#include <stdarg.h>#include <stdio.h>#include <windef.h>#include <winbase.h>#include <sspi.h>#include "wine/test.h"
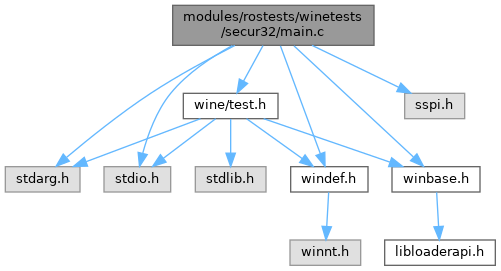
Include dependency graph for main.c:
Go to the source code of this file.
Macros | |
| #define | SECURITY_WIN32 |
| #define | _SEC_ERR(x) case (x): return #x; |
| #define | X(flag) |
Functions | |
| static | PSecurityFunctionTableA (SEC_ENTRY *pInitSecurityInterfaceA)(void) |
| static | SECURITY_STATUS (SEC_ENTRY *pEnumerateSecurityPackagesA)(PULONG |
| static void | InitFunctionPtrs (void) |
| static const char * | getSecError (SECURITY_STATUS status) |
| static SECURITY_STATUS | setupPackageA (SEC_CHAR *p_package_name, PSecPkgInfoA *p_pkg_info) |
| static void | testInitSecurityInterface (void) |
| static void | testEnumerateSecurityPackages (void) |
| static void | testQuerySecurityPackageInfo (void) |
| START_TEST (main) | |
Variables | |
| static HMODULE | secdll |
| static PSecPkgInfoA *static SEC_CHAR | ULONG |
| static PSecPkgInfoA *static SEC_CHAR | PLUID |
| static PSecPkgInfoA *static SEC_CHAR | PVOID |
| static PSecPkgInfoA *static SEC_CHAR | SEC_GET_KEY_FN |
| static PSecPkgInfoA *static SEC_CHAR | PCredHandle |
| static PSecPkgInfoA *static SEC_CHAR | PTimeStamp |
| static | PCtxtHandle |
| static SEC_CHAR | PSecBufferDesc |
| static SEC_CHAR | PULONG |
Macro Definition Documentation
◆ _SEC_ERR
◆ SECURITY_WIN32
◆ X
Value:
GLsizei GLenum const GLvoid GLsizei GLenum GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLint GLint GLint GLshort GLshort GLshort GLubyte GLubyte GLubyte GLuint GLuint GLuint GLushort GLushort GLushort GLbyte GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLfloat GLint GLint GLint GLint GLshort GLshort GLshort GLshort GLubyte GLubyte GLubyte GLubyte GLuint GLuint GLuint GLuint GLushort GLushort GLushort GLushort GLboolean flag
Definition: glfuncs.h:52
GLsizei GLenum const GLvoid GLsizei GLenum GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLint GLint GLint GLshort GLshort GLshort GLubyte GLubyte GLubyte GLuint GLuint GLuint GLushort GLushort GLushort GLbyte GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLfloat GLint GLint GLint GLint GLshort GLshort GLshort GLshort GLubyte GLubyte GLubyte GLubyte GLuint GLuint GLuint GLuint GLushort GLushort GLushort GLushort GLboolean const GLdouble const GLfloat const GLint const GLshort const GLbyte const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLdouble const GLfloat const GLfloat const GLint const GLint const GLshort const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort GLenum GLenum GLenum GLfloat GLenum GLint GLenum GLenum GLenum GLfloat GLenum GLenum GLint GLenum GLfloat GLenum GLint GLint GLushort GLenum GLenum GLfloat GLenum GLenum GLint GLfloat const GLubyte GLenum GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLint GLint GLsizei GLsizei GLint GLenum GLenum const GLvoid GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLenum const GLdouble GLenum GLenum const GLfloat GLenum GLenum const GLint GLsizei GLuint GLfloat GLuint GLbitfield GLfloat GLint GLuint GLboolean GLenum GLfloat GLenum GLbitfield GLenum GLfloat GLfloat GLint GLint const GLfloat GLenum GLfloat GLfloat GLint GLint GLfloat GLfloat GLint GLint const GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat const GLdouble const GLfloat const GLdouble const GLfloat GLint i
Definition: glfuncs.h:248
Function Documentation
◆ getSecError()
|
static |
Definition at line 74 of file main.c.
