RtlRemovePrivileges.c File Reference
#include "precomp.h"
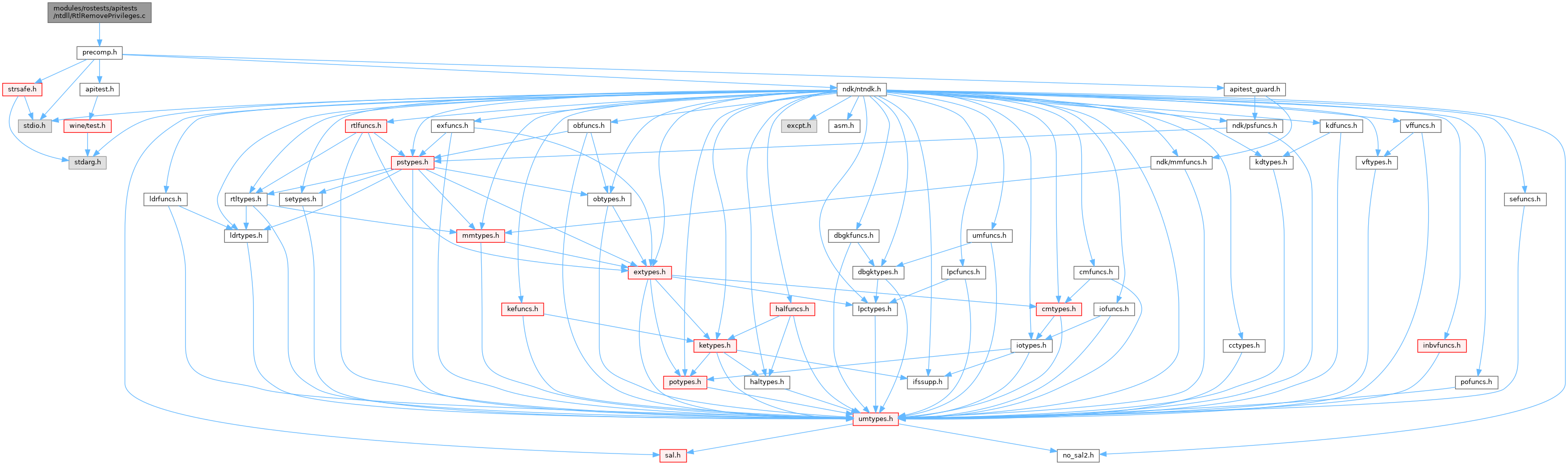
Include dependency graph for RtlRemovePrivileges.c:
Go to the source code of this file.
Functions | |
| START_TEST (RtlRemovePrivileges) | |
Function Documentation
◆ START_TEST()
| START_TEST | ( | RtlRemovePrivileges | ) |
Definition at line 10 of file RtlRemovePrivileges.c.
11{
12#if (NTDDI_VERSION >= NTDDI_VISTA)
20 ULONG PrivilegesToKeep[2];
21
22 /* Duplicate current process token to run this test */
25 {
26 ok(0, "Failed to open current process token with TOKEN_DUPLICATE access (Status code %lx)!\n", Status);
27 return;
28 }
29
30 Status = NtDuplicateToken(TokenHandle, TOKEN_ALL_ACCESS, NULL, FALSE, TokenPrimary, &TestTokenHandle);
33 {
35 return;
36 }
37
38 /* Retrieve token privileges, we need at least 3 privileges to run following tests */
39 Status = NtQueryInformationToken(TestTokenHandle, TokenPrivileges, Buffer, sizeof(Buffer), &ReturnLength);
41 {
42 NtClose(TestTokenHandle);
44 return;
45 }
48 {
49 NtClose(TestTokenHandle);
50 ok(0, "No enough privileges to run the test (Number of privilege: %lu)!\n", Privileges->PrivilegeCount);
51 return;
52 }
53
54 /* Remove all privileges except 2nd and 3rd privileges, this should succeed */
55 PrivilegesToKeep[0] = Privileges->Privileges[1].Luid.LowPart;
56 PrivilegesToKeep[1] = Privileges->Privileges[2].Luid.LowPart;
58
59 /* Do not use NT_SUCCESS, RtlRemovePrivileges may returns STATUS_NOT_ALL_ASSIGNED */
61 {
62 NtClose(TestTokenHandle);
64 return;
65 }
66
67 /* Now, only two privileges we kept should be present */
68 Status = NtQueryInformationToken(TestTokenHandle, TokenPrivileges, Buffer, sizeof(Buffer), &ReturnLength);
70 {
71 NtClose(TestTokenHandle);
73 return;
74 }
76 "Number of privileges after RtlRemovePrivileges is %lu, expected %u\n", Privileges->PrivilegeCount,
77 ARRAYSIZE(PrivilegesToKeep));
78 ok(PrivilegesToKeep[0] + PrivilegesToKeep[1] ==
80 "Incorrect privileges kept by RtlRemovePrivileges: %lu and %lu, expected %lu and %lu",
81 Privileges->Privileges[0].Luid.LowPart, Privileges->Privileges[1].Luid.LowPart, PrivilegesToKeep[0],
82 PrivilegesToKeep[1]);
83
84 /* Remove all privileges, this should succeed */
