Configuration options (set of defines) More...
#include "check_config.h"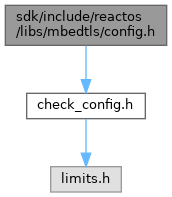
Go to the source code of this file.
Detailed Description
Configuration options (set of defines)
This set of compile-time options may be used to enable or disable features selectively, and reduce the global memory footprint.
Definition in file config.h.
Macro Definition Documentation
◆ MBEDTLS_AES_C
| #define MBEDTLS_AES_C |
Enable the AES block cipher.
Module: library/aes.c Caller: library/cipher.c library/pem.c library/ctr_drbg.c
This module enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_PSK_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_DHE_PSK_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_PSK_WITH_AES_256_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_AES_256_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_PSK_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_DHE_PSK_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_PSK_WITH_AES_128_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_AES_128_CBC_SHA MBEDTLS_TLS_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_RSA_WITH_AES_256_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_RSA_PSK_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_RSA_PSK_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_RSA_PSK_WITH_AES_256_CBC_SHA MBEDTLS_TLS_RSA_PSK_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_RSA_PSK_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_RSA_PSK_WITH_AES_128_CBC_SHA MBEDTLS_TLS_PSK_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_PSK_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_PSK_WITH_AES_256_CBC_SHA MBEDTLS_TLS_PSK_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_PSK_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_PSK_WITH_AES_128_CBC_SHA
PEM_PARSE uses AES for decrypting encrypted keys.
◆ MBEDTLS_AESNI_C
| #define MBEDTLS_AESNI_C /* swyter: looks like these AMD64 improvements are behind an arch macro, better perf is always good */ |
◆ MBEDTLS_ARC4_C
| #define MBEDTLS_ARC4_C |
Enable the ARCFOUR stream cipher.
Module: library/arc4.c Caller: library/cipher.c
This module enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_ECDSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDH_RSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDHE_PSK_WITH_RC4_128_SHA MBEDTLS_TLS_DHE_PSK_WITH_RC4_128_SHA MBEDTLS_TLS_RSA_WITH_RC4_128_SHA MBEDTLS_TLS_RSA_WITH_RC4_128_MD5 MBEDTLS_TLS_RSA_PSK_WITH_RC4_128_SHA MBEDTLS_TLS_PSK_WITH_RC4_128_SHA
- Warning
- ARC4 is considered a weak cipher and its use constitutes a security risk. If possible, we recommend avoidng dependencies on it, and considering stronger ciphers instead.
◆ MBEDTLS_ASN1_PARSE_C
| #define MBEDTLS_ASN1_PARSE_C |
◆ MBEDTLS_ASN1_WRITE_C
| #define MBEDTLS_ASN1_WRITE_C |
◆ MBEDTLS_BIGNUM_C
| #define MBEDTLS_BIGNUM_C |
◆ MBEDTLS_BLOWFISH_C
| #define MBEDTLS_BLOWFISH_C |
◆ MBEDTLS_CAMELLIA_C
| #define MBEDTLS_CAMELLIA_C |
Enable the Camellia block cipher.
Module: library/camellia.c Caller: library/cipher.c
This module enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_PSK_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_DHE_PSK_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_DHE_PSK_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_DHE_PSK_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_PSK_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_CBC_SHA MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_CBC_SHA MBEDTLS_TLS_RSA_PSK_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_RSA_PSK_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_RSA_PSK_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_RSA_PSK_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_PSK_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_PSK_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_PSK_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_PSK_WITH_CAMELLIA_128_CBC_SHA256
◆ MBEDTLS_CCM_C
| #define MBEDTLS_CCM_C |
◆ MBEDTLS_CIPHER_C
| #define MBEDTLS_CIPHER_C |
◆ MBEDTLS_CIPHER_MODE_CBC
| #define MBEDTLS_CIPHER_MODE_CBC |
◆ MBEDTLS_CIPHER_MODE_CFB
| #define MBEDTLS_CIPHER_MODE_CFB |
◆ MBEDTLS_CIPHER_MODE_CTR
| #define MBEDTLS_CIPHER_MODE_CTR |
◆ MBEDTLS_CIPHER_MODE_OFB
| #define MBEDTLS_CIPHER_MODE_OFB |
◆ MBEDTLS_CIPHER_MODE_XTS
| #define MBEDTLS_CIPHER_MODE_XTS |
◆ MBEDTLS_CIPHER_PADDING_ONE_AND_ZEROS
◆ MBEDTLS_CIPHER_PADDING_PKCS7
| #define MBEDTLS_CIPHER_PADDING_PKCS7 |
MBEDTLS_CIPHER_PADDING_XXX: Uncomment or comment macros to add support for specific padding modes in the cipher layer with cipher modes that support padding (e.g. CBC)
If you disable all padding modes, only full blocks can be used with CBC.
