#include "sha1.h"
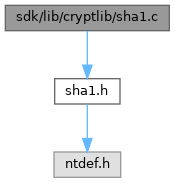
Include dependency graph for sha1.c:
Go to the source code of this file.
Macros | |
| #define | rol(value, bits) (((value) << (bits)) | ((value) >> (32 - (bits)))) |
| #define | DWORD2BE(x) (((x) >> 24) & 0xff) | (((x) >> 8) & 0xff00) | (((x) << 8) & 0xff0000) | (((x) << 24) & 0xff000000); |
| #define | blk0(i) (Block[i] = (rol(Block[i],24)&0xFF00FF00)|(rol(Block[i],8)&0x00FF00FF)) |
| #define | blk1(i) (Block[i&15] = rol(Block[(i+13)&15]^Block[(i+8)&15]^Block[(i+2)&15]^Block[i&15],1)) |
| #define | f1(x, y, z) (z^(x&(y^z))) |
| #define | f2(x, y, z) (x^y^z) |
| #define | f3(x, y, z) ((x&y)|(z&(x|y))) |
| #define | f4(x, y, z) (x^y^z) |
| #define | R0(v, w, x, y, z, i) z+=f1(w,x,y)+blk0(i)+0x5A827999+rol(v,5);w=rol(w,30); |
| #define | R1(v, w, x, y, z, i) z+=f1(w,x,y)+blk1(i)+0x5A827999+rol(v,5);w=rol(w,30); |
| #define | R2(v, w, x, y, z, i) z+=f2(w,x,y)+blk1(i)+0x6ED9EBA1+rol(v,5);w=rol(w,30); |
| #define | R3(v, w, x, y, z, i) z+=f3(w,x,y)+blk1(i)+0x8F1BBCDC+rol(v,5);w=rol(w,30); |
| #define | R4(v, w, x, y, z, i) z+=f4(w,x,y)+blk1(i)+0xCA62C1D6+rol(v,5);w=rol(w,30); |
Functions | |
| static void | SHA1Transform (ULONG State[5], UCHAR Buffer[64]) |
| VOID NTAPI | A_SHAInit (PSHA_CTX Context) |
| VOID NTAPI | A_SHAUpdate (PSHA_CTX Context, const unsigned char *Buffer, ULONG BufferSize) |
| VOID NTAPI | A_SHAFinal (PSHA_CTX Context, PULONG Result) |
Macro Definition Documentation
◆ blk0
◆ blk1
◆ DWORD2BE
◆ f1
◆ f2
◆ f3
◆ f4
◆ R0
◆ R1
◆ R2
◆ R3
◆ R4
◆ rol
Function Documentation
◆ A_SHAFinal()
Definition at line 171 of file sha1.c.
172{
176 ULONG BufferContentSize, LengthHi, LengthLo;
177
178 BufferContentSize = Context->Count[1] & 63;
179 if (BufferContentSize >= 56)
180 Pad = 56 + 64 - BufferContentSize;
181 else
182 Pad = 56 - BufferContentSize;
183
185 LengthLo = (Context->Count[1] << 3);
186
188 Buffer[0] = 0x80;
193
196
199}
Definition: bufpool.h:45
VOID NTAPI A_SHAUpdate(PSHA_CTX Context, const unsigned char *Buffer, ULONG BufferSize)
Definition: sha1.c:128
_At_(*)(_In_ PWSK_CLIENT Client, _In_opt_ PUNICODE_STRING NodeName, _In_opt_ PUNICODE_STRING ServiceName, _In_opt_ ULONG NameSpace, _In_opt_ GUID *Provider, _In_opt_ PADDRINFOEXW Hints, _Outptr_ PADDRINFOEXW *Result, _In_opt_ PEPROCESS OwningProcess, _In_opt_ PETHREAD OwningThread, _Inout_ PIRP Irp Result)(Mem)) NTSTATUS(WSKAPI *PFN_WSK_GET_ADDRESS_INFO
Definition: wsk.h:409
Referenced by finalize_hash_impl(), sha_check(), and VerifyInteg().
◆ A_SHAInit()
Definition at line 102 of file sha1.c.
103{
104 /* SHA1 initialization constants */
105 Context->State[0] = 0x67452301;
106 Context->State[1] = 0xEFCDAB89;
107 Context->State[2] = 0x98BADCFE;
108 Context->State[3] = 0x10325476;
109 Context->State[4] = 0xC3D2E1F0;
110 Context->Count[0] =
111 Context->Count[1] = 0;
112}
Referenced by A_SHAFinal(), init_hash_impl(), sha_check(), and VerifyInteg().
◆ A_SHAUpdate()
Definition at line 128 of file sha1.c.
129{
130 ULONG BufferContentSize;
131
132 BufferContentSize = Context->Count[1] & 63;
135 Context->Count[0]++;
137
139 {
141 BufferSize);
142 }
143 else
144 {
146 {
148 64 - BufferContentSize);
149 Buffer += 64 - BufferContentSize;
150 BufferSize -= 64 - BufferContentSize;
152 BufferContentSize = 0;
153 }
155 }
156}
Referenced by A_SHAFinal().
◆ SHA1Transform()
Definition at line 42 of file sha1.c.
43{
45 ULONG *Block;
46
48
49 /* Copy Context->State[] to working variables */
55
56 /* 4 rounds of 20 operations each. Loop unrolled. */
77
78 /* Add the working variables back into Context->State[] */
84
85 /* Wipe variables */
87}
Definition: stack_allocator.h:18
Referenced by A_SHAUpdate().