SeHelpers.c File Reference
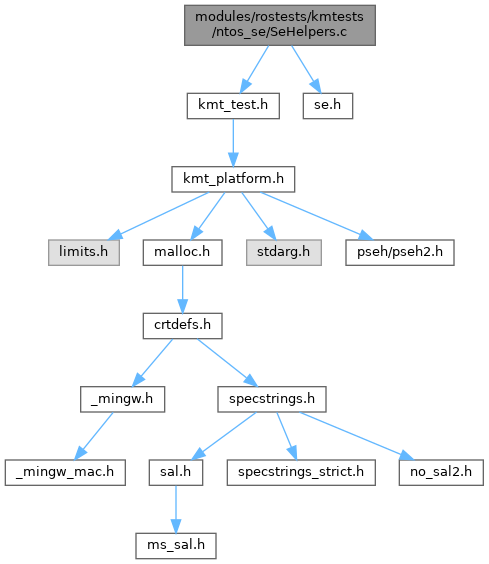
Include dependency graph for SeHelpers.c:
Go to the source code of this file.
Functions | |
| NTSTATUS | RtlxAddAuditAccessAceEx (_Inout_ PACL Acl, _In_ ULONG Revision, _In_ ULONG Flags, _In_ ACCESS_MASK AccessMask, _In_ PSID Sid, _In_ BOOLEAN Success, _In_ BOOLEAN Failure) |
| NTSTATUS | RtlxAddMandatoryLabelAceEx (_Inout_ PACL Acl, _In_ ULONG Revision, _In_ ULONG Flags, _In_ ACCESS_MASK AccessMask, _In_ PSID Sid) |
| VOID | CheckSid__ (_In_ PSID Sid, _In_ ULONG SidSize, _In_ PISID ExpectedSid, _In_ PCSTR FileAndLine) |
| VOID | VCheckAcl__ (_In_ PACL Acl, _In_ ULONG AceCount, _In_ PCSTR FileAndLine, _In_ va_list Arguments) |
| VOID | CheckAcl__ (_In_ PACL Acl, _In_ ULONG AceCount, _In_ PCSTR FileAndLine,...) |
Function Documentation
◆ CheckAcl__()
Definition at line 219 of file SeHelpers.c.
224{
225 va_list Arguments;
226
227 va_start(Arguments, FileAndLine);
228 VCheckAcl__(Acl, AceCount, FileAndLine, Arguments);
229 va_end(Arguments);
230}
VOID VCheckAcl__(_In_ PACL Acl, _In_ ULONG AceCount, _In_ PCSTR FileAndLine, _In_ va_list Arguments)
Definition: SeHelpers.c:128
◆ CheckSid__()
| VOID CheckSid__ | ( | _In_ PSID | Sid, |
| _In_ ULONG | SidSize, | ||
| _In_ PISID | ExpectedSid, | ||
| _In_ PCSTR | FileAndLine | ||
| ) |
Definition at line 89 of file SeHelpers.c.
94{
95 BOOLEAN Okay;
97
100 return;
102 return;
106 return;
107
111 return;
114 if (!Okay)
115 {
116 WCHAR Buffer1[128];
117 WCHAR Buffer2[128];
118 UNICODE_STRING SidString1, SidString2;
119 RtlInitEmptyUnicodeString(&SidString1, Buffer1, sizeof(Buffer1));
120 RtlInitEmptyUnicodeString(&SidString2, Buffer2, sizeof(Buffer2));
124 }
125}
Definition: nsiface.idl:2307
BOOLEAN BOOLEAN KmtOk(INT Condition, PCSTR FileAndLine, PCSTR Format,...) KMT_FORMAT(ms_printf
BOOLEAN BOOLEAN VOID VOID BOOLEAN BOOLEAN KmtSkip(INT Condition, PCSTR FileAndLine, PCSTR Format,...) KMT_FORMAT(ms_printf
NTSYSAPI BOOLEAN NTAPI RtlEqualSid(_In_ PSID Sid1, _In_ PSID Sid2)
NTSYSAPI NTSTATUS NTAPI RtlConvertSidToUnicodeString(OUT PUNICODE_STRING DestinationString, IN PVOID Sid, IN BOOLEAN AllocateDestinationString)
Definition: env_spec_w32.h:368
Referenced by CheckDirectorySecurity__(), and VCheckAcl__().
