#include "ksecdd.h"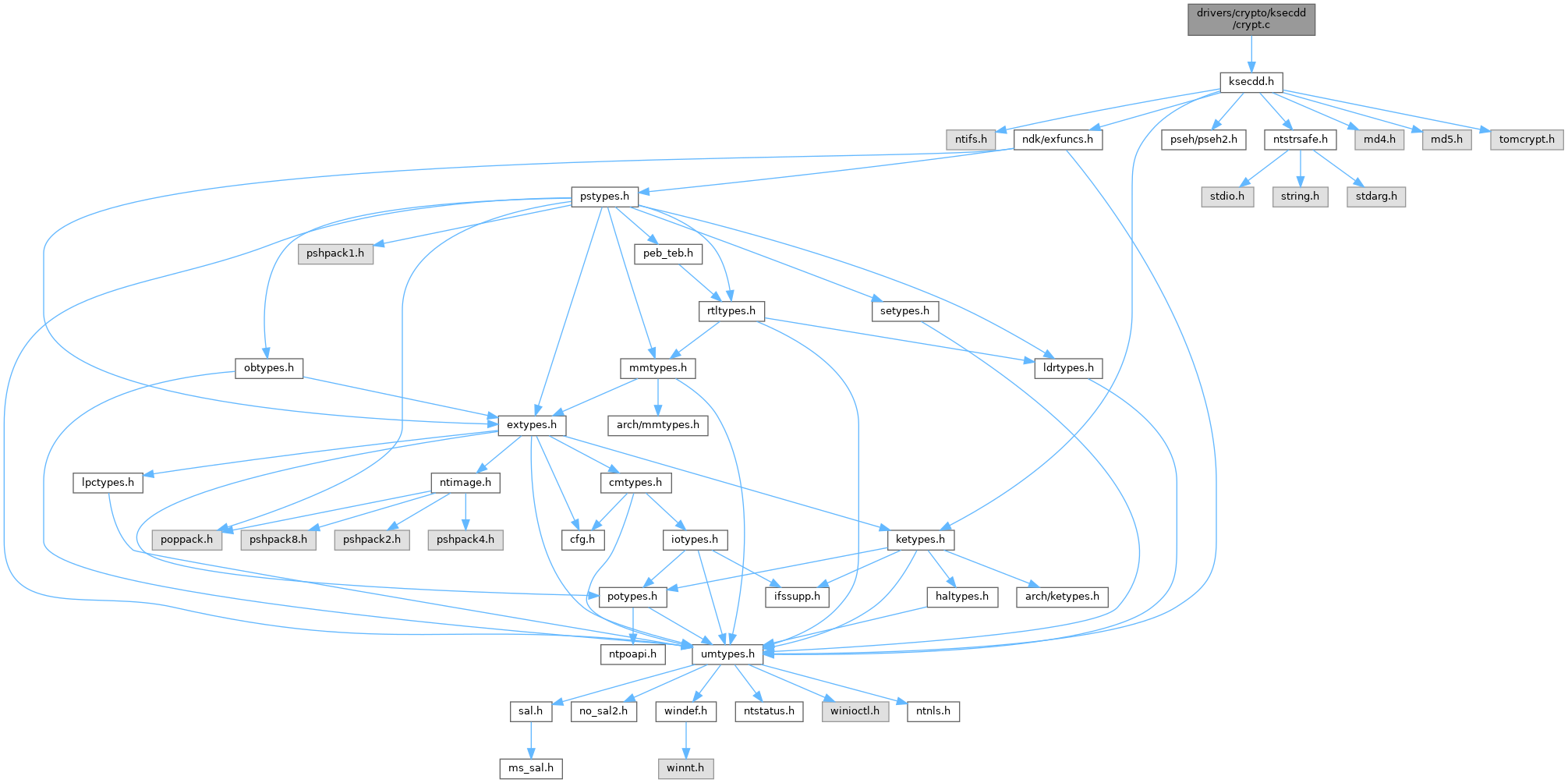
Go to the source code of this file.