Enable padding modes in the cipher layer.
◆ MBEDTLS_CIPHER_PADDING_ZEROS
◆ MBEDTLS_CIPHER_PADDING_ZEROS_AND_LEN
◆ MBEDTLS_CTR_DRBG_C
| #define MBEDTLS_CTR_DRBG_C |
Enable the CTR_DRBG AES-based random generator. The CTR_DRBG generator uses AES-256 by default. To use AES-128 instead, enable MBEDTLS_CTR_DRBG_USE_128_BIT_KEY above.
- Note
- To achieve a 256-bit security strength with CTR_DRBG, you must use AES-256 and use sufficient entropy. See ctr_drbg.h for more details.
Module: library/ctr_drbg.c Caller:
Requires: MBEDTLS_AES_C
This module provides the CTR_DRBG AES random number generator.
◆ MBEDTLS_DES_C
| #define MBEDTLS_DES_C |
Enable the DES block cipher.
Module: library/des.c Caller: library/pem.c library/cipher.c
This module enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_ECDSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDHE_PSK_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_DHE_PSK_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_RSA_PSK_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_PSK_WITH_3DES_EDE_CBC_SHA
PEM_PARSE uses DES/3DES for decrypting encrypted keys.
- Warning
- DES is considered a weak cipher and its use constitutes a security risk. We recommend considering stronger ciphers instead.
◆ MBEDTLS_DHM_C
| #define MBEDTLS_DHM_C |
Enable the Diffie-Hellman-Merkle module.
Module: library/dhm.c Caller: library/ssl_cli.c library/ssl_srv.c
This module is used by the following key exchanges: DHE-RSA, DHE-PSK
- Warning
- Using DHE constitutes a security risk as it is not possible to validate custom DH parameters. If possible, it is recommended users should consider preferring other methods of key exchange. See dhm.h for more details.
◆ MBEDTLS_ECDH_C
| #define MBEDTLS_ECDH_C |
◆ MBEDTLS_ECDSA_C
| #define MBEDTLS_ECDSA_C |
◆ MBEDTLS_ECDSA_DETERMINISTIC
| #define MBEDTLS_ECDSA_DETERMINISTIC |
Enable deterministic ECDSA (RFC 6979). Standard ECDSA is "fragile" in the sense that lack of entropy when signing may result in a compromise of the long-term signing key. This is avoided by the deterministic variant.
Requires: MBEDTLS_HMAC_DRBG_C
Comment this macro to disable deterministic ECDSA.