◆ RtlxAddAuditAccessAceEx()
| NTSTATUS RtlxAddAuditAccessAceEx | ( | _Inout_ PACL | Acl, |
| _In_ ULONG | Revision, | ||
| _In_ ULONG | Flags, | ||
| _In_ ACCESS_MASK | AccessMask, | ||
| _In_ PSID | Sid, | ||
| _In_ BOOLEAN | Success, | ||
| _In_ BOOLEAN | Failure | ||
| ) |
Definition at line 12 of file SeHelpers.c.
20{
22 USHORT AceSize;
24
27
34 Ace->Header.AceSize = AceSize;
38 Sid);
41 {
43 Revision,
44 MAXULONG,
45 Ace,
46 AceSize);
47 }
50}
NTSYSAPI NTSTATUS NTAPI RtlAddAce(_Inout_ PACL Acl, _In_ ULONG AceRevision, _In_ ULONG StartingAceIndex, _In_reads_bytes_(AceListLength) PVOID AceList, _In_ ULONG AceListLength)
Definition: ms-dtyp.idl:198
Definition: ms-dtyp.idl:266
NTSYSAPI BOOLEAN WINAPI RtlCopySid(DWORD, PSID, PSID)
Referenced by TestSeAssignSecurity().
◆ RtlxAddMandatoryLabelAceEx()
| NTSTATUS RtlxAddMandatoryLabelAceEx | ( | _Inout_ PACL | Acl, |
| _In_ ULONG | Revision, | ||
| _In_ ULONG | Flags, | ||
| _In_ ACCESS_MASK | AccessMask, | ||
| _In_ PSID | Sid | ||
| ) |
Definition at line 53 of file SeHelpers.c.
59{
61 USHORT AceSize;
63
70 Ace->Header.AceSize = AceSize;
74 Sid);
77 {
79 Revision,
80 MAXULONG,
81 Ace,
82 AceSize);
83 }
86}
Definition: ms-dtyp.idl:278
Referenced by TestSeAssignSecurity().
◆ VCheckAcl__()
| VOID VCheckAcl__ | ( | _In_ PACL | Acl, |
| _In_ ULONG | AceCount, | ||
| _In_ PCSTR | FileAndLine, | ||
| _In_ va_list | Arguments | ||
| ) |
Definition at line 128 of file SeHelpers.c.
133{
136 PACE_HEADER AceHeader;
141 PACCESS_ALLOWED_ACE AllowedAce;
142 PACCESS_DENIED_ACE DeniedAce;
143 PSYSTEM_AUDIT_ACE AuditAce;
144
147 return;
153 KmtOk(Acl->AceCount == AceCount, FileAndLine, "AceCount is %u, expected %lu\n", Acl->AceCount, AceCount);
156 {
157 KmtOk(Acl->AclSize >= Offset + sizeof(*AceHeader), FileAndLine, "AclSize too small (%u) at Offset %lu, ACE #%lu\n", Acl->AclSize, Offset, i);
159 break;
161 KmtOk((ULONG_PTR)AceHeader % sizeof(ULONG) == 0, FileAndLine, "[%lu] Unaligned ACE %p\n", i, AceHeader);
162 KmtOk(AceHeader->AceSize % sizeof(ULONG) == 0, FileAndLine, "[%lu] Unaligned ACE size %u\n", i, AceHeader->AceSize);
163 KmtOk(Acl->AclSize >= Offset + AceHeader->AceSize, FileAndLine, "[%lu] AclSize too small (%u) at Offset %lu\n", i, Acl->AclSize, Offset);
165 break;
168 continue;
171 KmtOk(AceHeader->AceType == AceType, FileAndLine, "[%lu] AceType is %u, expected %u\n", i, AceHeader->AceType, AceType);
172 KmtOk(AceHeader->AceFlags == AceFlags, FileAndLine, "[%lu] AceFlags is 0x%x, expected 0x%x\n", i, AceHeader->AceFlags, AceFlags);
174 {
177 KmtOk(AceHeader->AceSize >= sizeof(*AllowedAce), FileAndLine, "[%lu] AllowedAce AceSize too small: %u\n", i, AceHeader->AceSize);
179 continue;
180 AllowedAce = (PACCESS_ALLOWED_ACE)AceHeader;
181 KmtOk(AllowedAce->Mask == Mask, FileAndLine, "[%lu] AllowedAce Mask is 0x%lx, expected 0x%lx\n", i, AllowedAce->Mask, Mask);
