain().
Variable Documentation
◆ NtAuthority
|
static |
Definition at line 15 of file security.c.
◆ WorldAuthority
|
static |
Definition at line 14 of file security.c.
Referenced by AccessCheckEmptyMappingTest(), CmpHiveRootSecurityDescriptor(), CreateBaseAcls(), CreateLogoffSecurityAttributes(), CreateNlsSecurityDescriptor(), CSR_API(), GetAllowedWorldAce(), GetDosDevicesProtection(), QueryTokenPrivilegesAndGroupsTests(), QueryTokenRestrictedSidsTest(), RtlDefaultNpAcl(), SampCreateAccountDomainSD(), SampCreateAliasSD(), SampCreateBuiltinDomainSD(), SampCreateGroupSD(), SampCreateServerSD(), SampCreateUserSD(), ScmCreateSids(), and SmpCreateSecurityDescriptors().