◆ MBEDTLS_ECP_C
| #define MBEDTLS_ECP_C |
◆ MBEDTLS_ECP_DP_BP256R1_ENABLED
◆ MBEDTLS_ECP_DP_BP384R1_ENABLED
◆ MBEDTLS_ECP_DP_BP512R1_ENABLED
◆ MBEDTLS_ECP_DP_CURVE25519_ENABLED
◆ MBEDTLS_ECP_DP_CURVE448_ENABLED
◆ MBEDTLS_ECP_DP_SECP192K1_ENABLED
◆ MBEDTLS_ECP_DP_SECP192R1_ENABLED
| #define MBEDTLS_ECP_DP_SECP192R1_ENABLED |
◆ MBEDTLS_ECP_DP_SECP224K1_ENABLED
◆ MBEDTLS_ECP_DP_SECP224R1_ENABLED
◆ MBEDTLS_ECP_DP_SECP256K1_ENABLED
◆ MBEDTLS_ECP_DP_SECP256R1_ENABLED
◆ MBEDTLS_ECP_DP_SECP384R1_ENABLED
◆ MBEDTLS_ECP_DP_SECP521R1_ENABLED
◆ MBEDTLS_ECP_NIST_OPTIM
| #define MBEDTLS_ECP_NIST_OPTIM |
◆ MBEDTLS_ENTROPY_C
| #define MBEDTLS_ENTROPY_C |
◆ MBEDTLS_ENTROPY_FORCE_SHA256
| #define MBEDTLS_ENTROPY_FORCE_SHA256 /* swyter: ReactOS is primarily 32-bit only, this speeds it up notably */ |
Force the entropy accumulator to use a SHA-256 accumulator instead of the default SHA-512 based one (if both are available).
Requires: MBEDTLS_SHA256_C
On 32-bit systems SHA-256 can be much faster than SHA-512. Use this option if you have performance concerns.
This option is only useful if both MBEDTLS_SHA256_C and MBEDTLS_SHA512_C are defined. Otherwise the available hash module is used.
◆ MBEDTLS_ERROR_STRERROR_DUMMY
| #define MBEDTLS_ERROR_STRERROR_DUMMY |
Enable a dummy error function to make use of mbedtls_strerror() in third party libraries easier when MBEDTLS_ERROR_C is disabled (no effect when MBEDTLS_ERROR_C is enabled).
You can safely disable this if MBEDTLS_ERROR_C is enabled, or if you're not using mbedtls_strerror() or error_strerror() in your application.
Disable if you run into name conflicts and want to really remove the mbedtls_strerror()
◆ MBEDTLS_GCM_C
| #define MBEDTLS_GCM_C |
◆ MBEDTLS_GENPRIME
| #define MBEDTLS_GENPRIME |
◆ MBEDTLS_HAVE_ASM
| #define MBEDTLS_HAVE_ASM |
◆ MBEDTLS_HMAC_DRBG_C
| #define MBEDTLS_HMAC_DRBG_C |
◆ MBEDTLS_KEY_EXCHANGE_DHE_RSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_DHE_RSA_ENABLED |
Enable the DHE-RSA based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_DHM_C, MBEDTLS_RSA_C, MBEDTLS_PKCS1_V15, MBEDTLS_X509_CRT_PARSE_C
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA MBEDTLS_TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA
- Warning
- Using DHE constitutes a security risk as it is not possible to validate custom DH parameters. If possible, it is recommended users should consider preferring other methods of key exchange. See dhm.h for more details.
◆ MBEDTLS_KEY_EXCHANGE_ECDH_ECDSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_ECDH_ECDSA_ENABLED |
Enable the ECDH-ECDSA based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_ECDH_C, MBEDTLS_X509_CRT_PARSE_C
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_ECDSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDH_ECDSA_WITH_CAMELLIA_256_GCM_SHA384
◆ MBEDTLS_KEY_EXCHANGE_ECDH_RSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_ECDH_RSA_ENABLED |
Enable the ECDH-RSA based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_ECDH_C, MBEDTLS_X509_CRT_PARSE_C
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDH_RSA_WITH_RC4_128_SHA MBEDTLS_TLS_ECDH_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDH_RSA_WITH_CAMELLIA_256_GCM_SHA384
◆ MBEDTLS_KEY_EXCHANGE_ECDHE_ECDSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_ECDHE_ECDSA_ENABLED |
Enable the ECDHE-ECDSA based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_ECDH_C, MBEDTLS_ECDSA_C, MBEDTLS_X509_CRT_PARSE_C,
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_ECDSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDHE_ECDSA_WITH_RC4_128_SHA
◆ MBEDTLS_KEY_EXCHANGE_ECDHE_RSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_ECDHE_RSA_ENABLED |
Enable the ECDHE-RSA based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_ECDH_C, MBEDTLS_RSA_C, MBEDTLS_PKCS1_V15, MBEDTLS_X509_CRT_PARSE_C
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_256_CBC_SHA384 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_ECDHE_RSA_WITH_RC4_128_SHA
◆ MBEDTLS_KEY_EXCHANGE_RSA_ENABLED
| #define MBEDTLS_KEY_EXCHANGE_RSA_ENABLED |
Enable the RSA-only based ciphersuite modes in SSL / TLS.