184 Sid,
185 FileAndLine);
186 }
188 {
191 KmtOk(AceHeader->AceSize >= sizeof(*DeniedAce), FileAndLine, "[%lu] DeniedAce AceSize too small: %u\n", i, AceHeader->AceSize);
193 continue;
194 DeniedAce = (PACCESS_DENIED_ACE)AceHeader;
195 KmtOk(DeniedAce->Mask == Mask, FileAndLine, "[%lu] DeniedAce Mask is 0x%lx, expected 0x%lx\n", i, DeniedAce->Mask, Mask);
198 Sid,
199 FileAndLine);
200 }
202 {
205 KmtOk(AceHeader->AceSize >= sizeof(*AuditAce), FileAndLine, "[%lu] AuditAce AceSize too small: %u\n", i, AceHeader->AceSize);
207 continue;
208 AuditAce = (PSYSTEM_AUDIT_ACE)AceHeader;
209 KmtOk(AuditAce->Mask == Mask, FileAndLine, "[%lu] AuditAce Mask is 0x%lx, expected 0x%lx\n", i, AuditAce->Mask, Mask);
212 Sid,
213 FileAndLine);
214 }
215 }
216}
VOID CheckSid__(_In_ PSID Sid, _In_ ULONG SidSize, _In_ PISID ExpectedSid, _In_ PCSTR FileAndLine)
Definition: SeHelpers.c:89
GLsizei GLenum const GLvoid GLsizei GLenum GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLint GLint GLint GLshort GLshort GLshort GLubyte GLubyte GLubyte GLuint GLuint GLuint GLushort GLushort GLushort GLbyte GLbyte GLbyte GLbyte GLdouble GLdouble GLdouble GLdouble GLfloat GLfloat GLfloat GLfloat GLint GLint GLint GLint GLshort GLshort GLshort GLshort GLubyte GLubyte GLubyte GLubyte GLuint GLuint GLuint GLuint GLushort GLushort GLushort GLushort GLboolean const GLdouble const GLfloat const GLint const GLshort const GLbyte const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLdouble const GLfloat const GLfloat const GLint const GLint const GLshort const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort const GLdouble const GLfloat const GLint const GLshort GLenum GLenum GLenum GLfloat GLenum GLint GLenum GLenum GLenum GLfloat GLenum GLenum GLint GLenum GLfloat GLenum GLint GLint GLushort GLenum GLenum GLfloat GLenum GLenum GLint GLfloat const GLubyte GLenum GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLint GLint GLsizei GLsizei GLint GLenum GLenum const GLvoid GLenum GLenum const GLfloat GLenum GLenum const GLint GLenum GLenum const GLdouble GLenum GLenum const GLfloat GLenum GLenum const GLint GLsizei GLuint GLfloat GLuint GLbitfield GLfloat GLint GLuint GLboolean GLenum GLfloat GLenum GLbitfield GLenum GLfloat GLfloat GLint GLint const GLfloat GLenum GLfloat GLfloat GLint GLint GLfloat GLfloat GLint GLint const GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat GLint GLfloat GLfloat const GLdouble const GLfloat const GLdouble const GLfloat GLint i
Definition: glfuncs.h:248
struct _SYSTEM_AUDIT_ACE * PSYSTEM_AUDIT_ACE
struct _ACCESS_DENIED_ACE * PACCESS_DENIED_ACE
struct _ACE_HEADER * PACE_HEADER
struct _ACCESS_ALLOWED_ACE * PACCESS_ALLOWED_ACE
Definition: ms-dtyp.idl:215
Definition: ms-dtyp.idl:230
Definition: ms-dtyp.idl:209
Referenced by CheckAcl__(), CheckDirectorySecurity__(), and CheckKeySecurity__().