86
87 /* Do not use NT_SUCCESS, RtlRemovePrivileges may returns STATUS_NOT_ALL_ASSIGNED */
89 {
90 NtClose(TestTokenHandle);
92 return;
93 }
94
95 /* Now, no privilege should be present */
96 Status = NtQueryInformationToken(TestTokenHandle, TokenPrivileges, Buffer, sizeof(Buffer), &ReturnLength);
98 {
99 NtClose(TestTokenHandle);
101 return;
102 }
103 ok(Privileges->PrivilegeCount == 0, "There are %lu privileges still exist after RtlRemovePrivileges\n",
104 Privileges->PrivilegeCount);
105
106 NtClose(TestTokenHandle);
107 return;
108#else
110#endif /* (NTDDI_VERSION >= NTDDI_VISTA) */
111}
_In_ PVOID _In_ ULONG _Out_ PVOID _In_ ULONG _Inout_ PULONG ReturnLength
Definition: KdSystemDebugControl.c:34
Definition: bufpool.h:45
Definition: nsiface.idl:2307
NTSYSAPI NTSTATUS NTAPI RtlRemovePrivileges(_In_ HANDLE TokenHandle, _In_reads_opt_(PrivilegeCount) _When_(PrivilegeCount !=0, _Notnull_) PULONG PrivilegesToKeep, _In_ ULONG PrivilegeCount)
Removes all privileges in the specified access token.
Definition: priv.c:515
NTSTATUS NTAPI NtOpenProcessToken(IN HANDLE ProcessHandle, IN ACCESS_MASK DesiredAccess, OUT PHANDLE TokenHandle)
Definition: security.c:350
Definition: setypes.h:73
Definition: setypes.h:1034
_Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtQueryInformationToken(_In_ HANDLE TokenHandle, _In_ TOKEN_INFORMATION_CLASS TokenInformationClass, _Out_writes_bytes_to_opt_(TokenInformationLength, *ReturnLength) PVOID TokenInformation, _In_ ULONG TokenInformationLength, _Out_ PULONG ReturnLength)
Queries a specific type of information in regard of an access token based upon the information class....
Definition: tokencls.c:473
_Must_inspect_result_ __kernel_entry NTSTATUS NTAPI NtDuplicateToken(_In_ HANDLE ExistingTokenHandle, _In_ ACCESS_MASK DesiredAccess, _In_opt_ POBJECT_ATTRIBUTES ObjectAttributes, _In_ BOOLEAN EffectiveOnly, _In_ TOKEN_TYPE TokenType, _Out_ PHANDLE NewTokenHandle)
Duplicates a token.
Definition: tokenlif.c:1871
_In_ PSECURITY_SUBJECT_CONTEXT _In_ BOOLEAN _In_ ACCESS_MASK _In_ ACCESS_MASK _Outptr_opt_ PPRIVILEGE_SET * Privileges
Definition: sefuncs.h:17
struct _TOKEN_PRIVILEGES TOKEN_PRIVILEGES
struct _TOKEN_PRIVILEGES * PTOKEN_PRIVILEGES