Requires: MBEDTLS_RSA_C, MBEDTLS_PKCS1_V15, MBEDTLS_X509_CRT_PARSE_C
This enables the following ciphersuites (if other requisites are enabled as well): MBEDTLS_TLS_RSA_WITH_AES_256_GCM_SHA384 MBEDTLS_TLS_RSA_WITH_AES_256_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_AES_256_CBC_SHA MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_GCM_SHA384 MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_256_CBC_SHA MBEDTLS_TLS_RSA_WITH_AES_128_GCM_SHA256 MBEDTLS_TLS_RSA_WITH_AES_128_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_AES_128_CBC_SHA MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_GCM_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_CBC_SHA256 MBEDTLS_TLS_RSA_WITH_CAMELLIA_128_CBC_SHA MBEDTLS_TLS_RSA_WITH_3DES_EDE_CBC_SHA MBEDTLS_TLS_RSA_WITH_RC4_128_SHA MBEDTLS_TLS_RSA_WITH_RC4_128_MD5
◆ MBEDTLS_MD5_C
| #define MBEDTLS_MD5_C |
Enable the MD5 hash algorithm.
Module: library/md5.c Caller: library/md.c library/pem.c library/ssl_tls.c
This module is required for SSL/TLS up to version 1.1, and for TLS 1.2 depending on the handshake parameters. Further, it is used for checking MD5-signed certificates, and for PBKDF1 when decrypting PEM-encoded encrypted keys.
- Warning
- MD5 is considered a weak message digest and its use constitutes a security risk. If possible, we recommend avoiding dependencies on it, and considering stronger message digests instead.
◆ MBEDTLS_MD_C
| #define MBEDTLS_MD_C |
◆ MBEDTLS_OID_C
| #define MBEDTLS_OID_C |
Enable the OID database.
Module: library/oid.c Caller: library/asn1write.c library/pkcs5.c library/pkparse.c library/pkwrite.c library/rsa.c library/x509.c library/x509_create.c library/x509_crl.c library/x509_crt.c library/x509_csr.c library/x509write_crt.c library/x509write_csr.c
This modules translates between OIDs and internal values.
◆ MBEDTLS_PADLOCK_C
| #define MBEDTLS_PADLOCK_C |
◆ MBEDTLS_PK_C
| #define MBEDTLS_PK_C |
◆ MBEDTLS_PK_PARSE_C
| #define MBEDTLS_PK_PARSE_C |
◆ MBEDTLS_PK_PARSE_EC_EXTENDED
| #define MBEDTLS_PK_PARSE_EC_EXTENDED |
Enhance support for reading EC keys using variants of SEC1 not allowed by RFC 5915 and RFC 5480.
Currently this means parsing the SpecifiedECDomain choice of EC parameters (only known groups are supported, not arbitrary domains, to avoid validation issues).
Disable if you only need to support RFC 5915 + 5480 key formats.
◆ MBEDTLS_PK_RSA_ALT_SUPPORT
| #define MBEDTLS_PK_RSA_ALT_SUPPORT |
◆ MBEDTLS_PKCS12_C
| #define MBEDTLS_PKCS12_C |
Enable PKCS#12 PBE functions. Adds algorithms for parsing PKCS#8 encrypted private keys
Module: library/pkcs12.c Caller: library/pkparse.c
Requires: MBEDTLS_ASN1_PARSE_C, MBEDTLS_CIPHER_C, MBEDTLS_MD_C Can use: MBEDTLS_ARC4_C
This module enables PKCS#12 functions.