75{
77
78#define _SEC_ERR(x) case (x): return #x;
80 {
100 default:
103 }
104#undef _SEC_ERR
105}
#define _SEC_ERR(x)
Referenced by testQuerySecurityPackageInfo().
◆ InitFunctionPtrs()
Definition at line 50 of file main.c.
51{
56 {
68 }
69}
HINSTANCE WINAPI DECLSPEC_HOTPATCH LoadLibraryA(LPCSTR lpLibFileName)
Definition: loader.c:111
static QUERY_CONTEXT_ATTRIBUTES_FN_A pQueryContextAttributesA
Definition: schannel.c:32
Referenced by START_TEST().
◆ PSecurityFunctionTableA()
|
static |
◆ SECURITY_STATUS()
|
static |
◆ setupPackageA()
|
static |
Definition at line 110 of file main.c.
Referenced by testQuerySecurityPackageInfo().
◆ START_TEST()
| START_TEST | ( | main | ) |
Definition at line 247 of file main.c.
248{
249 InitFunctionPtrs();
250 if(pInitSecurityInterfaceA)
251 testInitSecurityInterface();
252 if(pFreeContextBuffer)
253 {
254 if(pEnumerateSecurityPackagesA)
256 if(pQuerySecurityPackageInfoA)
257 {
258 testQuerySecurityPackageInfo();
259 }
260 }
263}
◆ testEnumerateSecurityPackages()
Definition at line 131 of file main.c.
132{
133
134 SECURITY_STATUS sec_status;
137
139
140 sec_status = pEnumerateSecurityPackagesA(&num_packages, &pkg_info);
141
143 "EnumerateSecurityPackages() should return %d, not %08x\n",
144 SEC_E_OK, sec_status);
145
146 if (num_packages == 0)
147 {
148 todo_wine
150 num_packages);
152 return;
153 }
154 else
156 num_packages);
157
159 "pkg_info should not be NULL after EnumerateSecurityPackages\n");
160
165#define X(flag) \
166 if(pkg_info[i].fCapabilities & flag) \
167 trace("\t" #flag "\n")
168
193#undef X
196 }
197
198 pFreeContextBuffer(pkg_info);
199}
#define X(x)
#define SECPKG_FLAG_APPCONTAINER_PASSTHROUGH
Definition: sspi.h:148
Definition: sspi.h:103
Referenced by START_TEST().
◆ testInitSecurityInterface()
Definition at line 122 of file main.c.
Referenced by START_TEST().
◆ testQuerySecurityPackageInfo()
Definition at line 202 of file main.c.
203{
204 SECURITY_STATUS sec_status;
205 PSecPkgInfoA pkg_info;
208
210
211 /* Test with an existing package. Test should pass */
212
213 pkg_info = (void *)0xdeadbeef;
214 sec_status = setupPackageA(ntlm, &pkg_info);
215
218 "Return value of QuerySecurityPackageInfo() shouldn't be %s\n",
219 getSecError(sec_status) );
220
222 {
225 /* there is no point in testing pkg_info->cbMaxToken since it varies
226 * between implementations.
227 */
228
229 sec_status = pFreeContextBuffer(pkg_info);
231 "Return value of FreeContextBuffer() shouldn't be %s\n",
232 getSecError(sec_status) );
233 }
234
235 /* Test with a nonexistent package, test should fail */
236
237 pkg_info = (void *)0xdeadbeef;
238 sec_status = pQuerySecurityPackageInfoA(winetest, &pkg_info);
239
241 "Return value of QuerySecurityPackageInfo() should be %s for a nonexistent package\n",
243
245}
static SECURITY_STATUS setupPackageA(SEC_CHAR *p_package_name, PSecPkgInfoA *p_pkg_info)
Definition: main.c:110
Referenced by START_TEST().
Variable Documentation
◆ PCredHandle
| PSecPkgInfoA *static SEC_CHAR PCredHandle |
◆ PCtxtHandle
◆ PLUID
| PSecPkgInfoA *static SEC_CHAR PLUID |
◆ PSecBufferDesc
◆ PTimeStamp
◆ PULONG
◆ PVOID
◆ SEC_GET_KEY_FN
| PSecPkgInfoA *static SEC_CHAR SEC_GET_KEY_FN |
◆ secdll
|
static |
Definition at line 32 of file main.c.
Referenced by InitFunctionPtrs(), and START_TEST().