Classes | |
| struct | _KSEC_PROCESS_DATA |
| struct | _KSEC_LOGON_DATA |
Typedefs | |
| typedef struct _KSEC_PROCESS_DATA | KSEC_PROCESS_DATA |
| typedef struct _KSEC_PROCESS_DATA * | PKSEC_PROCESS_DATA |
| typedef struct _KSEC_LOGON_DATA | KSEC_LOGON_DATA |
| typedef struct _KSEC_LOGON_DATA * | PKSEC_LOGON_DATA |
Functions | |
| VOID NTAPI | KsecInitializeEncryptionSupport (VOID) |
| static VOID | KsecGetKeyData (_Out_ UCHAR KeyData[32], _In_ ULONG OptionFlags) |
| static VOID | KsecGetDes3Key (_Out_ PDES3_KEY Des3Key, _In_ ULONG OptionFlags) |
| static VOID | KsecGetAesKey (_Out_ PAES_KEY AesKey, _In_ ULONG OptionFlags) |
| static VOID | KsecEncryptMemoryDes3 (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
| static VOID | KsecDecryptMemoryDes3 (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
| static VOID | KsecEncryptMemoryAes (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
| static VOID | KsecDecryptMemoryAes (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
| NTSTATUS NTAPI | KsecEncryptMemory (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
| NTSTATUS NTAPI | KsecDecryptMemory (_Inout_ PVOID Buffer, _In_ ULONG Length, _In_ ULONG OptionFlags) |
Variables | |
| MD5_CTX | KsecLoadTimeStartMd5s [2] |
| DES3_KEY | KsecGlobalDes3Key |
| AES_KEY | KsecGlobalAesKey |
Typedef Documentation
◆ KSEC_LOGON_DATA
| typedef struct _KSEC_LOGON_DATA KSEC_LOGON_DATA |
◆ KSEC_PROCESS_DATA
◆ PKSEC_LOGON_DATA
| typedef struct _KSEC_LOGON_DATA * PKSEC_LOGON_DATA |
◆ PKSEC_PROCESS_DATA
| typedef struct _KSEC_PROCESS_DATA * PKSEC_PROCESS_DATA |
Function Documentation
◆ KsecDecryptMemory()
| NTSTATUS NTAPI KsecDecryptMemory | ( | _Inout_ PVOID | Buffer, |
| _In_ ULONG | Length, | ||
| _In_ ULONG | OptionFlags | ||
| ) |
Definition at line 327 of file crypt.c.
Referenced by KsecDeviceControl().
◆ KsecDecryptMemoryAes()
|
static |
Definition at line 266 of file crypt.c.
Referenced by KsecDecryptMemory().
◆ KsecDecryptMemoryDes3()
|
static |
Definition at line 214 of file crypt.c.
Referenced by KsecDecryptMemory().
◆ KsecEncryptMemory()
| NTSTATUS NTAPI KsecEncryptMemory | ( | _Inout_ PVOID | Buffer, |
| _In_ ULONG | Length, | ||
| _In_ ULONG | OptionFlags | ||
| ) |
Definition at line 292 of file crypt.c.
Referenced by KsecDeviceControl().
◆ KsecEncryptMemoryAes()
|
static |
Definition at line 240 of file crypt.c.
Referenced by KsecEncryptMemory().
◆ KsecEncryptMemoryDes3()
|
static |
Definition at line 188 of file crypt.c.
Referenced by KsecEncryptMemory().
◆ KsecGetAesKey()
Definition at line 163 of file crypt.c.
Referenced by KsecDecryptMemoryAes(), and KsecEncryptMemoryAes().
◆ KsecGetDes3Key()
Definition at line 138 of file crypt.c.
Referenced by KsecDecryptMemoryDes3(), and KsecEncryptMemoryDes3().
◆ KsecGetKeyData()
Definition at line 75 of file crypt.c.
Referenced by KsecGetAesKey(), and KsecGetDes3Key().
◆ KsecInitializeEncryptionSupport()
Definition at line 43 of file crypt.c.
Referenced by DriverEntry().
Variable Documentation
◆ KsecGlobalAesKey
| AES_KEY KsecGlobalAesKey |
Definition at line 14 of file crypt.c.
Referenced by KsecGetAesKey(), and KsecInitializeEncryptionSupport().
◆ KsecGlobalDes3Key
| DES3_KEY KsecGlobalDes3Key |
Definition at line 13 of file crypt.c.
Referenced by KsecGetDes3Key(), and KsecInitializeEncryptionSupport().
◆ KsecLoadTimeStartMd5s
| MD5_CTX KsecLoadTimeStartMd5s[2] |
Definition at line 12 of file crypt.c.
Referenced by KsecGetKeyData(), and KsecInitializeEncryptionSupport().