◆ MBEDTLS_PKCS1_V15
| #define MBEDTLS_PKCS1_V15 |
◆ MBEDTLS_PKCS1_V21
| #define MBEDTLS_PKCS1_V21 |
◆ MBEDTLS_PKCS5_C
| #define MBEDTLS_PKCS5_C |
◆ MBEDTLS_PLATFORM_C
| #define MBEDTLS_PLATFORM_C |
Enable the platform abstraction layer that allows you to re-assign functions like calloc(), free(), snprintf(), printf(), fprintf(), exit().
Enabling MBEDTLS_PLATFORM_C enables to use of MBEDTLS_PLATFORM_XXX_ALT or MBEDTLS_PLATFORM_XXX_MACRO directives, allowing the functions mentioned above to be specified at runtime or compile time respectively.
- Note
- This abstraction layer must be enabled on Windows (including MSYS2) as other module rely on it for a fixed snprintf implementation.
Module: library/platform.c Caller: Most other .c files
This module enables abstraction of common (libc) functions.
◆ MBEDTLS_REMOVE_3DES_CIPHERSUITES
| #define MBEDTLS_REMOVE_3DES_CIPHERSUITES |
Remove 3DES ciphersuites by default in SSL / TLS. This flag removes the ciphersuites based on 3DES from the default list as returned by mbedtls_ssl_list_ciphersuites(). However, it is still possible to enable (some of) them with mbedtls_ssl_conf_ciphersuites() by including them explicitly.
A man-in-the-browser attacker can recover authentication tokens sent through a TLS connection using a 3DES based cipher suite (see "On the Practical (In-)Security of 64-bit Block Ciphers" by Karthikeyan Bhargavan and Gaëtan Leurent, see https://sweet32.info/SWEET32_CCS16.pdf). If this attack falls in your threat model or you are unsure, then you should keep this option enabled to remove 3DES based cipher suites.
Comment this macro to keep 3DES in the default ciphersuite list.
◆ MBEDTLS_REMOVE_ARC4_CIPHERSUITES
| #define MBEDTLS_REMOVE_ARC4_CIPHERSUITES |
Remove RC4 ciphersuites by default in SSL / TLS. This flag removes the ciphersuites based on RC4 from the default list as returned by mbedtls_ssl_list_ciphersuites(). However, it is still possible to enable (some of) them with mbedtls_ssl_conf_ciphersuites() by including them explicitly.
Uncomment this macro to remove RC4 ciphersuites by default.
◆ MBEDTLS_RIPEMD160_C
| #define MBEDTLS_RIPEMD160_C |
◆ MBEDTLS_RSA_C
| #define MBEDTLS_RSA_C |
Enable the RSA public-key cryptosystem.
Module: library/rsa.c library/rsa_internal.c Caller: library/ssl_cli.c library/ssl_srv.c library/ssl_tls.c library/x509.c
This module is used by the following key exchanges: RSA, DHE-RSA, ECDHE-RSA, RSA-PSK
Requires: MBEDTLS_BIGNUM_C, MBEDTLS_OID_C
◆ MBEDTLS_SHA1_C
| #define MBEDTLS_SHA1_C |
Enable the SHA1 cryptographic hash algorithm.
Module: library/sha1.c Caller: library/md.c library/ssl_cli.c library/ssl_srv.c library/ssl_tls.c library/x509write_crt.c
This module is required for SSL/TLS up to version 1.1, for TLS 1.2 depending on the handshake parameters, and for SHA1-signed certificates.
- Warning
- SHA-1 is considered a weak message digest and its use constitutes a security risk. If possible, we recommend avoiding dependencies on it, and considering stronger message digests instead.
◆ MBEDTLS_SHA256_C
| #define MBEDTLS_SHA256_C |
◆ MBEDTLS_SHA512_C
| #define MBEDTLS_SHA512_C |
◆ MBEDTLS_SSL_ALL_ALERT_MESSAGES
| #define MBEDTLS_SSL_ALL_ALERT_MESSAGES |
Enable sending of alert messages in case of encountered errors as per RFC. If you choose not to send the alert messages, mbed TLS can still communicate with other servers, only debugging of failures is harder.
The advantage of not sending alert messages, is that no information is given about reasons for failures thus preventing adversaries of gaining intel.
Enable sending of all alert messages
◆ MBEDTLS_SSL_ALPN
| #define MBEDTLS_SSL_ALPN |
◆ MBEDTLS_SSL_CBC_RECORD_SPLITTING
| #define MBEDTLS_SSL_CBC_RECORD_SPLITTING |
◆ MBEDTLS_SSL_CLI_C
| #define MBEDTLS_SSL_CLI_C |
◆ MBEDTLS_SSL_ENCRYPT_THEN_MAC
| #define MBEDTLS_SSL_ENCRYPT_THEN_MAC |
Enable support for Encrypt-then-MAC, RFC 7366.
This allows peers that both support it to use a more robust protection for ciphersuites using CBC, providing deep resistance against timing attacks on the padding or underlying cipher.
This only affects CBC ciphersuites, and is useless if none is defined.
Requires: MBEDTLS_SSL_PROTO_TLS1 or MBEDTLS_SSL_PROTO_TLS1_1 or MBEDTLS_SSL_PROTO_TLS1_2
Comment this macro to disable support for Encrypt-then-MAC
◆ MBEDTLS_SSL_EXTENDED_MASTER_SECRET
| #define MBEDTLS_SSL_EXTENDED_MASTER_SECRET |
Enable support for Extended Master Secret, aka Session Hash (draft-ietf-tls-session-hash-02).
This was introduced as "the proper fix" to the Triple Handshake familiy of attacks, but it is recommended to always use it (even if you disable renegotiation), since it actually fixes a more fundamental issue in the original SSL/TLS design, and has implications beyond Triple Handshake.
Requires: MBEDTLS_SSL_PROTO_TLS1 or MBEDTLS_SSL_PROTO_TLS1_1 or MBEDTLS_SSL_PROTO_TLS1_2
Comment this macro to disable support for Extended Master Secret.
◆ MBEDTLS_SSL_MAX_FRAGMENT_LENGTH
| #define MBEDTLS_SSL_MAX_FRAGMENT_LENGTH |
◆ MBEDTLS_SSL_PROTO_TLS1
| #define MBEDTLS_SSL_PROTO_TLS1 |
◆ MBEDTLS_SSL_PROTO_TLS1_1
| #define MBEDTLS_SSL_PROTO_TLS1_1 |
◆ MBEDTLS_SSL_PROTO_TLS1_2
| #define MBEDTLS_SSL_PROTO_TLS1_2 |
◆ MBEDTLS_SSL_RENEGOTIATION
| #define MBEDTLS_SSL_RENEGOTIATION |
Enable support for TLS renegotiation.
The two main uses of renegotiation are (1) refresh keys on long-lived connections and (2) client authentication after the initial handshake. If you don't need renegotiation, it's probably better to disable it, since it has been associated with security issues in the past and is easy to misuse/misunderstand.
Comment this to disable support for renegotiation.
- Note
- Even if this option is disabled, both client and server are aware of the Renegotiation Indication Extension (RFC 5746) used to prevent the SSL renegotiation attack (see RFC 5746 Sect. 1). (See
mbedtls_ssl_conf_legacy_renegotiationfor the configuration of this extension).
◆ MBEDTLS_SSL_SERVER_NAME_INDICATION
| #define MBEDTLS_SSL_SERVER_NAME_INDICATION |
◆ MBEDTLS_SSL_SESSION_TICKETS
| #define MBEDTLS_SSL_SESSION_TICKETS |
Enable support for RFC 5077 session tickets in SSL. Client-side, provides full support for session tickets (maintenance of a session store remains the responsibility of the application, though). Server-side, you also need to provide callbacks for writing and parsing tickets, including authenticated encryption and key management. Example callbacks are provided by MBEDTLS_SSL_TICKET_C.
Comment this macro to disable support for SSL session tickets
◆ MBEDTLS_SSL_TICKET_C
| #define MBEDTLS_SSL_TICKET_C |
◆ MBEDTLS_SSL_TLS_C
| #define MBEDTLS_SSL_TLS_C |
◆ MBEDTLS_SSL_TRUNCATED_HMAC
| #define MBEDTLS_SSL_TRUNCATED_HMAC |
◆ MBEDTLS_TIMING_C
| #define MBEDTLS_TIMING_C |
Enable the semi-portable timing interface.
- Note
- The provided implementation only works on POSIX/Unix (including Linux, BSD and OS X) and Windows. On other platforms, you can either disable that module and provide your own implementations of the callbacks needed by
mbedtls_ssl_set_timer_cb()for DTLS, or leave it enabled and provide your own implementation of the whole module by settingMBEDTLS_TIMING_ALTin the current file. - See also our Knowledge Base article about porting to a new environment: https://tls.mbed.org/kb/how-to/how-do-i-port-mbed-tls-to-a-new-environment-OS
Module: library/timing.c Caller: library/havege.c
This module is used by the HAVEGE random number generator.
◆ MBEDTLS_TLS_DEFAULT_ALLOW_SHA1_IN_KEY_EXCHANGE
| #define MBEDTLS_TLS_DEFAULT_ALLOW_SHA1_IN_KEY_EXCHANGE |
Complete list of ciphersuites to use, in order of preference.
- Warning
- No dependency checking is done on that field! This option can only be used to restrict the set of available ciphersuites. It is your responsibility to make sure the needed modules are active.
Use this to save a few hundred bytes of ROM (default ordering of all available ciphersuites) and a few to a few hundred bytes of RAM.
The value below is only an example, not the default. Allow SHA-1 in the default TLS configuration for certificate signing. Without this build-time option, SHA-1 support must be activated explicitly through mbedtls_ssl_conf_cert_profile. Turning on this option is not recommended because of it is possible to generate SHA-1 collisions, however this may be safe for legacy infrastructure where additional controls apply.
- Warning
- SHA-1 is considered a weak message digest and its use constitutes a security risk. If possible, we recommend avoiding dependencies on it, and considering stronger message digests instead. Allow SHA-1 in the default TLS configuration for TLS 1.2 handshake signature and ciphersuite selection. Without this build-time option, SHA-1 support must be activated explicitly through mbedtls_ssl_conf_sig_hashes. The use of SHA-1 in TLS <= 1.1 and in HMAC-SHA-1 is always allowed by default. At the time of writing, there is no practical attack on the use of SHA-1 in handshake signatures, hence this option is turned on by default to preserve compatibility with existing peers, but the general warning applies nonetheless:
- SHA-1 is considered a weak message digest and its use constitutes a security risk. If possible, we recommend avoiding dependencies on it, and considering stronger message digests instead.
◆ MBEDTLS_X509_CHECK_EXTENDED_KEY_USAGE
| #define MBEDTLS_X509_CHECK_EXTENDED_KEY_USAGE |
Enable verification of the extendedKeyUsage extension (leaf certificates).
Disabling this avoids problems with mis-issued and/or misused certificates.
- Warning
- Depending on your PKI use, disabling this can be a security risk!
Comment to skip extendedKeyUsage checking for certificates.
◆ MBEDTLS_X509_CHECK_KEY_USAGE
| #define MBEDTLS_X509_CHECK_KEY_USAGE |
Enable verification of the keyUsage extension (CA and leaf certificates).
Disabling this avoids problems with mis-issued and/or misused (intermediate) CA and leaf certificates.
- Warning
- Depending on your PKI use, disabling this can be a security risk!
Comment to skip keyUsage checking for both CA and leaf certificates.
◆ MBEDTLS_X509_CRT_PARSE_C
| #define MBEDTLS_X509_CRT_PARSE_C |
◆ MBEDTLS_X509_RSASSA_PSS_SUPPORT
| #define MBEDTLS_X509_RSASSA_PSS_SUPPORT |
◆ MBEDTLS_X509_USE_C
| #define MBEDTLS_X509_USE_C |
Enable X.509 core for using certificates.
Module: library/x509.c Caller: library/x509_crl.c library/x509_crt.c library/x509_csr.c
Requires: MBEDTLS_ASN1_PARSE_C, MBEDTLS_BIGNUM_C, MBEDTLS_OID_C, MBEDTLS_PK_PARSE_C
This module is required for the X.509 parsing modules.